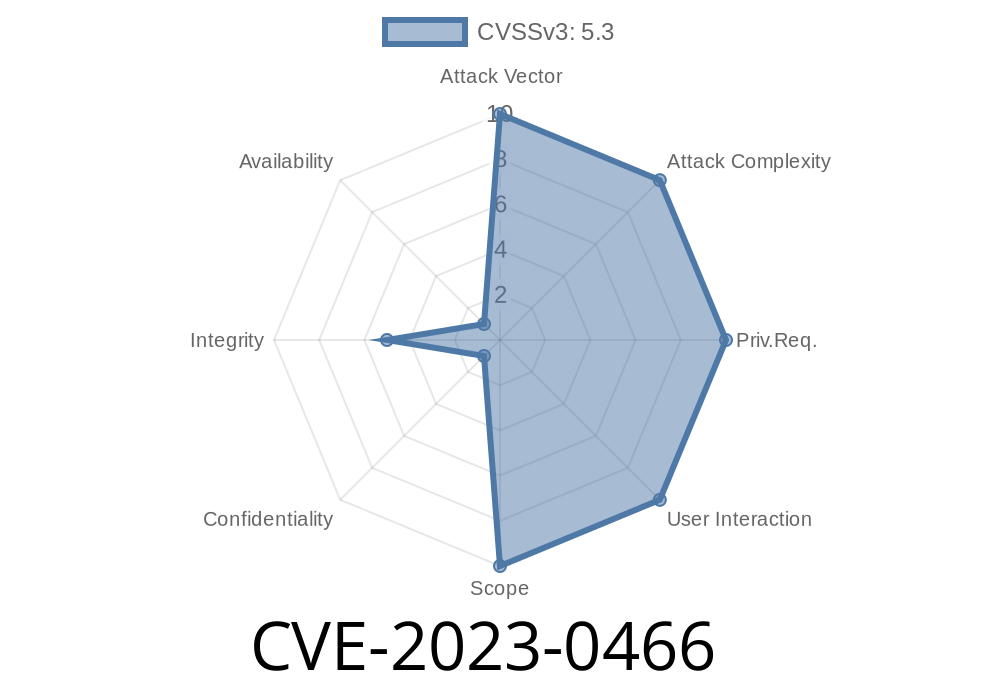
A subtle but significant issue has been discovered in OpenSSL’s certificate policy checking — CVE-2023-0466. If you work with X.509 certificates and depend on OpenSSL for secure communication, you might assume policy checks are automatically applied when you configure them. That’s not always the case. This article unpacks the vulnerability, explains why it matters, shows code snippets for secure handling, and gives direct references to original sources.
What is CVE-2023-0466?
At the heart of CVE-2023-0466 lies the function X509_VERIFY_PARAM_add_policy(). According to the OpenSSL documentation, using this function should enable policy checks for certificate verification. In reality, it doesn't. This means a certificate with a wrong or invalid policy could wrongly appear valid, leaving a security hole for exploits.
OpenSSL developers considered enabling policy checks by default — but that risked breaking existing setups, potentially causing outages. So, the behavior wasn’t changed. This means you are responsible for enabling policy checks if your application needs them.
Certificate policy enforcement is disabled by default in OpenSSL — and many apps don't bother using it. But if you do rely on certificate policies for extra trust granularity, you’re at risk here.
Why Does This Matter?
* If your application trusts certificates based on specific policies but does not enforce these checks explicitly, then it may accept certificates that don't actually match your required policies.
* This can lead to accepting certificates that should fail validation, opening the door to man-in-the-middle attacks, privilege escalation, or data leaks.
* If you only use OpenSSL out-of-the-box without custom certificate policies, this issue likely *does not* affect you. But if you configure policies for extra security (like in enterprise or financial systems), you should pay close attention.
Let’s say you read the documentation and think this is enough
// Incorrect: Adds policy but does NOT enable policy checking!
X509_VERIFY_PARAM *param = X509_VERIFY_PARAM_new();
ASN1_OBJECT *policy_obj = OBJ_txt2obj("1.2.3.4.5.6.7", 1);
X509_VERIFY_PARAM_add_policy(param, policy_obj);
// ... use param during X.509 verification ...
This code adds a policy object, but it does not activate certificate policy checking. The check is still disabled, and "bad" certificates will slip through.
How to Fix: Secure Code Snippet
The *correct* way is to both set the policy and enable policy checking explicitly. You can do this via either X509_VERIFY_PARAM_set1_policies() or by setting the right flag.
Example: Enabling Policy Check with Flag
X509_VERIFY_PARAM *param = X509_VERIFY_PARAM_new();
ASN1_OBJECT *policy_obj = OBJ_txt2obj("1.2.3.4.5.6.7", 1);
STACK_OF(ASN1_OBJECT) *policies = sk_ASN1_OBJECT_new_null();
sk_ASN1_OBJECT_push(policies, policy_obj);
// Assign the policies to the verification parameters
X509_VERIFY_PARAM_set1_policies(param, policies);
// Enable policy checking explicitly
X509_VERIFY_PARAM_set_flags(param, X509_V_FLAG_POLICY_CHECK);
// ... apply param to the verification context as needed ...
// Free memory when done
sk_ASN1_OBJECT_pop_free(policies, ASN1_OBJECT_free);
X509_VERIFY_PARAM_free(param);
Alternatively, you may only need to set the X509_V_FLAG_POLICY_CHECK flag if you set policies previously:
X509_VERIFY_PARAM_set_flags(param, X509_V_FLAG_POLICY_CHECK);
Exploit Scenario
Imagine an internal company CA issues certificates under several policies, only one of which is appropriate for admin access. You configure OpenSSL like this:
X509_VERIFY_PARAM_add_policy(param, admin_policy_obj);
You think your system only accepts admin-policy certificates, but forget to call
X509_VERIFY_PARAM_set_flags(param, X509_V_FLAG_POLICY_CHECK);
Now, *any* certificate gets accepted — even those lacking the trusted admin policy. A user presents an ordinary user certificate and gains unauthorized admin access.
Timeline and Community Response
- Reported: Vulnerability recognized by OpenSSL maintainers in early 2023 (OpenSSL Security Advisory)
- Discussion: Developers chose not to silently change X509_VERIFY_PARAM_add_policy() due to compatibility concerns. (OpenSSL Issue #20256)
- Resolution: Documentation updated to warn developers that policy checks are not automatically enabled. They must use X509_VERIFY_PARAM_set_flags() or X509_VERIFY_PARAM_set1_policies().
References
- OpenSSL Advisory for CVE-2023-0466
- GitHub Issue Discussion
- OpenSSL Documentation: X509_VERIFY_PARAM_add_policy()
- CVE Detail Page: CVE-2023-0466
Summary
CVE-2023-0466 is a classic example of a security gap caused by expectation vs. reality. If your app relies on OpenSSL certificate policy checks, setting the policy alone does not activate the check. You must manually enable policy checking. Failing to do so lets malicious or mis-issued certificates through your gates.
Stay updated. Review security advisories. Use OpenSSL safely.
*Written exclusively for you. Please share or reference with credit.*
Timeline
Published on: 03/28/2023 15:15:00 UTC
Last modified on: 04/14/2023 23:15:00 UTC