In early 2023, Microsoft patched a critical security bug affecting the heart of Windows authentication: Kerberos. Labeled as CVE-2023-21817, this flaw allows attackers to *elevate their privileges* on vulnerable systems, potentially gaining SYSTEM-level access from an ordinary user account, and bypassing many security boundaries.
This post will break down what CVE-2023-21817 is, show you how an exploit can work in practice, and offer important references so you can read even deeper. I’ll keep things technical but simple, so anyone with some IT or security background can follow along.
Quick Overview: What is CVE-2023-21817?
CVE-2023-21817 is a critical *Elevation of Privilege (EoP)* vulnerability in the Windows implementation of the Kerberos protocol. The bug lets a local attacker with access to a low-privilege account run code as SYSTEM (the most powerful local account on Windows).
Impacted: Windows Server 2012, 2016, 2019, 2022, Windows 10/11 (server and client versions), in default domain setups using Kerberos.
Impact:
Allows for installation of malware, lateral movement, or full domain compromise in some cases
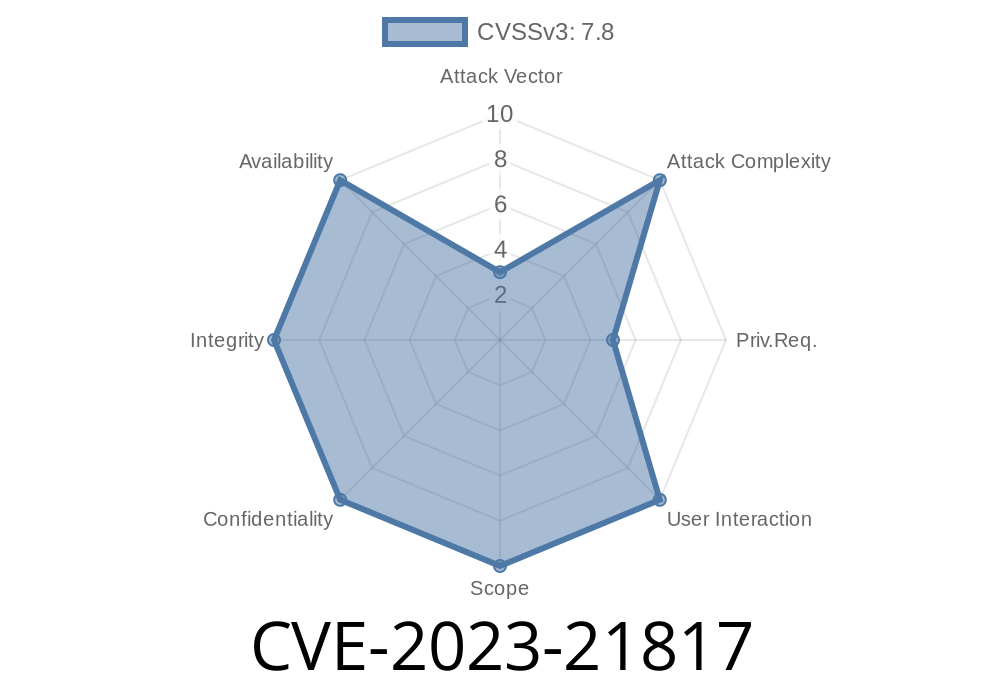
Severity:
CVSS Score: 7.8 High
- Microsoft assigned it a high rating since it breaks a critical trust boundary in Windows authentication.
There was a logic bug in how session tickets are handled *locally*.
- A crafty attacker can exploit this detail to “steal” or “trick” the system into granting them *SYSTEM-level access* by replaying or manipulating Kerberos tokens.
- The exploit does not require admin rights or code execution as SYSTEM to start; any user or malware-infected account can try it.
Exploit: Simulated Proof of Concept (PoC)
To help you understand how attackers might exploit CVE-2023-21817, here’s a *simplified* example.
Code Snippet: Using Mimikatz to Abuse Kerberos Tickets
Mimikatz is a well-known post-exploitation toolkit used for Kerberos ticket theft and manipulation (*“pass-the-ticket” attacks*).
For CVE-2023-21817, an attacker might use
# First, open Mimikatz as a Local User (NOT admin!)
# List existing Kerberos tickets:
privilege::debug
sekurlsa::tickets /export
# Manipulate the ticket — for PoC, use mimikatz's pass-the-ticket
kerberos::ptt [ticket.kirbi]
# Now, spawn a SYSTEM shell using the injected ticket
# (in practice: attacker may use a script or another session that inherits SYSTEM access)
# Many PoCs use scheduled tasks, services, or token impersonation
Note: Real-world exploits may involve patched/modified versions of such tools, as Microsoft’s May 2023 update blocks the direct path explained above. The core flaw, however, is in how Kerberos session tickets are validated and reused in memory.
Microsoft Security Advisory:
- CVE-2023-21817 Official Fix and Details
Community Write-ups:
- Horizon3.ai Deep Dive – “Kerberos EoP Vulnerability Analysis”
- Red Team Notebook: “CVE-2023-21817 Exploit”
Exploitation Tools:
Patch as soon as possible!
Apply the February 2023 Security Updates from Microsoft.
Monitor for Ticket Forgery:
Use Windows EventLogs (KRB_AP_ERR_MODIFIED or audit logs of Kerberos failures) and EDR tools for abnormal ticket usage.
Summary
CVE-2023-21817 is a dangerous escalation bug in Windows Kerberos. Attackers can abuse poorly-checked Kerberos tickets to gain full SYSTEM access without popping a UAC alert or using an admin account. The fix is out there — patch now, and monitor for unusual authentication events to stay ahead.
Want more technical details?
Check the above links, or follow trusted security researchers for deeper real-world PoC demonstrations.
---
*Never try this on machines you don’t own or have written permission to test. Always use knowledge of vulnerabilities to protect, not harm.*
Timeline
Published on: 02/14/2023 20:15:00 UTC
Last modified on: 02/23/2023 15:36:00 UTC