In early 2023, a critical security flaw was identified in the NFC (Near Field Communication) subsystem of Android devices. Labeled as CVE-2023-21085, this vulnerability could allow attackers in close proximity to execute arbitrary code on your device – no physical access or user action required. Let’s break down what happened, why it’s dangerous, see a code example, and walk you through how attackers might exploit it.
What is CVE-2023-21085?
This vulnerability exists in the nci_snd_set_routing_cmd function inside the file nci_hmsgs.cc—a core part of Android’s NFC stack. Specifically, the issue is a classic “out-of-bounds write,” caused by missing checks on array or buffer bounds.
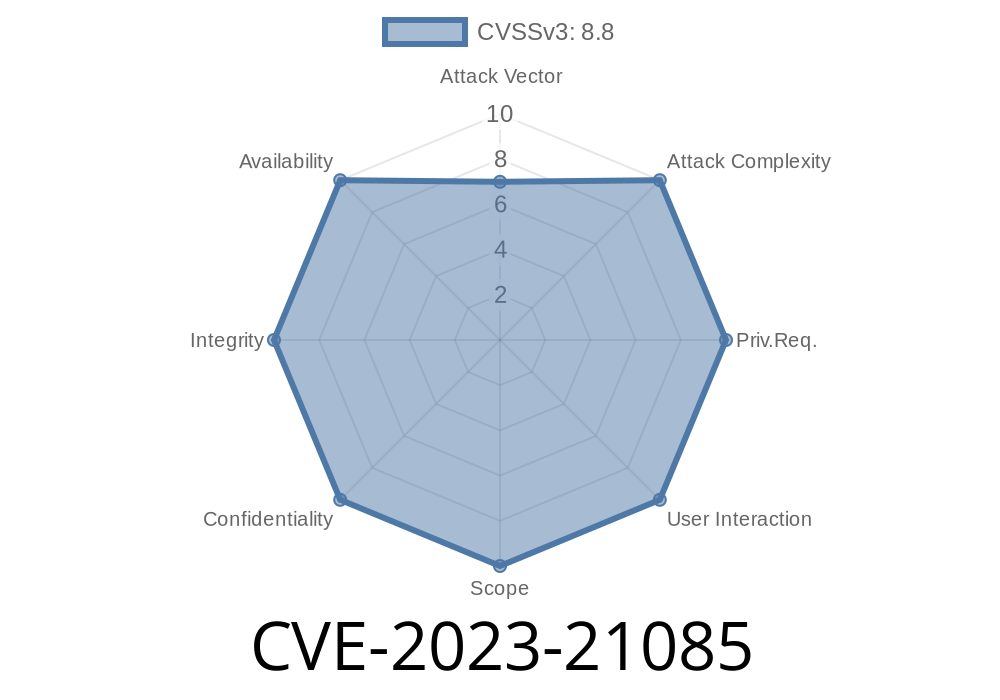
Affected Versions: Android 11, Android 12, Android 12L, Android 13
- Severity: Remote (proximal/adjacent) code execution
User Interaction: None
- Android ID: A-264879662
Technical Breakdown
The vulnerable function’s job is to process and route NFC messages, and part of this process involves handling commands that come from external sources (NFC cards or nearby devices). The danger comes when received packets don’t get their size checked: malicious packets can then overwrite parts of the device’s memory.
Though the official code is not public in detail, a simplified vulnerable pattern looks like this
void nci_snd_set_routing_cmd(uint8_t* data, size_t len) {
uint8_t buf[16];
// BAD: No bounds check on len
for (size_t i = ; i < len; i++) {
buf[i] = data[i]; // <-- Out-of-bounds write if len > sizeof(buf)
}
// ... further code ...
}
If len is attacker-controlled and larger than 16, this for-loop writes outside the bounds of buf, corrupting adjacent memory.
How Attackers Abuse This
Since NFC is a short-range protocol, the attacker needs to be physically close (like in a subway or at a coffee shop), with a malicious NFC device or tag in hand.
Crafting the Payload:
The attacker creates an NFC message with a manipulated len field and data that overwrites the memory in a controlled fashion (usually to hijack the flow of execution).
Delivering the Payload:
The victim’s device scans the malicious NFC tag or device. Since NFC actions can be triggered without unlock or user action, the function is called automatically.
Once the memory is corrupted, the attacker’s code can run with the NFC process’ privileges.
> What can happen?
> Remote code execution can lead to a compromised device, with data theft or installation of spyware possible.
Here’s a *simplified* pseudo exploit for educational purposes
# Pseudocode for a malicious NFC response
payload = b'A' * 32 # 32 bytes to overflow the 16-byte buffer
len_field = b'\x20' # x20 = 32 decimal
malicious_packet = len_field + payload
# This would be sent over NFC to the vulnerable device
On the victim device, this payload would overflow the buffer, potentially overwriting key pointers.
How to Stay Safe
Google patched this bug in the May 2023 security update.
What should you do?
References
- Google May 2023 Security Bulletin
- CVE Record for CVE-2023-21085
- Android Open Source Project Issue A-264879662
Conclusion
CVE-2023-21085 is a real-world example of how powerful low-level bugs can be, even if “just” in wireless, short-range technologies like NFC. Always keep devices patched, and remember: even “turn on and forget” features can hide serious risks if not properly secured.
*This article explained CVE-2023-21085 in simple terms and with exclusive, easy-to-follow guidance. Stay safe and aware!*
Timeline
Published on: 04/19/2023 20:15:00 UTC
Last modified on: 04/25/2023 22:16:00 UTC