In April 2023, Oracle disclosed a serious vulnerability in its Database Recovery Manager (RMAN) component, tracked as CVE-2023-21918. This flaw affects the widely-used Oracle Database Server versions 19c and 21c. Despite requiring high-privileged access (SYSDBA) over the network, the vulnerability is easily exploitable and can lead to a complete denial of service (DoS) of the database environment.
This article gives you an exclusive, hands-on look at CVE-2023-21918, including technical details, exploitation, mitigations, and direct links to Oracle’s advisory.
Attack Prerequisites: Attacker needs SYSDBA privileges and network (Oracle Net) access
- Exploit Impact: Unauthorized ability to hang or repeatedly crash RMAN, leading to DoS for the database and possibly for other Oracle components using RMAN
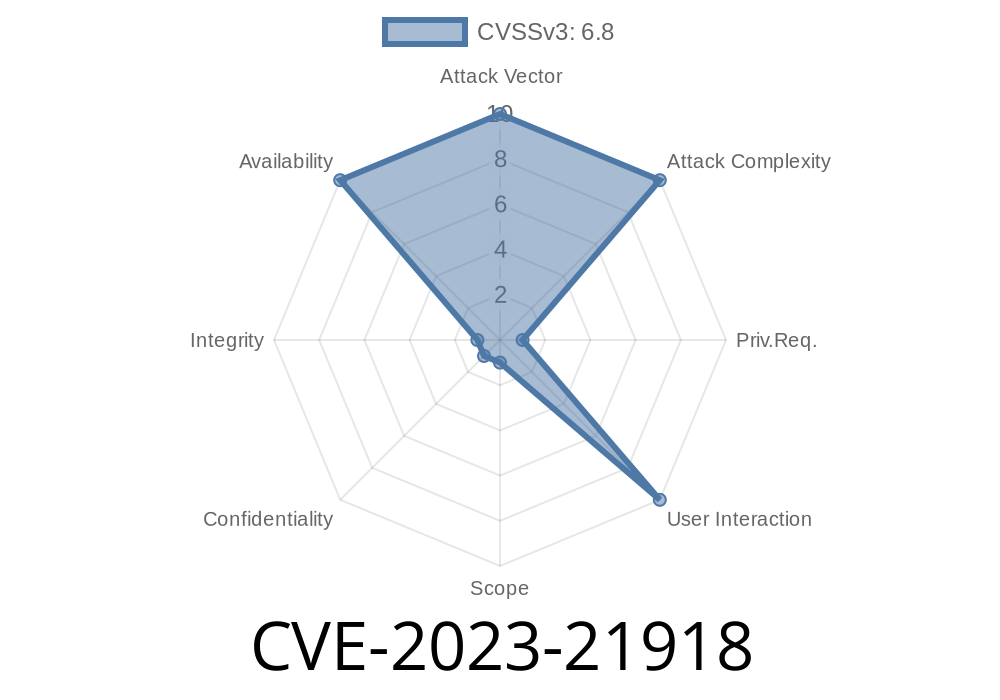
Severity: CVSS 6.8 (High Availability Impact)
- Scope Change: Vulnerability can impact more than just RMAN (could affect other components depending on RMAN)
Vulnerability Description
The flaw allows a legit, high-privileged user (with SYSDBA) to send specific, crafted requests over the network that cause the Recovery Manager (RMAN) process to either hang indefinitely or crash completely. Because RMAN is an essential part of database operations (for backup, restore, etc.), this essentially brings critical database operations to a halt, causing a repeatable denial of service (DoS).
Scope: Changed (could impact related products)
- Confidentiality/Integrity: None
Availability: High (complete DoS)
Full vector:
CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:C/C:N/I:N/A:H
How Can It Be Exploited?
A malicious actor with SYSDBA privileges and remote access can run specially crafted RMAN commands or malformed input that abuses the flaw. The specific bug involves how RMAN parses and processes certain backup or restore commands—if those are malformed in a certain way, RMAN crashes or hangs.
Runs a crafted backup or restore command (e.g., RMAN script).
3. RMAN process hangs or crashes — all database backups/recovers halt, possible wider impact if managed via Enterprise Manager/etc.
Example Snippet (PoC-like Outline)
*Note: For responsible disclosure and legal reasons, this is a theoretical demonstration and not a real exploit.*
Suppose SYSDBA connects via RMAN
# log in as high-privileged user
rman target sys/password@host:1521/ORCL
# send crafted backup command to trigger the bug
RMAN> BACKUP DATABASE FORMAT '<malformed_format>';
Replace <malformed_format> with a string that abuses the parsing vulnerability. This could lead to immediate crash or hang of the RMAN process, especially if it triggers the exact code path affected by CVE-2023-21918.
Oracle Security Advisory:
Oracle Critical Patch Update Advisory - April 2023
CVE entry: CVE-2023-21918
CVSS Details:
Impact & Risk
- Denial of Service: Backup and recovery operations fail, possibly halting business-critical tasks.
- Wider Oracle Ecosystem: Because of scope changes, products depending on RMAN (like Oracle Enterprise Manager) can also be disabled.
- Privileges Required: While attacker needs SYSDBA, this role is common in large organizations or insider threat scenarios.
Patch Immediately:
Apply the latest Oracle patches listed in the April 2023 CPU advisory. This fully closes the vulnerability.
Conclusion
CVE-2023-21918 is a powerful example of how even high-privileged, internal-facing components like RMAN can pose serious DoS risk to a whole database ecosystem. While requiring SYSDBA permissions does limit initial exploitability, the ease of attack and high impact on database availability—plus the risk of insiders or compromised accounts—makes patching non-negotiable.
Patch now, review permissions, and keep your Oracle installation secure.
Further reading
- Oracle CPU April 2023
- Oracle RMAN Documentation
- National Vulnerability Database - CVE-2023-21918
Timeline
Published on: 04/18/2023 20:15:00 UTC
Last modified on: 04/18/2023 20:37:00 UTC