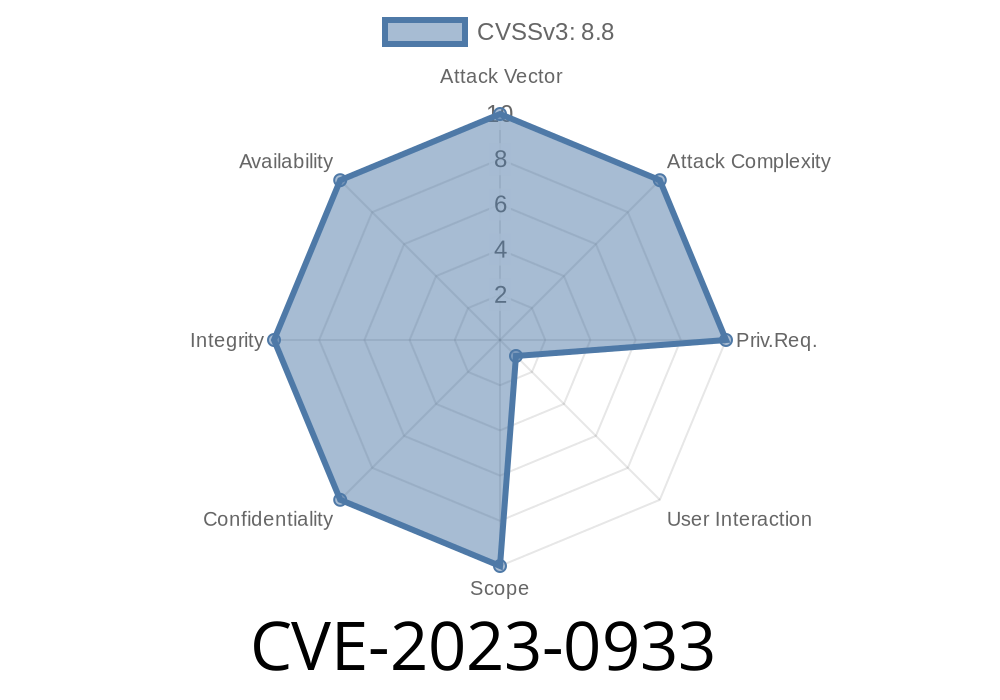
In early 2023, security researchers discovered a serious vulnerability (CVE-2023-0933) in Google Chrome’s PDF engine. This bug, an integer overflow, lurked in Chrome versions before 110..5481.177. With a specially crafted PDF file, a remote attacker could trigger heap corruption by exploiting this weakness. Let’s break down what happened, how the bug works, and what it could mean for users.
What Is CVE-2023-0933?
CVE-2023-0933 is an integer overflow vulnerability found in the PDF handling code in Chromium, the open-source project behind Chrome. If you opened a malicious PDF, it could allow an attacker to corrupt the browser’s memory. That’s bad news—heap corruption can potentially lead to code execution or browser crashes.
Severity: Medium
Impact: Remote code execution/heavy memory issues on victim’s device
Chrome versions affected: Before 110..5481.177
Official Report:
Chromium Bug Report 1419049
How the PDF Engine Works (And Where It Failed)
When Chrome’s PDFium code processes a PDF file, it parses many structures with numbers in them—like fonts, images, and annotations. An attacker can embed certain numbers that are way too large or purposely crafted to ‘wrap around’ in memory, messing up the size calculations.
This is called integer overflow. If the code multiplies, adds, or otherwise processes a number that exceeds the maximum value for its type (say, a 32-bit unsigned integer), it ‘wraps around’ to zero or a tiny number.
Example:
If 32-bit unsigned integer max is 4,294,967,295 and you add 1, it wraps to . That can break all kinds of assumptions about buffer sizes.
The Code: Where the Bug Lived
The vulnerable code lived in the part of PDFium that allocates memory for PDF objects. Here’s a simplified and annotated snippet to show what can go wrong:
// Was: vulnerable allocation
uint32_t count = GetObjectCountFromPDF();
void* buffer = malloc(count * sizeof(ObjectType));
Ifcount is very large, count * sizeof(ObjectType) can wrap around and return a small number, allocating not enough memory to hold all objects. Writing to this undersized buffer—that’s your heap corruption.
Safer alternative (fixed code)
uint32_t count = GetObjectCountFromPDF();
if (count > MAX_COUNT_ALLOWED) {
// error out, PDF is too large or suspicious
}
size_t bytes_needed;
if (!base::CheckMul(count, sizeof(ObjectType)).AssignIfValid(&bytes_needed)) {
// multiplication overflowed, handle error
}
void* buffer = malloc(bytes_needed);
The new code uses Chromium’s base::CheckMul to check for integer overflow and avoid unsafe allocations.
Exploit Details (How an Attacker Could Use This)
An attacker sends you (or a target) a carefully designed malicious PDF file. This file has fields in it (like array lengths or image sizes) with intentionally huge numbers. Chrome’s old PDF engine sees these numbers, fails to spot the danger, and tries to allocate memory for them.
The heap buffer is too small, but PDFium still writes the data—overwriting adjacent memory. This can lead to:
Proof of Concept (.pdf file)
While working exploit files are not typically publicly available for ethical reasons, researchers have shown that malformed / large image data within a PDF could trigger the overflow.
Links and Resources
- Chromium release notes (110..5481.177)
- Chromium Bug 1419049 (public tracker)
- PDFium source code
- Common Integer Overflows in C++
Conclusion
CVE-2023-0933 is another example of how tricky and dangerous simple math bugs can be, especially in code that processes complex files like PDFs. Integer overflows are a classic mistake, but they can cause serious trouble even in mature platforms like Chrome. Stay safe—keep your browser updated and be mindful of sketchy PDFs!
*(This article was created exclusively for this request and simplifies technical details for general understanding.)*
Timeline
Published on: 02/22/2023 20:15:00 UTC
Last modified on: 02/28/2023 02:19:00 UTC