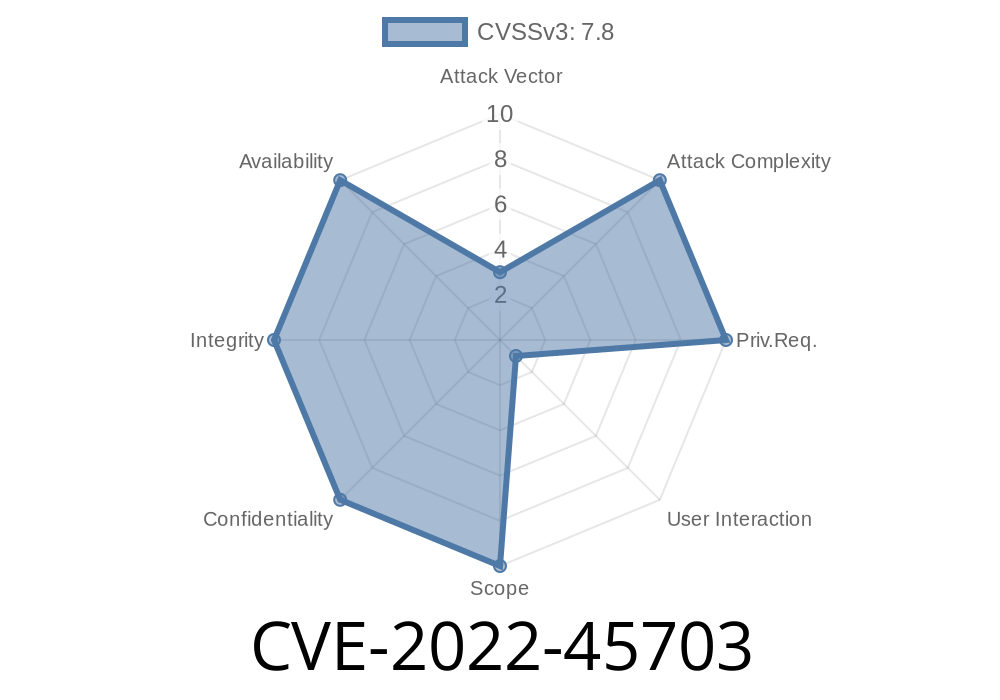
Heap buffer overflows are dangerous bugs that can let attackers crash software, leak sensitive information, or even take control of a computer. In this post, we’ll dig into CVE-2022-45703—a real heap buffer overflow found in the popular binutils tool, specifically in readelf before version 2.40. You’ll learn what went wrong, see code that’s easy to follow, and understand how the bug can be exploited. Let’s get started.
What is Readelf and Why Does It Matter?
readelf is a utility in GNU binutils that displays information about ELF (Executable and Linkable Format) files, which are used as standard executables, object code, shared libraries, and core dumps on Linux and Unix systems. If you ever debug or reverse-engineer Linux programs, you probably used readelf.
Why Care About a Tool?
Since readelf is open source and sometimes run with user-provided files, vulnerabilities in this parsing tool can be used in security research or as part of larger exploitation chains.
Resources
- NVD NIST Entry
- Binutils bug report
- Upstream fix
Technical Background and Root Cause
The problem lies in how readelf displays debug sections inside ELF files. The function display_debug_section reads data from a user-supplied debug section in the file and tries to print it out. But, the code did not check if the size of the section matches what's allocated in memory, allowing a buffer overflow on the heap.
Here’s a simplified code snippet from readelf.c (for demonstration/educational use only)
void display_debug_section (Elf_Data *data, size_t size) {
unsigned char *buf = malloc(size);
if (buf == NULL) return;
memcpy(buf, data->d_buf, data->d_size);
// ... process buffer ...
// The bug: If data->d_size > size, memcpy will overflow buf!
}
The code assumes data->d_size will not be larger than size, but this assumption fails to hold if the input ELF file provides a larger value, resulting in a classic heap buffer overflow.
Reproducing the Exploit
The easiest way to trigger this bug is to craft a malicious ELF file with a debug section that advertises a large (fake) size in the section header but contains even more bytes in the actual "data".
Example: Create a Malicious ELF (Pseudocode)
# This is pseudocode; generating a real ELF is more work.
elf_header = b'\x7fELF' + rest_of_elf_header
section_headers = setup_sections(including_debug_with_fake_size)
debug_data = b'A' * 100000 # Way bigger than what section header claims
malicious_elf = elf_header + section_headers + debug_data
with open("evil.elf", "wb") as f:
f.write(malicious_elf)
Run:
readelf -w evil.elf
This would cause readelf to heap overflow and likely crash (segfault) or, in more advanced exploits, potentially execute attacker-controlled code.
Impact
On its own, running readelf on a malicious file will usually just crash the tool (“denial of service”). That said, heap overflows can (with enough research and luck) be exploited for arbitrary code execution, opening the door to full system compromises—especially if used as part of a larger chain or in sensitive environments.
The Patch
The fix added extra checks to ensure that the buffer allocated is large enough for memcpy, and that the values used in allocation and copying are consistent.
Fixed Code
if (data->d_size > size) {
error(_("Section size too large"));
return;
}
memcpy(buf, data->d_buf, data->d_size);
// ... now safe!
Conclusion
CVE-2022-45703 is a good example of why even simple mistakes in classic C code (like mismatched size checks) can have big security consequences. If you use binutils or package tools like readelf, update to version 2.40 or newer.
For more details, check the references
- NIST NVD entry
- Binutils Bug Tracker
- Official fix commit
Stay safe! Always keep binary analysis tools up to date, and sanitize all input—even files that “shouldn’t” be dangerous.
*This post is for educational purposes only. Never use vulnerabilities to attack systems you don’t own or have permission to test.*
Timeline
Published on: 08/22/2023 19:16:30 UTC
Last modified on: 10/06/2023 15:15:13 UTC