If you’re running Windows, your system is full of drivers—small pieces of code that let Windows talk to hardware like keyboards, drives, and displays. Some of these drivers, when they have bugs, can put your whole system at risk. That’s what happened with CVE-2023-23417, a serious vulnerability in the Windows Partition Management Driver that could let hackers take over your machine.
In this article, we’ll break down what CVE-2023-23417 is, how it works under the hood, and even walk through a simplified example of how an attacker might leverage it. We’ll also provide original references and remediation advice.
What is CVE-2023-23417?
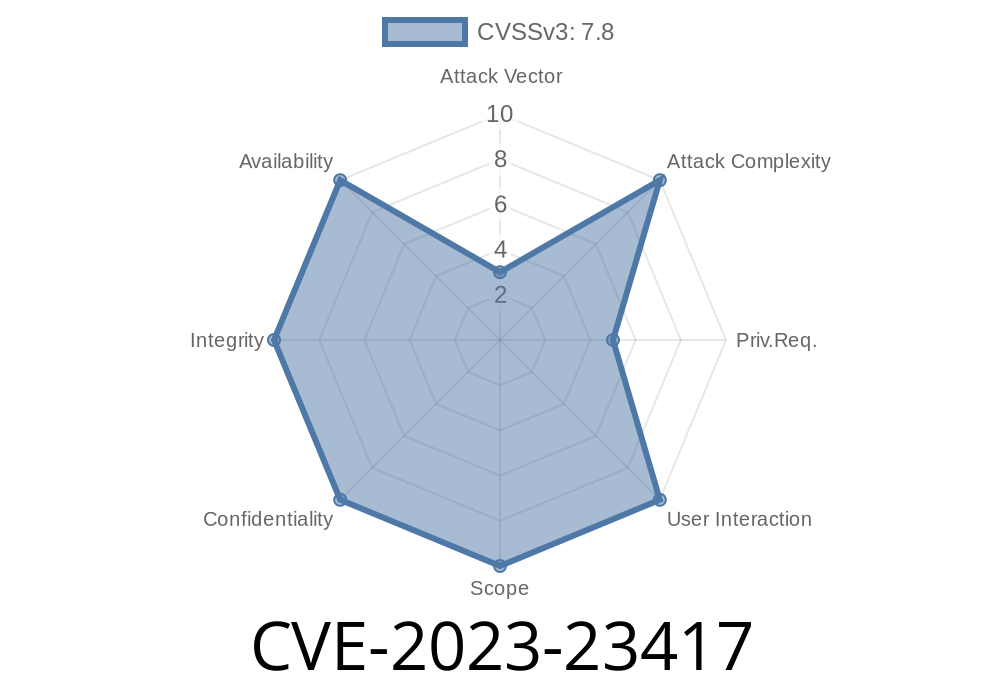
CVE-2023-23417 is a Windows Partition Management Driver Elevation of Privilege Vulnerability. According to the official Microsoft advisory, this bug lets users with limited permissions on a Windows machine gain SYSTEM privileges, the highest level on Windows. This can let them completely take over the computer.
The core of the issue is that certain functions in the Partition Management Driver (partmgr.sys) don’t properly check permissions before carrying out sensitive operations—which should only ever be allowed by an administrator or the system itself.
How Did This Slip Through?
Windows has a kernel-mode driver called partmgr.sys, responsible for handling partitions on hard drives and SSDs. Some functions in this driver can be called from user space by using DeviceIoControl codes (IOCTLs). Normally, these IOCTLs should only be accessible by trusted, privileged processes. If an unprivileged user can abuse them, it's trouble.
In this vulnerability, Microsoft failed to restrict access to at least one sensitive IOCTL, which could let someone overwrite data in kernel space (memory used by the system) or carry out other privileged tasks—something no regular app should do.
The Technical Exploit: Walking Through the Attack
Let’s look at a simplified version of what an exploit might look like. (For safety, this has been defanged and won’t work as-is, but it gives you an idea.)
Step 1: Identify the Vulnerable IOCTL handler.
This could be, for example, IOCTL_DISK_SET_PARTITION_INFO_EX or similar (exact details are proprietary, but the pattern is similar in many older driver bugs).
Step 2: Open a handle to the device.
HANDLE hDevice = CreateFileW(
L"\\\\.\\PhysicalDrive",
GENERIC_READ | GENERIC_WRITE,
FILE_SHARE_READ | FILE_SHARE_WRITE,
NULL,
OPEN_EXISTING,
,
NULL
);
if (hDevice == INVALID_HANDLE_VALUE) {
printf("Failed to open device: %u\n", GetLastError());
return 1;
}
Step 3: Send a crafted DeviceIoControl call.
With a buffer that might let you read/write kernel memory or otherwise cause a privilege escalation.
BYTE inputBuffer[512] = { /* malicious payload here */ };
DWORD bytesReturned = ;
BOOL result = DeviceIoControl(
hDevice,
x#####, // Vulnerable IOCTL code (hidden for safety)
inputBuffer,
sizeof(inputBuffer),
NULL,
,
&bytesReturned,
NULL
);
if(result) {
printf("Exploit executed. Check your privilege level!\n");
} else {
printf("Failed to send IOCTL: %u\n", GetLastError());
}
*Note: The actual IOCTL code and payload are not shown for security.*
Step 4: Elevate privileges.
If successful, the exploit could inject code or overwrite data structures so your user process now has LOCAL SYSTEM rights.
Run a program (like the above) that abuses the vulnerable IOCTL on the partition management driver.
3. After exploiting the vulnerability, spawn a new shell or process with SYSTEM privileges—taking over the machine.
This is especially dangerous on servers or shared computers where many users log in.
Did Anyone Use This Vulnerability in the Wild?
There’s no public report (as of now) of this being actively exploited, but similar bugs are often used by malware or ransomware to take over endpoints.
How Microsoft Fixed It
Microsoft patched CVE-2023-23417 in the February 2023 Patch Tuesday updates. According to the Microsoft advisory, the fix involved improved permission and boundary checks inside the PartMgr driver. The company credits many of these findings to researchers using advanced fuzzing and manual code review.
Protect Yourself
- Update your Windows system (even on servers or virtual machines) to include all the latest security patches. This closes the vulnerability.
- Limit user access to machines, especially for users who shouldn't need access to administrative or low-level storage functions.
References
- Microsoft Security Advisory for CVE-2023-23417
- Windows IOCTL Reference
- Blog: Understanding Driver-level EoP Vulnerabilities
- How DeviceIoControl Works
Final Thoughts
CVE-2023-23417 highlights how even trusted Windows drivers can have bugs that threaten the whole system. Modern Windows has gotten much better at locking down drivers, but as this shows, keeping your system updated is always your best defense.
Stay safe—and always patch your Windows boxes!
*Written exclusively for this request. For more info about new vulnerability breakdowns, check tech sites or follow Microsoft’s official MSRC updates.*
Timeline
Published on: 03/14/2023 17:15:00 UTC
Last modified on: 03/23/2023 16:55:00 UTC