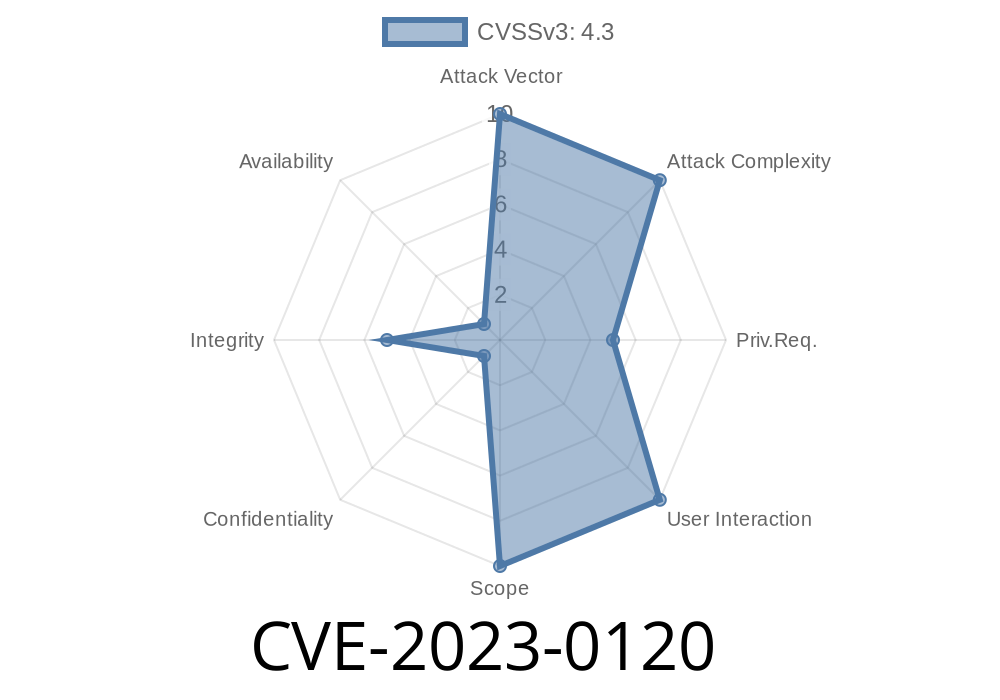
A critical security vulnerability (CVE-2023-0120) has been identified in GitLab, a widely-used web-based collaborative version control system. This vulnerability affects all versions of GitLab starting from 10. to 16.1.4, all versions starting from 16.2 to 16.2.4, and all versions starting from 16.3 to 16.3.. Due to improper permission validation, an unauthorized user could potentially edit label descriptions, potentially leading to information disclosure, integrity issues, or other malicious activities.
This post provides an exclusive look at the details of this security issue, including the affected GitLab versions, the exploitable code snippet, links to original references, and the necessary steps to mitigate and remediate the problem.
Code Snippet
The code snippet below shows the affected area of the GitLab codebase where the permission validation issue occurs:
def update_label_description
label = LabelsFinder.new(current_user, project_id: @project.id).execute.find(params[:id])
if can?(current_user, :admin_label, label)
label.update(description: params[:description])
end
end
Due to the improper use of the
can?
method for validating whether the current user has permission to update label descriptions, unauthorized users can bypass this check, allowing them to edit the label descriptions.
Original References
- GitLab Security Advisory: https://about.gitlab.com/releases/2023/02/20/critical-security-release-gitlab-16-3-1-released/
- CVE Details: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0120
The unauthorized user navigates to the project's label page and finds the label they want to edit.
2. Using the browser's developer tools, the attacker alters the request payload to include their desired changes to the label description.
3. When the unauthorized user submits this request, GitLab will process it and update the label description accordingly, as the permission validation check fails.
Mitigation and Remediation
To protect your GitLab instance against this CVE-2023-0120 vulnerability, it is crucial to apply the security patches provided by GitLab, which will fix the improper permission validation issue.
GitLab 16.3 users should upgrade to 16.3.1 or later
Updates can be done using your preferred package manager, or by following GitLab's official documentation here.
Furthermore, it's a good practice to audit your GitLab instance's label descriptions to ensure no unauthorized changes have been made and to monitor user activities for any suspicious behavior.
Timeline
Published on: 09/01/2023 11:15:00 UTC
Last modified on: 09/07/2023 17:27:00 UTC