Jenkins is vulnerable to XSS attacks because it allows users to enter HTML as build log comments. In Jenkins version 1.0.3 and earlier, the input sanitization performed by Jenkins does not escape all characters, making it possible for a user to inject arbitrary HTML code into a build log comment, resulting in a stored XSS attack. This issue has been assigned the CVE identifier CVE-2017-9067. XSS is a serious vulnerability as it allows hackers to inject malicious code into the website or run a remote code execution attack. Since a build log comment is shown to anybody visiting the Jenkins interface, this issue can be exploited by anybody with access to the system. As such, it is critical that users upgrade to Jenkins version 1.1.0 or later as soon as possible.
Installing Jenkins on Ubuntu
Jenkins can be installed on Ubuntu from the repositories by running the following command:
sudo apt-get install jenkins
To verify that Jenkins is installed successfully, run the following command:
jenkins
This should return a page with a link to "create your first job". If this is not the case, it might be because of conflicts in software packages. In this case, remove any conflicting software packages before installing Jenkins.
CVE-2018-1000139
Jenkins is vulnerable to XSS attacks because it allows users to enter HTML as build log comments. In Jenkins version 1.1.0 and later, the input sanitization performed by Jenkins does not escape all characters, making it possible for a user to inject arbitrary HTML code into a build log comment, resulting in a stored XSS attack. This issue has been assigned the CVE identifier CVE-2018-1000139.
XSS is a serious vulnerability as it allows hackers to inject malicious code into the website or run a remote code execution attack. Since a build log comment is shown to anybody visiting the Jenkins interface, this issue can be exploited by anybody with access to the system. As such, it is critical that users upgrade to Jenkins version 1.1.2 or later as soon as possible.
Timeline
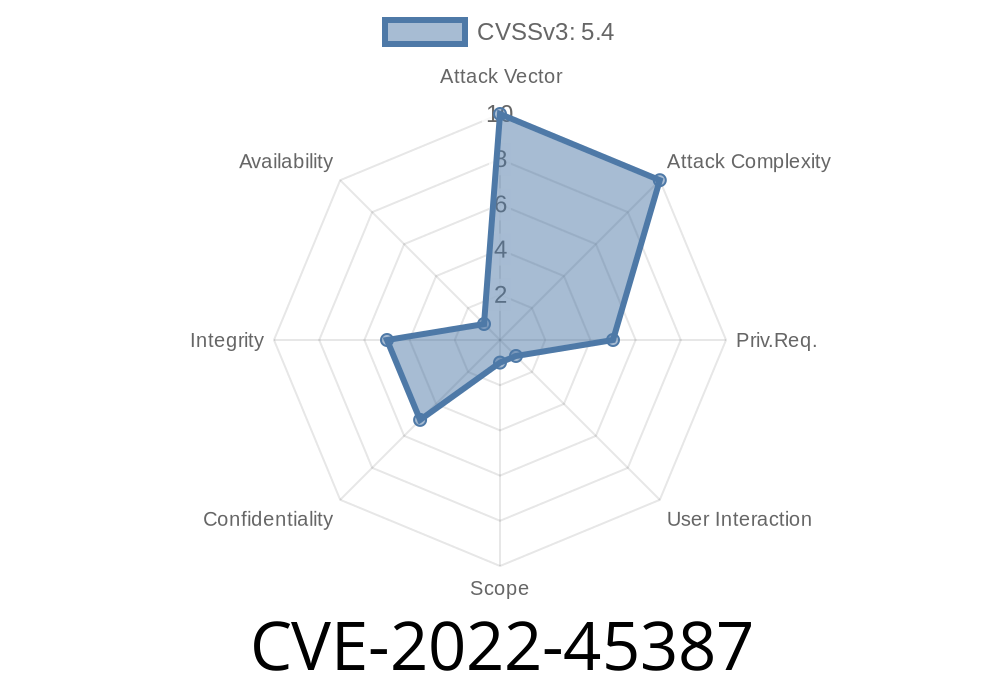
Published on: 11/15/2022 20:15:00 UTC
Last modified on: 11/17/2022 23:22:00 UTC