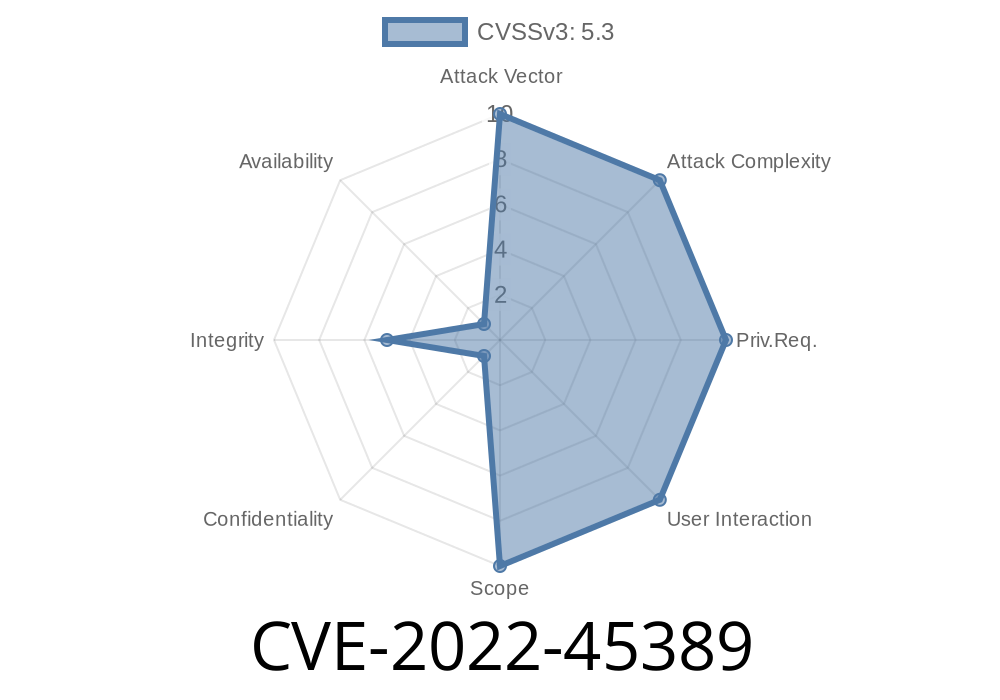
The issue is caused by a missing permission check in Jenkins XP-Dev Plugin 1.0 and earlier. When installing this plugin, an attacker could specify a new Jenkins instance that has this plugin installed. An attacker could then install the XP-Dev Plugin in a Jenkins instance that has root permissions. With the malicious Jenkins instance in place, the attacker could then push any arbitrary code to an arbitrary project on the Jenkins instance. This could then be executed in a security context, such as in a corporate network where code should be executed with permissions only in a client environment.
This issue was fixed in Jenkins 1.575 and later. If you are using an older version, we recommend updating.
Installing Jenkins on Windows
If you are installing Jenkins on Windows, the next step is to install the Java JDK.
To do this, you will need to open the Start menu and navigate to Control Panel > Programs and Features. Locate the Java JDK entry in the list of installed programs and click on it. Click on the Uninstall button under Add/Remove Programs if that option is available. Next, choose "Yes" when prompted to uninstall all components related to Java. If you then see a warning dialog box about an outdated version of Java being installed, select "Yes" again so that it can be uninstalled as well.
Next, go back to the Start menu and navigate back to Control Panel > Programs and Features. Locate Oracle JDK 8 in the list of installed programs and click on it. Click on Install next to the following options:
Java SE Development Kit (JDK) 8
JavaFX Development Kit (JFXDK) 1.8
Next, enter your administrative password when prompted for confirmation. Leave everything else unchecked and wait for installation to complete before carrying on with these instructions.
What is Jenkins XP-Dev Plugin?
The Jenkins XP-Dev Plugin let developers manage the environment that Jenkins runs in. With this plugin, they can use a debugger and IDE to debug their code or even deploy their application to an isolated environment for testing purposes. This plugin also supports remote development where multiple developers can work on the same project from different locations.
The issue is caused by a missing permission check in Jenkins XP-Dev Plugin 1.0 and earlier. When installing this plugin, an attacker could specify a new Jenkins instance that has this plugin installed. An attacker could then install the XP-Dev Plugin in a Jenkins instance that has root permissions. With the malicious Jenkins instance in place, the attacker could then push any arbitrary code to an arbitrary project on the Jenkins instance. This could then be executed in a security context, such as in a corporate network where code should be executed with permissions only in a client environment.
What is Jenkins?
Jenkins is an open source automation server. It is used to create and test automated software projects, or build pipelines for continuous integration and continuous delivery. Jenkins can be configured to run tasks like building software, testing software, and deploying applications.
Description of the XP-Dev Plugin
Jenkins is a software automation and continuous integration (CI) server. The Jenkins XP-Dev Plugin allows Jenkins to be installed as a Java application on Windows. It provides developers with a graphical interface for configuring, building, and deploying their builds.
Timeline
Published on: 11/15/2022 20:15:00 UTC
Last modified on: 11/18/2022 04:52:00 UTC