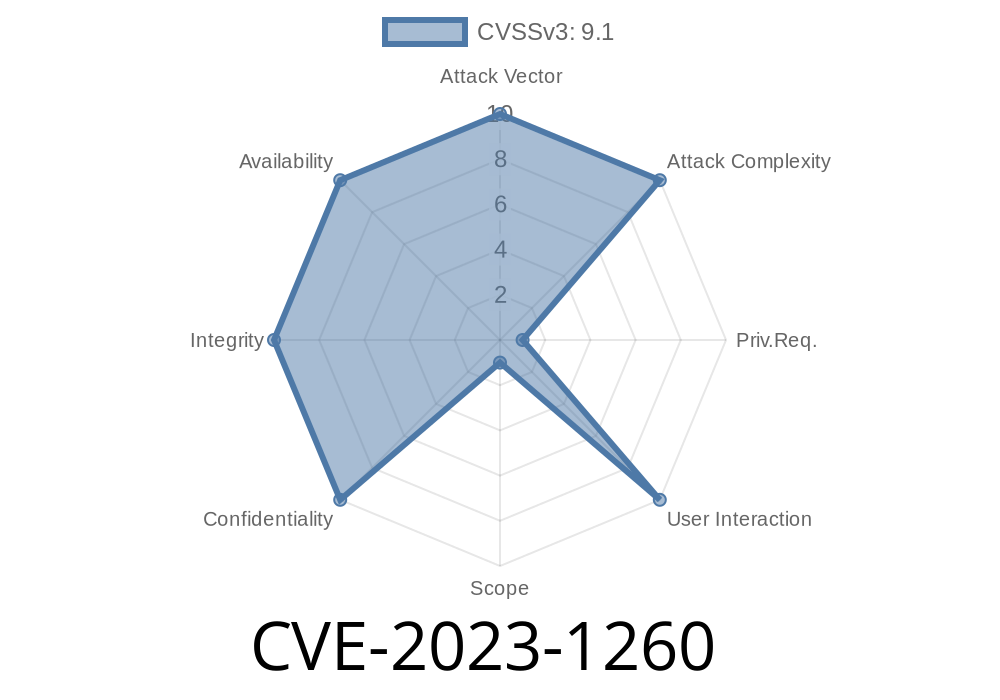
A critical vulnerability classified as CVE-2023-1260 has been identified in kube-apiserver, the core component of the Kubernetes control plane. This authentication bypass vulnerability could potentially allow a remote, authenticated attacker to escalate their privileges and gain control over a privileged pod by evading Security Context Constraints (SCC) admission restrictions. This article delves into the details of the vulnerability, its exploit, and ways to mitigate it.
Vulnerability Details
The CVE-2023-1260 vulnerability exists due to improper validation of permissions in kube-apiserver when dealing with the "pods/ephemeralcontainers" subresource. To exploit this vulnerability, an attacker needs to have been granted "update" and "patch" permissions on this subresource, which is beyond the default permissions provided.
Once these permissions are acquired, the attacker can either create a new pod or patch an existing one they already have access to. This can lead to privilege escalation, allowing the attacker to gain control over a privileged pod and potentially compromise the entire cluster.
Code Snippet
A sample code snippet that demonstrates the exploitation of this vulnerability is provided below.
# Attacker obtains "update" and "patch" permissions on "pods/ephemeralcontainers" subresource
kubectl create role pod-escalator --verb=update,patch --resource=pods/ephemeralcontainers
kubectl create rolebinding pod-escalator-binding --role=pod-escalator --user=attacker
# Attacker creates or patches a pod with elevated privileges
apiVersion: v1
kind: Pod
metadata:
name: vulnerable-pod
spec:
containers:
- name: container-1
image: "nginx:latest"
securityContext:
runAsUser: # Run as root user
privileged: true # Set privileged flag
By exploiting this vulnerability, the attacker has successfully created a privileged pod running as the root user, thereby bypassing the SCC admission controls.
For more information on this vulnerability, please refer to the following original sources
1. Kubernetes GitHub Issue
2. CVE-2023-1260 - NIST National Vulnerability Database
3. Kubernetes Security Blog Post
Kubernetes v1.22: Upgrade to v1.22.1 or later
2. Regularly audit and review the permissions granted to users and service accounts in your cluster to ensure that they are granted the least privileges required to perform their tasks. This includes paying close attention to any elevated permissions on the "pods/ephemeralcontainers" subresource.
By taking these steps, you can minimize the risk of attackers exploiting the CVE-2023-1260 vulnerability and protect your Kubernetes environment from potential security breaches.
Timeline
Published on: 09/24/2023 01:15:00 UTC
Last modified on: 10/20/2023 15:15:00 UTC