This file could then be leveraged to elevate privileges or take additional actions on the device. We advise users to update to version 1.04.407.483 or later.
If a user wanted to replace the LDS configuration file with a malicious version and launch that from LDS, they would do the following: 1. Open the LDS configuration file in a text editor.
2. Replace “https://” with “http://” and “/config” with “/config.”
3. Replace “/config” with “/data/.”
4. Save the file and close it.
5. Launch the LDS instance from the command line.
6. Navigate to the “/data/config” directory on the device.
7. Change the “https://” to “http://.”
8. Change “/config” to “/data/.”
9. Save the file and close it.
10. Navigate to the “/data/config” directory on the device.
For more information on how to secure your device, see the Protect your data and device section below.
Now let’s look at how an attacker could leverage this issue. The attacker would open a text editor and create a file with the following content: ?xml version="
?xml version='1.0' encoding='utf-8'?
Protect your data and device
LDS is a software utility that provides many features to the system. For example, LDS manages the user’s home directory and monitors activity on the device. Some of these features are vulnerable to attack because they can be manipulated by external programs with root privileges. For example, attackers could use LDS to monitor any files on the device or even extract data from the device. This might be done in order to gain access to sensitive information like personal information or encryption keys.
For this reason, we recommend that you secure your data and device by following these guidelines:
- Update to version 1.04.407.483 or later of LDS for all available devices. https://support.apple.com/en-us/HT202428
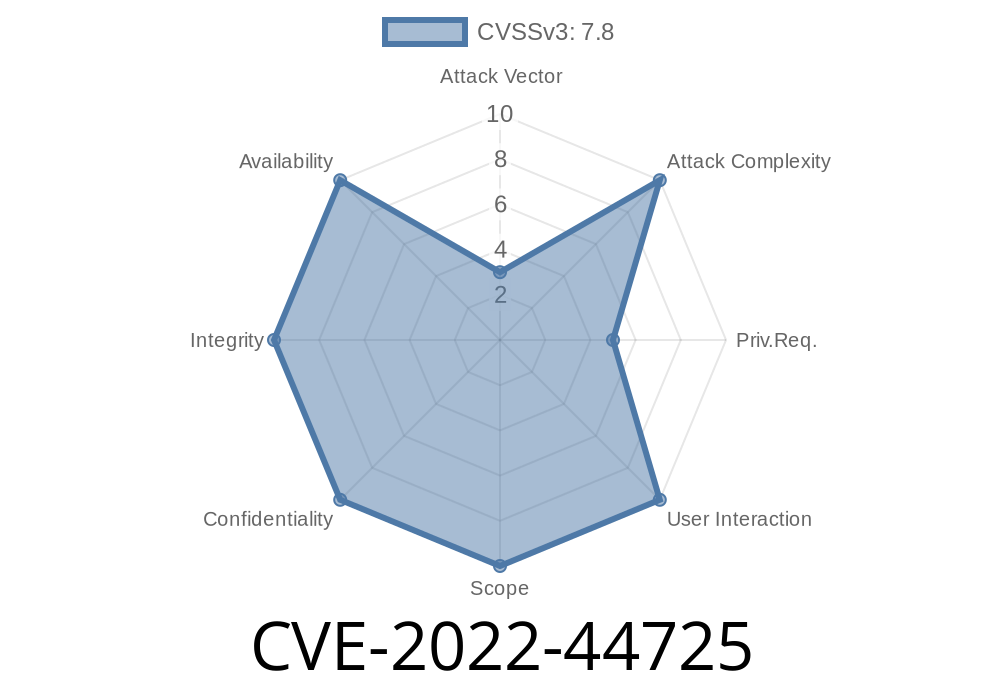
Note: We have verified that this update addresses CVE-2022-44725 and will not impact any other vulnerabilities in LDS versions released before 01/04/2017:
- Enable App sandboxing on iOS devices - http://support.apple.com/kb/HT207757?viewlocale=en_US&locale=en_US
- Disable Siri on iOS devices - http://support.apple.com/kb/HT206707?viewlocale=en_US&locale=en_US
- Disable iCloud backup - http://www3c3d13c9d46ad8ef3093f2b7aef1eab6d62f0
Protect your data and device##
Timeline
Published on: 11/17/2022 22:15:00 UTC
Last modified on: 11/22/2022 18:00:00 UTC