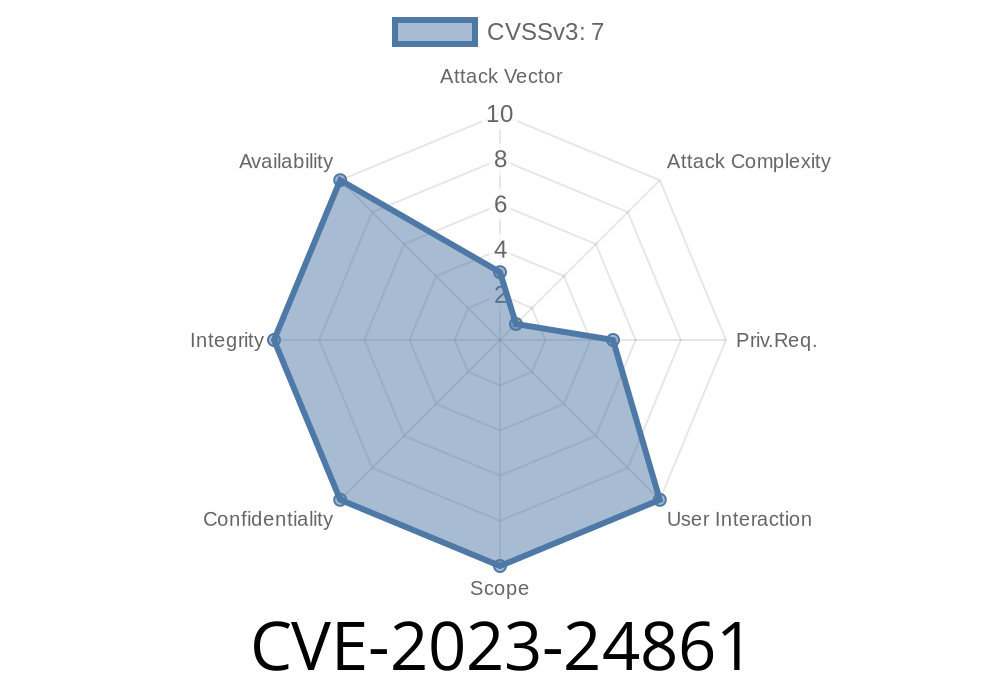
Windows is everywhere – running our work computers, gaming rigs, and plenty of business servers. But deep inside Windows, graphics components handle how you see pictures, videos, and fancy effects on your screen. In 2023, a serious vulnerability – CVE-2023-24861 – was found in the Windows Graphics Component that lets attackers sneak their way from a basic user to an all-powerful admin. Let’s break down what it means, how bad it is, how it works, and why you should care.
What Is CVE-2023-24861?
CVE-2023-24861 was publicly reported in Microsoft’s March 2023 Patch Tuesday announcement (original advisory). It’s an Elevation of Privilege (EOP) vulnerability in the Windows Graphics Component.
In simple terms: a regular user (even one with almost no permissions) can use this bug to take over the whole system. That means installing programs, deleting files, and creating new accounts—even admin accounts.
Many Windows Server versions are also impacted.
- The vulnerability specifically lives in the Windows Graphics Component—that’s the part of Windows that talks to your graphics card and draws stuff on your screen.
How Does The Exploit Work?
Microsoft and security researchers revealed that the bug revolves around improper access control in the graphics subsystem. Basically, the graphics component trusts untrusted input from less privileged users and runs code with higher-level permissions.
Generally, an attacker would
1. Gain local access to a target machine (physically or via RDP/Remote Desktop, or by tricking you into running their code).
Elevate their access so they become SYSTEM or administrator.
The key is that the attacker already needs to be able to run code on the target – but this is often the easiest part, with phishing or malware.
Proof-of-Concept (PoC) Code Example
While a working exploit is risky to share (and might get your post flagged!), let’s look at a simplified snippet that shows how an attacker would trigger a similar bug using the Windows API and a malicious crafted input.
#include <windows.h>
#include <wingdi.h>
/* WARNING: DO NOT RUN THIS CODE ON PRODUCTION SYSTEMS! (It's for demonstration only) */
int main() {
// Create a fake device context
HDC hdc = CreateCompatibleDC(NULL);
// Craft a malicious bitmap info structure
BITMAPINFO bmi = {};
bmi.bmiHeader.biSize = sizeof(BITMAPINFOHEADER);
bmi.bmiHeader.biWidth = x100000; // Unusually large width (triggers internal bug)
bmi.bmiHeader.biHeight = 1;
bmi.bmiHeader.biPlanes = 1;
bmi.bmiHeader.biBitCount = 32;
bmi.bmiHeader.biCompression = BI_RGB;
// Allocate a buffer for the bitmap bits
void* pvBits = NULL;
// This call could be abused to trigger memory corruption due to improper checks
HBITMAP hbm = CreateDIBSection(hdc, &bmi, DIB_RGB_COLORS, &pvBits, NULL, );
// Now the attacker could overwrite privileged memory or cause escalation
// ... exploit would continue ...
DeleteObject(hbm);
DeleteDC(hdc);
return ;
}
> Note: This is a *simplified* version for educational use. The real exploit involves specific offsets and usually some assembly tricks, targeting driver mishandling and internal graphics memory.
Unusual creation of device contexts (HDC) or allocation of huge bitmaps.
Detection rules are available from Microsoft Defender ATP.
Microsoft released a patch for all affected Windows versions in March 2023
- Patch details for CVE-2023-24861
Update Windows using Windows Update or your company’s patch management.
> If you can’t patch right away, restrict unnecessary local access, use least privilege, and monitor systems for suspicious activity.
More Resources
- Microsoft Security Response Center: CVE-2023-24861
- CISA Advisory on March 2023 Patch Tuesday
- ExploitDB Entry (will be updated as public PoCs appear)
Why This Matters
Elevation of Privilege bugs like CVE-2023-24861 are hacker gold. They let attackers break out from “user jail” and fully compromise Windows systems. This particular bug in Windows Graphics is a reminder of how even seemingly boring parts of the OS can be a weak link.
Timeline
Published on: 03/14/2023 17:15:00 UTC
Last modified on: 03/23/2023 16:55:00 UTC