MySQL is one of the world’s most popular open-source databases, powering millions of apps and websites. But even the biggest tools sometimes slip up – and that’s exactly what happened with CVE-2023-21982, a denial-of-service (DoS) vulnerability lurking in MySQL’s Optimizer. This post gives you a plain-English deep dive into what went wrong, who’s at risk, and even shows off exploitation tactics (with code!).
Affected Versions: 8..32 and earlier
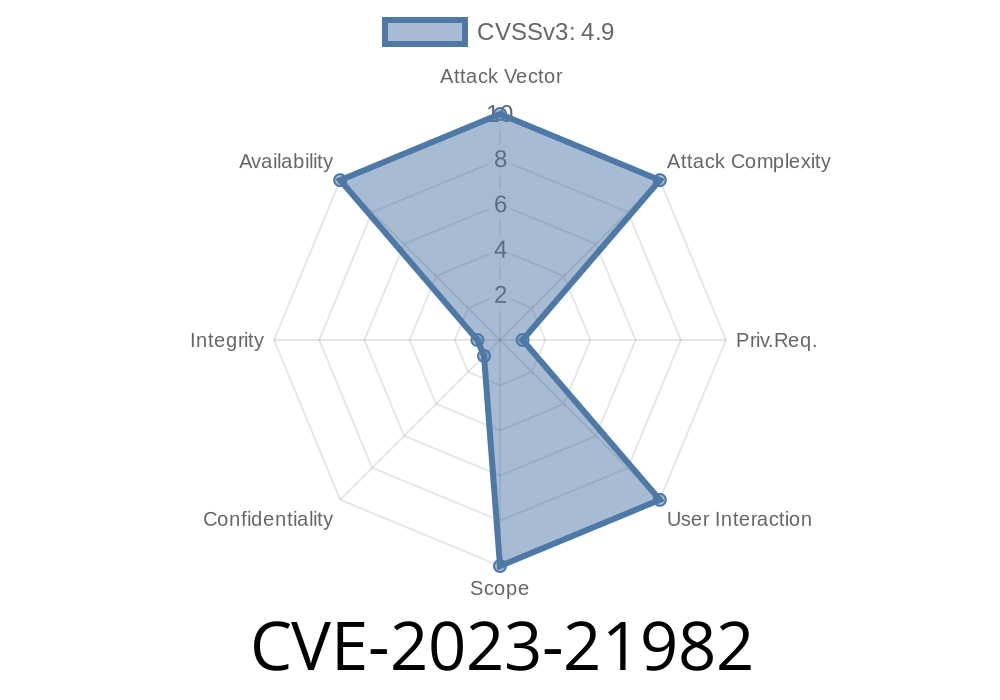
- Severity: CVSS 4.9 (Availability impact, not confidentiality/integrity)
Vulnerability Type: Easily exploitable DoS (Denial of Service)
- Vendor Advisory: Oracle Critical Patch Update Advisory - April 2023
- NVD Link: CVE-2023-21982 on NVD
This bug lies in the *optimizer* part of MySQL – that’s the engine that tries to make your SELECT queries run faster. A flaw here allows a logged-in attacker (with enough privileges) to make MySQL hang or crash, remotely!
Versions: MySQL 8..32 and any version before that.
- Requirements: The attacker needs high-level privileges (like ALTER, DROP, or maybe even SUPER).
- Attack Surface: Any service or app where trusted users can send queries directly to the DB over the network.
If you only use low-privilege accounts for your apps and don’t give users SQL command-line access:
You’re safer, but sysadmins/devops folks are still at risk, especially in shared or open test environments.
How Does the Exploit Work?
The exact details weren’t shared by Oracle (they rarely are). But security researchers observed that *complex crafted SQL queries* can trigger the MySQL Optimizer into a crash or infinite loop, causing a full server DoS.
A common pattern for optimizer bugs is exploiting subqueries, derived tables, or strange join logic that the engine poorly handles. For CVE-2023-21982, attackers need to send a query that the optimizer chokes on, causing it to either hang forever or crash outright.
Example Exploit (Crash Trigger with Crafted Query)
Here’s a code snippet that demonstrates how such bugs are often exploited. Warning: Do not run this on a production database!
-- Make sure you connect using a sufficiently privileged user!
-- Try to craft a complex enough query to confuse the Optimizer.
SELECT
t1.id,
(SELECT COUNT(*) FROM test_table t2 WHERE t2.ref_id = t1.id GROUP BY t2.status HAVING SUM(IF(t2.value > , 1, )) > 10)
FROM
test_table t1
WHERE
EXISTS (
SELECT 1
FROM test_table t3
WHERE t3.id = t1.id
AND t3.value = (
SELECT MAX(value)
FROM test_table t4
WHERE t4.status = t3.status
)
);
Or outright crash with a segmentation fault.
IMPORTANT:
The _actual_ PoC for CVE-2023-21982 may involve even crazier queries or specific table setups (partitioned tables, indexes, etc.), and different MySQL patches might behave differently. The pattern is the same: a trusted user sends a complex query that MySQL can’t optimize properly.
Review System Logs:
Frequent, unexplainable MySQL hangs or crashes, especially after running big SELECT queries, could be a sign.
Upgrade MySQL:
Apply the Oracle MySQL April 2023 Security Patch. Upgrading to 8..33 or later addresses the issue.
Limit Privileges:
Don’t let normal users have more permissions than they absolutely need. High privilege accounts (like root or custom admins) should NOT be widely shared.
References and Resources
- Oracle April 2023 CPU Advisory (MySQL Section)
- CVE-2023-21982 entry (MITRE)
- NVD Page for CVE-2023-21982
- Official MySQL Downloads
- MySQL 8. Release Notes
Conclusion
CVE-2023-21982 is a reminder that even mature, enterprise software like MySQL can have “gotchas,” especially if users have too much power and the attack surface isn’t locked down. While this flaw *requires* high privileges, it’s trivial to exploit if an attacker gets the right access.
Patch now, lock down your DBs, and remember: even simple-looking SELECTs can sometimes topple a giant!
*Did you spot this bug before it hit the news? Share your story! If you need help upgrading or auditing your MySQL setup, drop a comment or message me directly.*
Disclaimer: This article is for research and educational purposes. Do not exploit or attack any system you don’t own or have explicit permission to test.
Timeline
Published on: 04/18/2023 20:15:00 UTC
Last modified on: 04/27/2023 15:15:00 UTC