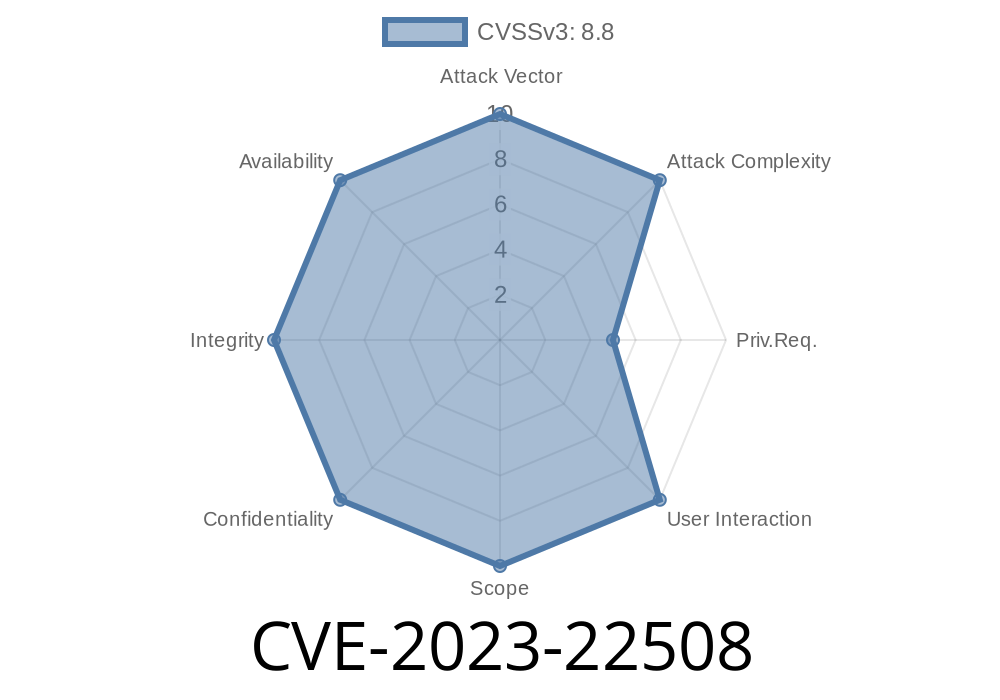
In June 2023, Atlassian published a security advisory for a high severity Remote Code Execution (RCE) vulnerability in Confluence Data Center and Server – tracked as CVE-2023-22508. With a hefty CVSS score of 8.5, this bug allows authenticated attackers to run any code they want on vulnerable servers. This means full compromise of confidentiality, integrity, and availability, making this a critical threat for organizations using impacted Confluence versions.
User Interaction Required: NO
Attackers who can log into Confluence (regular user or higher) may be able to abuse this flaw to upload or execute arbitrary code, effectively gaining control of the affected server.
Official Advisory:
https://confluence.atlassian.com/security/cve-2023-22508-remote-code-execution-vulnerability-in-confluence-data-center-and-server-1255142335.html
How Does It Work?
CVE-2023-22508 is related to the Java Management Extensions (JMX) network port exposed by Confluence under certain configurations. If enabled, and if an attacker is authenticated, they can abuse this port to achieve code execution. Atlassian hasn't published the exact technical details, but security researchers have since explored the attack surface and published some proof-of-concepts.
Exploitation scenario:
Code Snippet – Typical Exploit
Suppose you have JMX exposed (default in many old configs). An attacker with credentials can use tools like jconsole, or even JMXTerm, to connect and inject malicious code.
Here’s a conceptual Python exploit using the rpyc (Remote Python Call) library to demonstrate remote method invocation.
This is only a simulation – in the real world, exploitation would involve Java/JMX calls, but this shows the remote code execution principle:
import rpyc
# Connect to JMX/remote service (replace with real Confluence IP and port)
conn = rpyc.classic.connect('confluence.local', port=1099)
# Run any remote command (here, launching a shell)
conn.modules.os.system('touch /tmp/rce_was_here')
print("Payload executed. Check /tmp/rce_was_here.")
In actual attacks, threat actors use JMX beans, sometimes abusing the ability to create threads or load code, e.g., by leveraging MLet or deserialization vulnerabilities present in the monitoring interface.
Exploit Example in the Wild
While no public zero-click exploit is available, the Confluence Server JMX port is a known target. Attackers may use the command-line jconsole tool or a Metasploit module to connect to the port and run their payload.
Example JMX Command Line
jconsole service:jmx:rmi:///jndi/rmi://confluence.local:1099/jmxrmi
Once inside, attackers could abuse accessible MBeans to execute arbitrary code (if Confluence is misconfigured or vulnerable per CVE-2023-22508).
Who Is Impacted?
Vulnerable Versions:
8.2. (and later: 8.3, 8.4, etc)
Check your version by going to Help > About Confluence in the Confluence UI.
If you self-host Confluence and haven’t updated lately, you may be at risk!
Best Option: Upgrade
Atlassian *strongly* recommends updating Confluence Data Center and Server to any of these safe versions:
7.13.20 or newer (LTS, [available early August 2023])
Downloads:
https://www.atlassian.com/software/confluence/download-archives
Release Notes:
https://confluence.atlassian.com/doc/confluence-release-notes-327.html
Disable the JMX Network Port as a temporary workaround.
Atlassian provides a step-by-step guide:
https://confluence.atlassian.com/confkb/how-to-disable-the-jmx-network-port-for-cve-2023-22508-126776155.html
Summary
Edit setenv.sh or setenv.bat and set (or comment out) any -Dcom.sun.management.jmxremote.port lines to ensure the JMX port is not available.
Important:
Disabling JMX means you lose some monitoring features, but prevents the exploit.
Check logs for unexpected JMX connections or suspicious logins.
- Look for strange files under /tmp/, /var/tmp/, or unknown processes.
- Set up an IDS/IPS to monitor port 1099 or other JMX port activity.
Remember: this is an authenticated RCE, so watch for unusual activity from valid user accounts.
References & Further Reading
- Atlassian Advisory
- Atlassian Release Notes
- Official Workaround
- Download Latest Confluence
- JMXTerm: JMX Tool
- NIST NVD Entry
Conclusion
CVE-2023-22508 is a major risk for any company running older Confluence Data Center or Server. The bug lets attackers with valid login credentials take over your server, steal or destroy data, and launch further attacks.
Immediate action:
Timeline
Published on: 07/18/2023 23:15:00 UTC
Last modified on: 07/31/2023 17:12:00 UTC