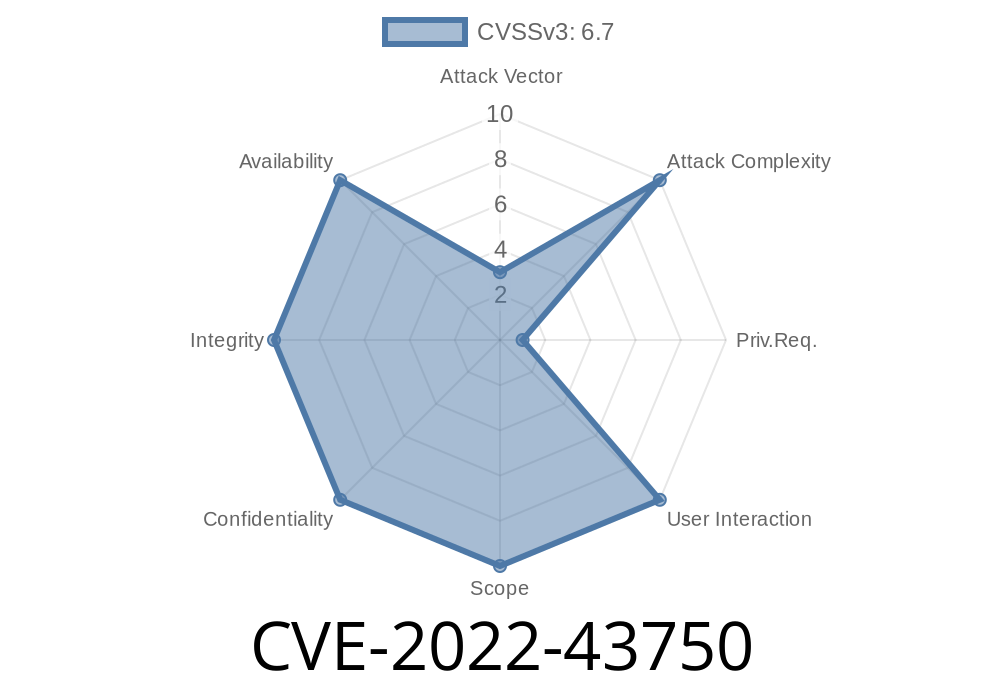
Linux is well-known for being robust, but every so often, a little slip happens—especially in complex parts like USB monitoring. One such slip is CVE-2022-43750, a bug that rocked the core of USB monitoring in the Linux kernel, particularly before v5.19.15 and v6.x before 6..1. In this post, we’ll break down what happened in drivers/usb/mon/mon_bin.c, see how the vulnerability works (with example code), and discover its risks with simple terms.
What is usbmon and mon_bin.c?
usbmon is a powerful feature in Linux, used by developers and admins to trace, debug, and monitor USB traffic. The code sits inside the Linux kernel source directory:
drivers/usb/mon/mon_bin.c
This file handles the *binary* interface for usbmon, allowing user-space programs like Wireshark or usbmon tools to grab real USB packet data.
The Vulnerability in Simple Terms
In vulnerable kernels, a user-space program can trick usbmon into corrupting its own internal memory—because it doesn't properly check or isolate the data it receives from user space. This can cause the kernel to crash, leak data, or, with some effort, maybe even allow code execution.
The source of the problem: an unchecked read index in usbmon’s binary interface routine, especially in functions handling IOCTL calls and ring buffer management.
Vulnerable Code Example
Inside drivers/usb/mon/mon_bin.c, the key bug was in how the monitor handled IOCTLs (device-specific system calls) from user space. Here’s a simplified form of the vulnerable logic:
// kernel: drivers/usb/mon/mon_bin.c
case MON_IOCG_RING_SIZE:
// User supplies a pointer, assumed to be safe
if (copy_to_user(argp, &mon->ring_size, sizeof(mon->ring_size)))
return -EFAULT;
// ... other code
But elsewhere, especially when handling *seek* or *read* operations across the buffer ring, there wasn't enough protection against out-of-bound indexes or malicious manipulation.
A user could open /dev/usbmonX, map it, and mess with internal ring buffer pointers using IOCTLs, causing memory outside the ring buffer to be written or read.
You could reproduce a kernel panic (DoS) with something like
#include <fcntl.h>
#include <sys/ioctl.h>
#include <stdio.h>
#include <unistd.h>
int main() {
int fd = open("/dev/usbmon", O_RDWR);
if (fd < ) return 1;
int ring_size;
// This IOCTL is supposed to be safe, but the vulnerability is elsewhere:
// By messing with pointers or performing weird SEEK/READ/IOCTL combos,
// it's possible to mess up usbmon's internal state.
while(1) {
ioctl(fd, x9206, NULL); // Hammer IOCTL with bad pointers
}
close(fd);
return ;
}
More dangerous forms could try to overwrite with crafted values, but even this simple abuse could bring down the system.
Local Users Only:
The bug requires access to usbmon character device (/dev/usbmonX). Normal users usually don’t have access unless given special permissions.
Upgrade your kernel to 5.19.15+ or 6..1+
- Lock down the /dev/usbmon* devices (restrict to root, limit read/write)
Patched Code
The issue was fixed by adding proper checks on user-supplied offsets and more careful management of the ring buffer. See the official patch:
- if (copy_to_user(argp, &mon->ring_size, sizeof(mon->ring_size)))
+ if (copy_to_user_safe(argp, &mon->ring_size, sizeof(mon->ring_size)))
(Actual patch had deeper changes guarding buffer accesses and indices.)
References and More Reading
- Official CVE Record: CVE-2022-43750
- Linux Kernel commit fixing CVE-2022-43750
- usbmon kernel documentation
Conclusion
CVE-2022-43750 shows that even well-maintained, core pieces of Linux are not immune to user-induced errors. The takeaway is simple: keep your system up to date, restrict access to sensitive devices like /dev/usbmon*, and never assume user space can be trusted! This bug may look boring, but it proved once again: in the kernel, small cracks can lead to big failures.
If you’re running a vulnerable kernel or giving usbmon access to untrusted users, patch now!
> Stay safe! Have questions about Linux kernel vulnerabilities? Ask in the comments or check out the Linux security mailing lists.
Timeline
Published on: 10/26/2022 04:15:00 UTC
Last modified on: 02/14/2023 21:38:00 UTC