This allowed an attacker to hijack an Airflow user's session by redirecting to a malicious site, then using `airflow login` to sign in to Airflow. The attacker could then access Airflow and perform actions on behalf of the Airflow user. This issue has been fixed in Airflow 2.4.3 and later. After upgrading to a new version, you can remove the open redirect from your Airflow installation. Open your server's `/etc/apache2/sites-enabled/ directory and edit the `virtual host>` configuration file for your webserver. Find the `Directory>` line and add ` .10 - Redirect .10 / login - 302 / log > / log `. This will fix the open redirect. If you are upgrading from an old version of Airflow and the `/login` open redirect is active, you will need to delete the open redirect. In your `/etc/apache2/sites-enabled/ directory, edit the `virtual host>` configuration file for your webserver. Find the `Directory>` line and remove the ` .10 - Redirect .10 / login - 302 / log > / log ` line. Restart your webserver to apply these changes. After upgrading to a new version, you can remove the open redirect in your installation. Open your installation's `/etc/apache2/sites-enabled/ directory and edit the `virtual host>`
Issue description and analysis
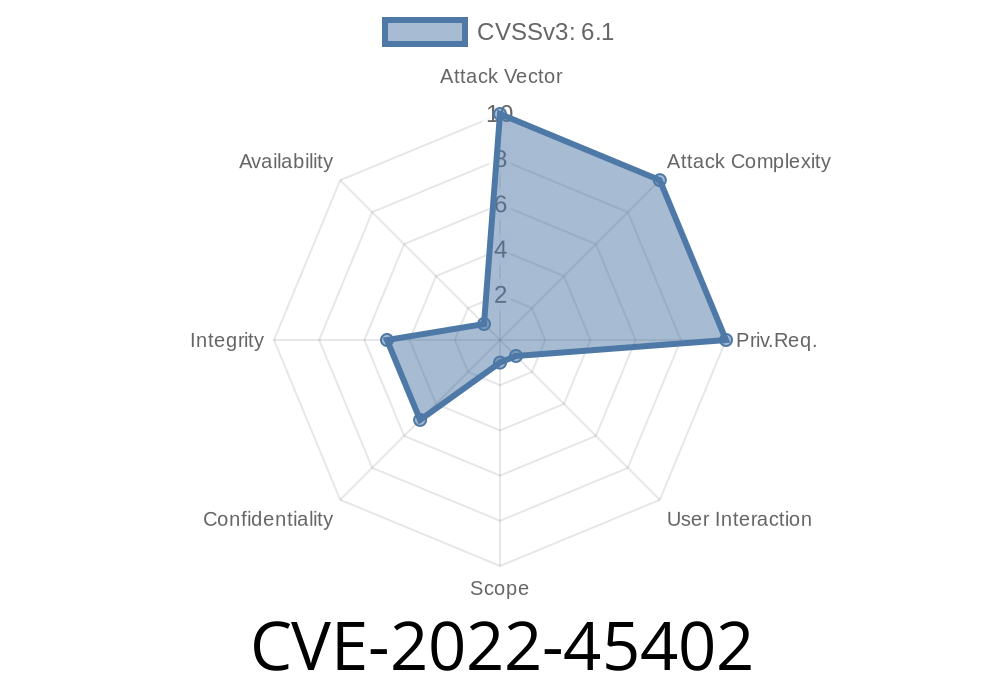
CVE-2022-45402 allowed a malicious user to hijack an Airflow users session by redirecting to a malicious site and then using `airflow login` to sign in to Airflow. The attacker could then access Airflow and perform actions on behalf of the Airflow user. This issue has been fixed in Airflow 2.4.3 and later by deleting the open redirect from your installation's `/etc/apache2/sites-enabled/ directory and editing the `virtual host>` configuration file for your webserver.
After upgrading to a new version, you can remove the open redirect from your installation's `/etc/apache2/sites-enabled/ directory and edit the `virtual host>` configuration file for your webserver. Find the `Directory>` line and add ` .10 - Redirect .10 / login - 302 / log > / log `. This will fix the open redirect if you are upgrading from an old version of Airflow or if it is active on your installation. If you're upgrading from an old version of Airflow, you'll need to delete the open redirect first by editing your installation's `/etc/apache2/sites-enabled/ directory, find the `Directory>` line, remove the ` .10 - Redirect .10 / login - 302 / log > / log ` line, restart Apache, then rerun pip install --upgrade airflow*.
How to fix the open redirect in Airflow 3.2 .x
To fix the open redirect in Airflow 3.2.x:
1) Install an earlier version of Airflow using pip or wheel.
2) Pull down all your data to a new installation running 3.2.x and make sure that the install is working before you proceed with this step.
3) In order to completely wipe out the issue, you'll need to delete the open redirect in your `/etc/apache2/sites-enabled/ directory and edit the `virtual host>` configuration file for your webserver. Find the `Directory>` line and remove the ` .10 - Redirect .10 / login - 302 / log > / log ` line. Restart your webserver to apply these changes.
Timeline
Published on: 11/15/2022 09:15:00 UTC
Last modified on: 11/17/2022 21:24:00 UTC