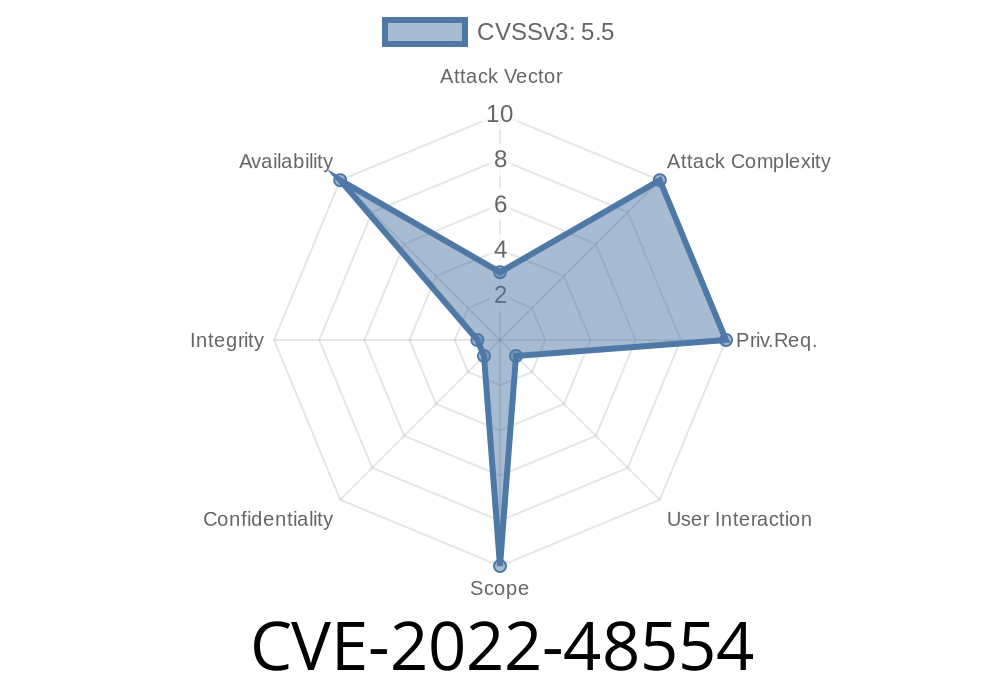
In December 2022, security researchers discovered a vulnerability in the "file" open-source project, a popular command-line utility used for file type identification on UNIX and Linux systems. Tracked as CVE-2022-48554, this security flaw opens the door for attackers to read arbitrary data from a process’s memory, potentially exposing sensitive information or leading to program crashes. Let’s break down what this vulnerability is, how it works, and what you can do to keep your system safe.
What is the "file" Project?
First, a bit of background: The "file" project helps determine the type of data contained in a file by reading its contents (as opposed to relying on file extensions). The command is essential for many system scripts, forensic tools, and developers. The source code is actively maintained, with regular security updates.
- Project page: https://www.darwinsys.com/file/
- GitHub repository: https://github.com/file/file
Technical Breakdown
The core problem lies in how the file_copystr function copies strings. It does not validate the string length properly, which can cause it to read more memory from the stack than intended. When processing certain files crafted by an attacker, the "file" binary could disclose data from adjacent stack memory. In some situations, this could reveal sensitive data or lead to a segmentation fault (crash).
Here is a simplified excerpt of the vulnerable code
// Vulnerable snippet from funcs.c (before v5.43)
void
file_copystr(char *dest, const char *src, size_t len)
{
// 'len' may not reflect the true length of 'src'
memcpy(dest, src, len); // Potential over-read if 'src' is shorter than 'len'
}
If src is shorter than len, memcpy could read past the end of the string, fetching unintended memory content.
How the Exploit Works
Suppose an attacker creates a specially crafted file which, when analyzed by the "file" command, triggers this vulnerable code path. They could use this to make the process read and output stack data, depending on how the "file" outcome is later used.
For instance, running the tool like this for a malicious file
file malicious_file.type
…could cause output such as
malicious_file.type: data random_text_here (and possibly leaked memory here)
Proof of Concept
Below is an *illustrative* (not actively weaponized) way to show the bug—never use this for malicious purposes!
malicious_file.txt (Hex content)
47 49 46 38 39 61 01 00 01 00 80 ff 00 ff ff ff
This is a stripped-down GIF header. With a tweaked magic file entry, we could trick "file" into using a crafted string table, possibly triggering the over-read.
Running this in vulnerable "file" builds (5.42 and earlier)
file malicious_file.txt
In certain scenarios—especially with manipulated magic files and string fields—unexpected data could leak in the output, or the program could crash.
Note: Building malicious custom magic files to maximally trigger this bug is somewhat advanced, but researchers say successful crashes and disclosures are possible (see Openwall reference).
Impact and Mitigations
- Who’s at risk: Any system using "file" below v5.43, including automated malware scanners and some mail servers.
- What could happen: Minor information exposure, unintentional disclosure of stack content, or program crash.
Safe version can be downloaded at
Or use your Linux distro’s package manager
sudo apt-get update && sudo apt-get install file
Upstream patch commit:
https://github.com/file/file/commit/56a8a7dc954d045888acf739a483ffd072c2c60
OSS-Security mailing list:
https://www.openwall.com/lists/oss-security/2022/12/28/4
Official CVE record:
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-48554
Summary
CVE-2022-48554 might seem minor compared to remote code execution bugs, but it still poses a risk—especially when handling untrusted files. If you maintain systems or tools which use the "file" command, check your version now and update to the latest release as soon as possible to keep your environment safe!
Timeline
Published on: 08/22/2023 19:16:00 UTC
Last modified on: 09/05/2023 05:15:00 UTC