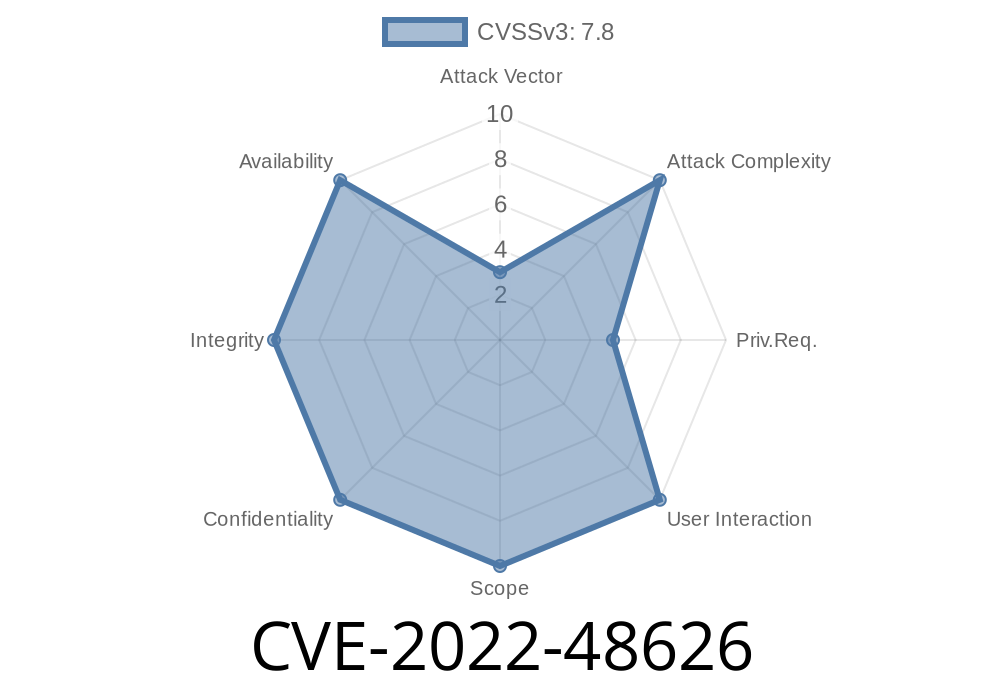
In late 2022, security researchers and Linux kernel maintainers identified and fixed a significant vulnerability in the Linux kernel, tagged as CVE-2022-48626. This flaw, discovered in the moxart MMC driver, carried the potential for severe impacts, such as the kernel crashing or — in certain exploitation scenarios — allowing attackers to escalate privileges. In this post, we’ll break down the vulnerability, help you understand how the exploit works, and show how it was fixed in simple terms.
What is CVE-2022-48626?
CVE-2022-48626 focuses on the moxart Multimedia Card (MMC) host driver within the Linux kernel. This driver manages connections to MMC/SD cards on hardware platforms using the MOXART SoC.
The vulnerability? A use-after-free bug. In software development, this means that the program tried to use memory after it had already been freed — which is a dangerous situation. Bad actors can sometimes exploit such issues to execute arbitrary code in kernel space.
Understanding the Core Problem
When the moxart MMC driver is removed (for example, when the device is unplugged or during shutdown), the function moxart_remove() is called. Inside this function, the code would *free* a chunk of memory (the MMC host structure), but then later try to access it by following a pointer that was now dangling — pointing to invalid memory.
The Old Vulnerable Code
static int moxart_remove(struct platform_device *pdev) {
struct moxart_host *host = platform_get_drvdata(pdev);
struct mmc_host *mmc = host->mmc;
mmc_remove_host(mmc);
// Freeing mmc structure
mmc_free_host(mmc);
// Oops! Accessing freed memory via 'host'
writel(, host->base); // host->base is now invalid!
return ;
}
In the old code, after freeing mmc (and by extension, host), the code tried to write to the device’s base register via host->base. But since host was just freed, this is dangerous: anything can go wrong, from kernel panics to security holes.
The Patch (Fixed Code)
The fix was straightforward: cache the base register pointer before freeing the host/memory.
static int moxart_remove(struct platform_device *pdev) {
struct moxart_host *host = platform_get_drvdata(pdev);
struct mmc_host *mmc = host->mmc;
void __iomem *base = host->base; // store pointer before free
mmc_remove_host(mmc);
mmc_free_host(mmc);
// Safe: use the cached pointer, not the freed struct
writel(, base);
return ;
}
This change ensures you’re not following dead memory. Instead, you keep a copy of what you needed and safely finish cleanup.
Exploit Details: How Could This Be Attacked?
If a malicious actor can trigger the remove routine at the right time, and then cause memory reuse, they could theoretically:
- Crash the Kernel: If the host pointer was pointing to memory that’s now garbage or used elsewhere, writing to that address could panic the system.
- Privilege Escalation: If they can allocate and control the memory reused at the host’s location, it might be possible to get the kernel to write to an attacker-controlled address — potentially a step towards arbitrary code execution.
Triggering such a condition in real life would require detailed knowledge of system internals, timing, and in most scenarios already some sort of local access, but it’s definitely not outside the realm of possibility. The main worry always is that every use-after-free bug may become a stepping-stone in a bigger attack chain.
Real-World Impact & Versions Affected
This bug specifically affects Linux systems using devices with the moxart MMC driver — that’s mostly some embedded systems and development boards using the MOXART SoC. If you don’t use this hardware or the driver isn’t loaded, you’re not affected.
The bug was fixed in the mainline Linux kernel as of version 6.2-rc1 and various stable updates. It’s good practice to always keep your kernel up-to-date, as similar patterns frequently cause other bugs.
References & More Reading
- The Patch: git.kernel.org commit
- CVE Page: CVE-2022-48626 at MITRE
- Linux Kernel changelog
- Understanding Use-After-Free Vulnerabilities
Conclusion: Lessons Learned
CVE-2022-48626 is a story about the importance of proper memory management — especially in kernel code, where mistakes can have big consequences. The fix here was simple, but the key is catching these issues before attackers do. As always, update your systems, especially if you run hardware with lesser-known drivers, and keep an eye on kernel security advisories.
If you’re a developer, remember: Don’t use memory after you free it — ever. Cache what you need, and always clean up safely.
Timeline
Published on: 02/26/2024 16:27:45 UTC
Last modified on: 04/17/2024 19:28:53 UTC