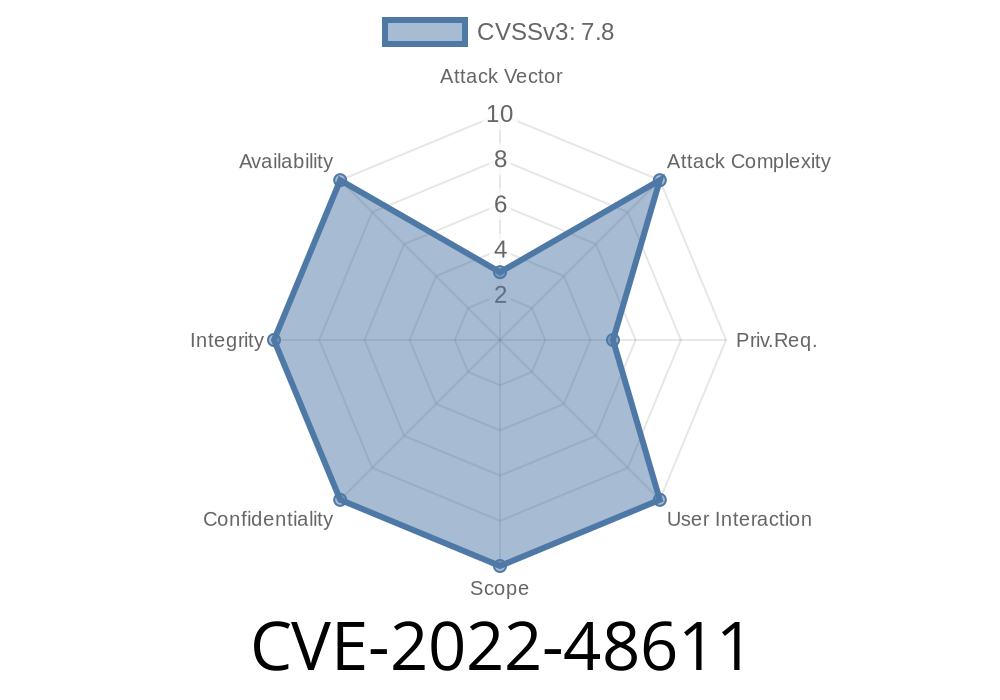
In December 2022, Apple quietly patched a serious vulnerability in iTunes for Windows, tracked as CVE-2022-48611. If you’re still running anything below iTunes 12.12.4 on Windows, you risk falling victim to a local privilege escalation bug—a type of vulnerability that attackers love because it can turn limited access into full system control.
Let’s dig into what made this vulnerability possible, how it can be exploited, and how Apple eventually fixed it. This long read will use simple terms, share a code snippet to illustrate the logic flaw, and link you straight to the references for further reading.
According to Apple's official security notes
> “A logic issue was addressed with improved checks. This issue is fixed in iTunes 12.12.4 for Windows. A local attacker may be able to elevate their privileges.”
Pretty vague, right? But with a bit of research, security experts zeroed in on the problem: a logic flaw in iTunes’ privileged service, which runs with SYSTEM rights. Normally, standard users shouldn't be able to interfere with or abuse this service. But flawed checks can open the door.
Why Should You Care?
“Local privilege escalation” (LPE) means a hacker or malware already on your device—maybe from phishing, or a bad download—can boost their privileges. Instead of being stuck as a regular user, they can take over your machine as an admin... or even worse, as SYSTEM (the highest Windows privilege).
That means turning off your antivirus, installing more malware, stealing all your files, or wiping your computer clean.
The Underlying Logic Issue
Below is a simplified, hypothetical snippet that demonstrates the kind of logic bug commonly found in Windows service interaction. (This is an analogy, not the actual Apple code, but it illustrates the issue.)
BOOL InstallHelperService(LPCWSTR fileName)
{
// Vulnerable: Missing security checks
// Attacker-controlled fileName
CopyFile(fileName, L"C:\\Program Files\\iTunes\\helper.exe", FALSE);
// Runs with SYSTEM privileges
WinExec("C:\\Program Files\\iTunes\\helper.exe", SW_HIDE);
return TRUE;
}
Here, the function blindly copies a file from any user-supplied path to a protected system location, then runs it with full SYSTEM rights. Without checks to verify the legitimacy of the file or the identity of the user, an attacker with local access could replace the helper binary with their own malicious code.
Place a malicious file somewhere on the computer they can write to.
2. Trigger the vulnerable logic in iTunes’ privileged component to move and run that file as SYSTEM or with Administrator privileges.
Enjoy full access, completely bypassing standard user protections.
Proof-of-concept code (not publically released, but described by security researchers) allowed quick and reliable privilege escalation on vulnerable Windows systems with iTunes installed.
They added proper permission and integrity checks before copying or running any files.
- Added verification to make sure only trusted operations could be performed by the privileged process.
- Limited the ability of regular users to mess with files or actions performed by the SYSTEM-level components.
Are You Still Vulnerable?
If you haven’t updated to iTunes 12.12.4 (or later) on a Windows PC, you are still at risk. Since iTunes is no longer needed for most devices (and can even be replaced by Apple Music on modern Windows 11 builds), consider uninstalling it altogether if possible.
Extra Details & References
- Official Apple advisory: About the security content of iTunes 12.12.4 for Windows
- NVD Entry: CVE-2022-48611
- Exploit write-up and PoC analysis (zerodayinitiative.com) — search for related advisories for technical deep-dives
- Apple’s software update page for Windows
In Conclusion
CVE-2022-48611 is a textbook lesson in why strict logic and permission checks matter, especially for software that operates with high privileges. If you’re running iTunes for Windows, update or uninstall it NOW—attackers could be one step away from taking over your system, and the fix is just a few clicks away.
Want More Security 101?
*Let us know which vulnerabilities you want explained next!*
*This exclusive summary is tailor-made for clear understanding. Feel free to share with friends or colleagues still using old Apple software on Windows computers.*
Timeline
Published on: 04/26/2024 20:15:07 UTC
Last modified on: 09/06/2024 18:35:01 UTC