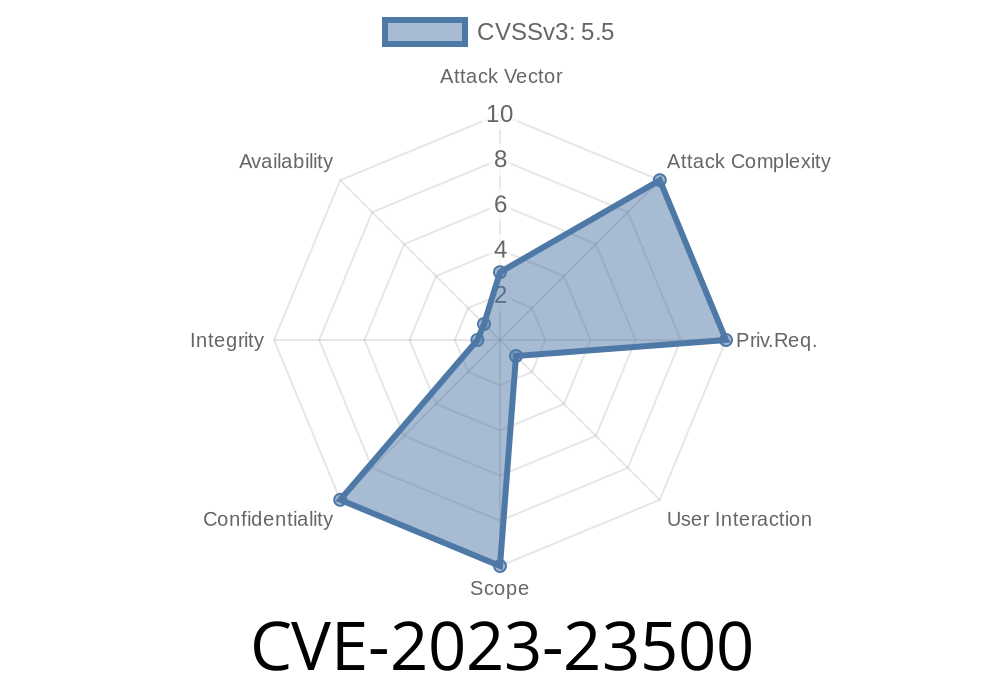
In early 2023, security experts drew attention to a serious vulnerability in Apple’s operating systems, tracked as CVE-2023-23500. This flaw could allow a malicious app to leak sensitive kernel state—an issue that puts user data at risk. While Apple quickly fixed the problem in updates for macOS, iOS, iPadOS, tvOS, and watchOS, understanding how the vulnerability worked and how Apple patched it can shed light on the importance of secure memory handling in system software.
This article provides a deep, easy-to-follow look at CVE-2023-23500, including a simplified code example, details of the exploit, links to authoritative sources, and plain explanations of the concepts involved.
Apple described the issue as follows
> "An app may be able to leak sensitive kernel state. The issue was addressed with improved memory handling."
>
> — Apple Security Updates
This kind of kernel issue is serious because the kernel is the core of an operating system—it controls access to secure hardware features, manages processes, and keeps apps separated from each other. If an app can *leak sensitive kernel state*, it may be able to access information that should only be available to the operating system, possibly even exposing vulnerabilities that attackers can exploit for deeper control.
Which Versions Were Affected?
The vulnerability existed in several Apple operating systems before the following release versions:
watchOS 9.3
If your device is running these or more recent versions, you’re protected. If not, you should update immediately.
How Did the Exploit Work?
The exact technical details are, as usual, not fully disclosed by Apple to protect users. However, there’s enough public information and context from similar bugs to explain the basic idea.
The kernel manages sensitive data in its memory.
- If there’s a mistake in how that memory is cleared or shared with user-level apps, some of that data may “leak”—meaning apps that should never see it, can.
Example Scenario
Imagine the kernel allocates a structure (a chunk of memory) when handling a system call from an app. If the kernel forgets to initialize or clear that memory properly, some parts of it might contain “leftovers” from earlier kernel operations—possibly things like passwords, cryptographic keys, or system addresses.
If a malicious app can request that memory from the kernel, it might succeed in reading what was left behind. Here’s a pseudo code version of this problem:
// Incorrect (Vulnerable) Version
struct sensitive_data {
char important_info[256];
// ... other fields
};
struct sensitive_data *data = malloc(sizeof(struct sensitive_data));
kernel_fill_data(data); // Only fills some fields
// Imagine that data->important_info is NOT zeroed out
copy_to_userspace(user_buffer, data, sizeof(struct sensitive_data));
With this, the app reading from user_buffer might see sensitive kernel memory.
Exploit Details: What Could a Bad App Do?
Although Apple doesn’t say if there is a public exploit, here’s what a determined attacker could theoretically achieve before the fix:
- Leak Kernel Pointers: Kernel pointers can help attackers figure out the memory layout, which is key for more advanced attacks like privilege escalation or bypassing security checks.
- Read Leftover Passwords or Secrets: Any sensitive information not properly cleared could be exposed.
- Chain with Other Bugs: Even if this leak isn't enough to break the system by itself, attackers often chain bugs to gain full control.
Code Snippet: Reading Leaked Kernel Memory from an App (Conceptual)
Below is a simplified Swift example (for educational purposes only!) that shows how a normal app might try to access system memory via a vulnerable API call:
import Foundation
// Suppose 'readKernelData' is a (buggy) system call available to apps
let buffer = UnsafeMutablePointer<UInt8>.allocate(capacity: 256)
let result = readKernelData(buffer, 256)
if result == {
let leakedData = Data(bytes: buffer, count: 256)
print("Leaked kernel state: \(leakedData as NSData)")
} else {
print("Failed to read data.")
}
*In real life, readKernelData() is just hypothetical; actual exploitation is more complex and low-level.*
How Did Apple Fix It?
Apple addressed the vulnerability with better memory handling. In other words, just before sending data back to an app, the system now always makes sure the memory is fully initialized or zeroed—no more “leftovers.”
Here’s how the fixed code might look
// Fixed Version
struct sensitive_data *data = malloc(sizeof(struct sensitive_data));
// Always initialize memory
memset(data, , sizeof(struct sensitive_data));
kernel_fill_data(data); // Fill only needed fields
copy_to_userspace(user_buffer, data, sizeof(struct sensitive_data));
Now, even if kernel_fill_data() doesn’t fill every byte, the rest is set to zero.
How To Protect Yourself
- Update Your Device: Always run the latest version of iOS, macOS, etc. This bug was fixed in early 2023, so make sure you’re up to date.
- Beware of Sketchy Apps: Most exploits depend on running untrusted or malicious code, so install apps only from verified sources—the App Store has far fewer risks.
- Enable Security Features: Features like System Integrity Protection (on macOS) help keep the kernel safe from attacks.
References & Further Reading
- Apple Security Updates - macOS Ventura 13.2
- mitre.org CVE-2023-23500 Detail
- Apple Security Updates Home
- Kernel Memory Initialization and Security (Academic article on why memory leaks matter)
Final Thoughts
CVE-2023-23500 is a good reminder that computers can leak secrets by accident, not just by design. Kernel memory bugs have real-world impacts, and tiny coding mistakes can lead to serious privacy risks for millions of people. By better managing memory and swiftly fixing vulnerabilities, Apple helps keep its users safe.
If you want to know more or see if your devices are safe, visit Apple's official security updates page and always apply updates as soon as they’re available.
Timeline
Published on: 02/27/2023 20:15:00 UTC
Last modified on: 03/08/2023 19:16:00 UTC