In early 2023, a serious security flaw was discovered in Google Chrome, one of the world’s most popular web browsers. Known as CVE-2023-1528, this bug was found in the way Chrome managed passwords before version 111..5563.110. What made this issue stand out was its “use-after-free” bug in the password management logic of the browser, which could allow a remote attacker—someone who had already managed to compromise the renderer process—to further abuse Chrome and potentially run dangerous code or steal sensitive data. Let’s break down what this means, how attackers could exploit it, and what it means for Chrome users and developers.
What is a Use-After-Free Bug?
A use-after-free vulnerability happens when a program “frees” (deletes) a memory area but then tries to use it later. In the chaos of modern browsers, where multiple things happen at once, this kind of bug can let hackers mess with memory—sometimes letting them run their own malicious code.
When this happens in a sensitive part of a browser—like the password manager—it raises the stakes dramatically. Since browsers sit between us and the web, any bug here can let attackers access personal info, logins, or worse.
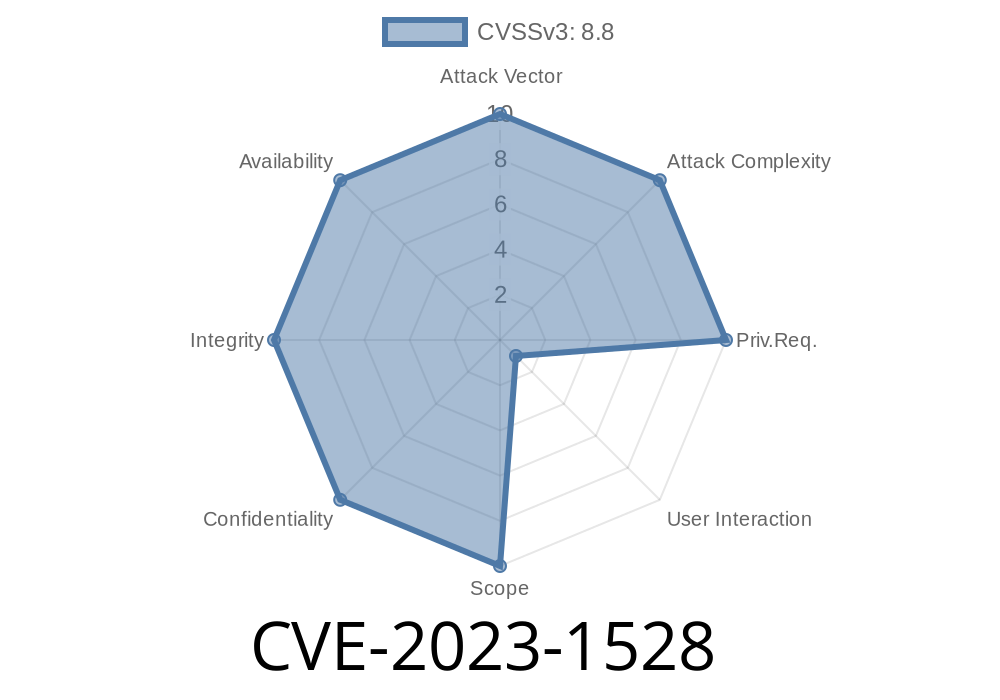
Type: Use-after-free (heap corruption)
- Attack remote vector: Requires prior compromise of the renderer process (via another vulnerability or malicious website), then uses a crafted HTML page to trigger the bug
Google’s official release note:
Stable Channel Update for Desktop
CVE Details:
Chromium Bugtracker (may be restricted):
How Did the Bug Work?
The problem lived inside the logic for managing saved passwords. If a web page could trick Chrome into freeing a specific object in memory, and then trigger a browser action that reused that already-freed area of memory, things could go wrong in several ways:
The browser could crash (Denial of Service).
- A skilled attacker could abuse the memory corruption to inject their own code into Chrome’s process (Remote Code Execution).
Example Scenario
1. Attacker lures the user to a malicious website that exploits a different vulnerability to break out of the website’s isolated sandbox—gaining code execution in the renderer process.
2. Their malicious site triggers the use-after-free bug, caused by how the Passwords component handled lifecycle events (like filling a login form, showing/hiding prompts, etc).
3. Heap corruption happens, which the attacker can then try to exploit further—to gain access to sensitive data or even escalate their access within the browser.
Simplified Exploit Example
Here's a *theoretical* Python example using Selenium that shows how an attacker might approach fuzzing for use-after-free bugs by repeatedly accessing and freeing password-related DOM elements.
> Warning: This code is for educational purposes only.
from selenium import webdriver
from selenium.webdriver.common.by import By
import time
# Start Chrome (make sure to use an old, vulnerable version—never do this outside a lab!)
options = webdriver.ChromeOptions()
options.add_argument('--disable-blink-features=AutomationControlled')
driver = webdriver.Chrome(options=options)
driver.get('http://localhost/fake_password_form.html';)
for i in range(100):
try:
# Simulates filling and removing elements rapidly
password_field = driver.find_element(By.ID, 'password')
password_field.send_keys('test_password')
driver.execute_script('document.getElementById("password").remove();')
time.sleep(.01)
# Simulate re-inserting password field
driver.execute_script('''
let input = document.createElement('input');
input.type = 'password';
input.id = 'password';
document.body.appendChild(input);
''')
except Exception as e:
print(f"Iteration {i}: Exception occurred: {e}")
driver.quit()
What’s happening?
This script tries to repeatedly add and remove a password field, simulating the conditions under which Chrome’s Password manager might get confused and access freed memory.
What Could an Attacker Actually Do?
A real-world attack would look a lot more complex, but the goal is simple: after breaking into the renderer, trigger the use-after-free so the attacker controlled memory layout. With careful heap spraying (filling freed memory with specific data), an attacker might:
- Leak memory contents, exposing passwords/credentials.
How was it Fixed?
Google fixed this bug in Chrome 111..5563.110 by adjusting the password manager’s memory handling, ensuring that objects aren’t accessed after being freed. The fix is internal and not public, but usually involves techniques like:
Update Chrome!
If you’re running anything older than 111..5563.110, you’re at risk. Go to "Help" > "About Google Chrome" to check for updates.
Many browser bugs are chained together in attacks.
3. Disable password saving in your browser if you have high security requirements (use a dedicated password manager).
Conclusion
CVE-2023-1528 serves as a reminder that even mature, widely used software like Google Chrome can have critical security flaws lurking in complex features like password management. Thanks to Google’s security rewards program, these bugs are often found by responsible researchers before they can be abused—this time, by Yulei Zhang (@yueliuzhang), who was credited for the discovery.
But as long as browsers have to juggle security with convenience, and handle all sorts of unpredictable web content, new bugs will keep cropping up. The best defense, as always, is to keep your browser up-to-date—and watch for the next big CVE.
Further Reading
- Understanding Use-After-Free Vulnerabilities
- Google Chrome Security
- CVE-2023-1528 on NVD
Stay safe, and always keep your browser healthy and patched!
Timeline
Published on: 03/21/2023 21:15:00 UTC
Last modified on: 04/15/2023 04:16:00 UTC