The Linux kernel, the core of many popular operating systems, sometimes suffers from subtle but serious bugs. One such flaw is CVE-2022-44034, discovered in the PCMCIA smartcard reader (scr24x_cs) driver code. Let’s break down what this vulnerability is, how it happens, and what kind of risks and exploits it brings for systems running affected kernels.
What is CVE-2022-44034?
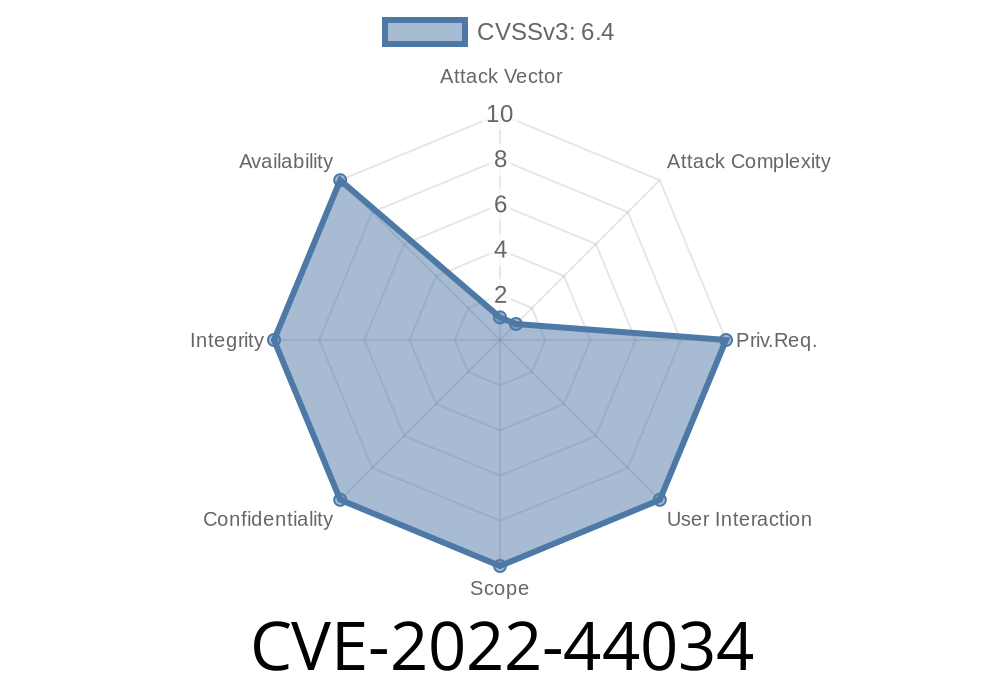
CVE-2022-44034 is a race condition problem (a timing issue) in versions of the Linux kernel up to Linux 6..6. Specifically, if someone physically removes a PCMCIA scr24x smartcard device during the process of opening it (open() system call), the driver can use memory that has already been freed—a classic “use-after-free” bug.
To be at risk, a person must have physical access to the system with the vulnerable hardware installed.
scr24x_remove() — Called when the device is physically removed (hot unplug)
A race between these two can result in scr24x_open accessing memory after scr24x_remove() has already freed it.
Here’s a simplified version of what’s going on
// Pseudo-code version of the race
int scr24x_open(struct inode *inode, struct file *filp) {
struct scr24x_dev *dev = ...; // gets pointer to device structure
// Checks device state (but what if device is removed right after this?)
if (!dev->present)
return -ENODEV;
// ... some initialization ...
filp->private_data = dev; // save pointer for later use
return ;
}
void scr24x_remove(struct pcmcia_device *p_dev) {
struct scr24x_dev *dev = pcmcia_get_drvdata(p_dev);
// Free the device structure immediately
kfree(dev);
// Now, another process could still be accessing dev!
}
If the device is unplugged (and scr24x_remove() runs) right after the initial checks in scr24x_open(), that open call will get a pointer to freed memory. Next access to that memory (like reading or writing the card) risks a *use-after-free*, which could crash the kernel, or worse, be exploited for privilege escalation.
While physical access is needed, a local attacker could
1. Start to open /dev/scr24x* (using a program, or cat for example).
2. Simultaneously *remove* the PCMCIA device during this open() (requires fast hands, or a script paired with physical remove).
The kernel tries to finish opening, but now uses the freed memory.
4. This can crash the kernel (DoS), or, with expert knowledge and timing, possibly run malicious code (exploit UAF).
System might crash, panic, or log error messages.
# In one terminal:
cat /dev/scr24x
# At the perfect moment, remove the card physically.
With a kernel debugger or fuzzer, this event is much easier to trigger reliably.
Exploitable as a Denial-of-Service (DoS) and *potentially* more with a complex payload.
Servers and desktops with these PCMCIA smartcard readers are at risk, especially in kiosks, financial systems, or locked-down terminals where cards are regularly inserted or removed.
How Was It Fixed?
The fix involves guarding the device’s memory structure using locking and checking, or defer actual freeing until all possible open instances are closed. Upgrading to the latest kernel (6..7 or newer as of this post) patches the vulnerability. Here’s a link to the patch:
https://github.com/torvalds/linux/commit/3ed012aad4f63a42be2f30f523e5f967972cd025
The patch uses synchronization and reference counting to avoid freeing the device structure too early.
References
- CVE Record — CVE-2022-44034
- Linux Kernel Patch for scr24x
- oss-security discussion
Bottom Line
While CVE-2022-44034 needs physical access, it’s a real-world reminder of how small race conditions in device driver code can lead to big issues. If you run Linux with PCMCIA smartcard readers, *update your kernel now* to stay safe!
Timeline
Published on: 10/30/2022 01:15:00 UTC
Last modified on: 11/01/2022 14:55:00 UTC