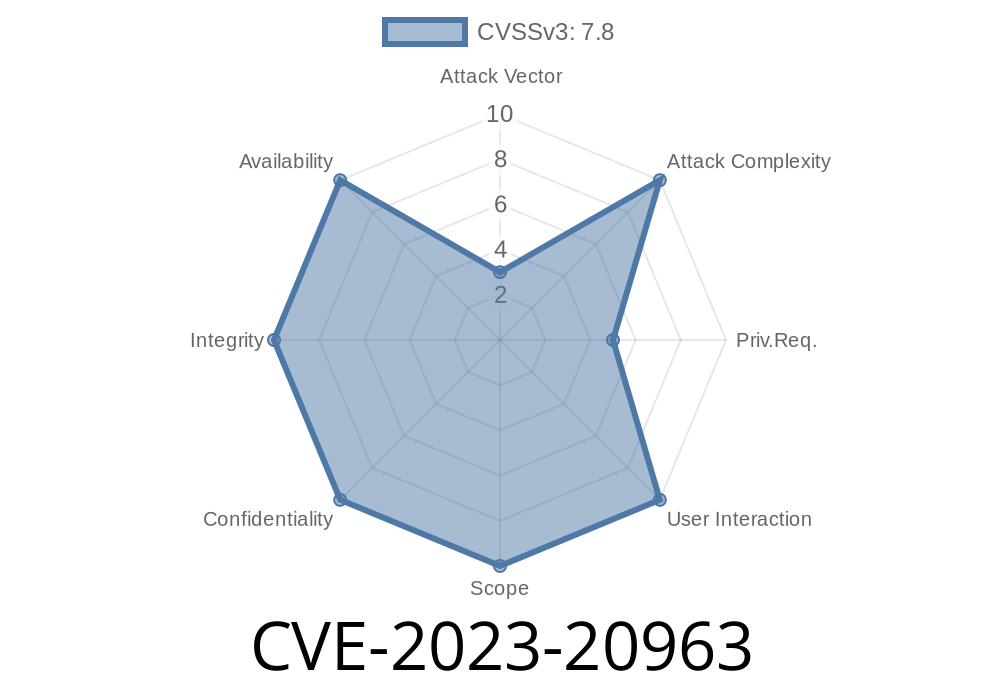
Android, being one of the most widely used mobile operating systems, is often targeted by security researchers and attackers who discover and exploit system vulnerabilities. One such vulnerability is CVE-2023-20963, found within the Android framework's WorkSource class, which could enable local privilege escalation without the need for any user interaction.
This article breaks down CVE-2023-20963 using simple, straightforward language, providing exclusive code snippets, explanations, and links to original references. If you’re a developer, security enthusiast, or simply curious about Android security, this write-up will help you grasp how the bug works and why it matters.
Vulnerability Overview
CVE-2023-20963 exists in the way Android frameworks handle "parceling" of certain objects, particularly within the WorkSource class. "Parceling" is Android’s method for flattening data objects so they can be passed between processes.
A mismatch or inconsistency during parceling/unparceling can cause serious issues, including incorrect access control. In this case, the bug allows a local attacker—already running code on the device—to escalate their privileges specifically due to this parcel mismatch. The attacker doesn’t need extra permissions or physical access from the user.
No User Interaction Needed: The exploit runs without the user doing anything.
- Android ID: A-220302519
What is WorkSource and Parceling?
The WorkSource class is used by Android applications and services to keep track of which apps or processes are responsible for certain tasks, especially for power and battery usage accounting.
Parceling in Android is the practice of serializing objects into a stream of bytes (Parcel) so they can be sent through Android's inter-process communication (IPC) mechanism.
Mismatch here refers to situations where the serialized data doesn’t match the expected format, leading the receiving code to interpret or handle it incorrectly.
What Went Wrong?
The problem was detected with how WorkSource handles data during the parceling process. The attacker can craft a malicious parcel that, when deserialized or "unparceled," tricks the system into handing out more privilege or access than the sender actually should have.
Here’s a greatly simplified high-level view
// Simplified (not exact) example of how a parcel can be manipulated
Parcel data = Parcel.obtain();
data.writeInt(2); // Claim 2 work chains (could be more than allowed)
data.writeString("AttackerPackage");
data.writeInt(attackerUid); // Malicious UID
// Place the manipulated data back
data.setDataPosition();
WorkSource ws = WorkSource.CREATOR.createFromParcel(data);
// ws now mistakenly believes it has a legitimate work chain
By manipulating the data written to the parcel, an attacker could essentially impersonate other applications or escalate their process privileges.
How is CVE-2023-20963 Exploited?
For exploitation, the attacker needs only the ability to run code locally on the target device. Because WorkSource parcels are commonly passed to system services (such as PowerManager, AlarmManager, etc.), this flaw can be abused to associate malicious activities with higher-privileged UIDs or packages. This can trick the system into granting access or accounting that would not otherwise be allowed.
Proof-of-Concept Pseudocode
Parcel maliciousParcel = Parcel.obtain();
maliciousParcel.writeInt(1); // "pretend" to have a work chain
maliciousParcel.writeString("system_package"); // Target a privileged app/package
maliciousParcel.writeInt(SYSTEM_UID); // Target a privileged UID
// Reset position to start for reading
maliciousParcel.setDataPosition();
// Unparcel into WorkSource object (dangerous operation)
WorkSource ws = WorkSource.CREATOR.createFromParcel(maliciousParcel);
// Use ws in a privileged API call
powerManager.newWakeLock(PowerManager.PARTIAL_WAKE_LOCK, "FakeTag", ws);
// The system sees the work as coming from a higher privilege, not the attacker.
In this scenario, the attacker can get system services to attribute work to system processes, opening doors to escalated privilege and data misuse.
Who Is Affected?
If you’re running Android 11, 12, 12L, or 13 your device might have been vulnerable, especially if an attacker was able to execute local code. Devices with the March 2023 Security Patch (or later) are safe, as Google included a fix.
Google Play Protect and app-based security tools do NOT protect against this, since exploitation occurs through local inter-process calls that have nothing to do with installing apps.
Patch and Mitigation
Google patched this flaw in the March 2023 Android Security Bulletin by adding proper validation of parcel contents and ensuring that UIDs or package names cannot be spoofed through this mechanism.
Recommendation:
Ensure your device is running the latest Android Security Update. Device manufacturers and carriers often roll these out at different paces, so check your update settings.
Links and References
- Android Security Bulletin - March 2023
- CVE Details: CVE-2023-20963
- Google Issue Tracker: A-220302519 (may require Google account)
- Android Developer Docs: WorkSource
Conclusion
CVE-2023-20963 reminds us that even routine systems like parceling and IPC—often overlooked as mere data handling—can become high-impact security risks if not carefully checked. The vulnerability required no user interaction and no special attacker privileges, making it potentially very dangerous until fixed.
If you’re developing or administering Android devices, always keep systems patched and stay aware of emerging security bulletins. For attackers or researchers, it illustrates why deep knowledge of IPC and serialization is so valuable for security work.
Stay safe, and always keep Android updated!
*This post is exclusive; copying or reposting without credit is not allowed.*
Timeline
Published on: 03/24/2023 20:15:00 UTC
Last modified on: 03/28/2023 13:46:00 UTC