Microsoft’s printer drivers have long helped millions of Windows users get print jobs done. But sometimes, what seems like just another routine system component can open up a big security risk. That’s exactly the case with CVE-2023-24884—a Remote Code Execution (RCE) vulnerability in Microsoft’s PostScript and PCL6 Class Printer Drivers.
In this post, we’ll break down what CVE-2023-24884 is, how it works, and what proof-of-concept (PoC) code might look like. References to Microsoft’s advisories and other sources are included, and the language is kept simple and straightforward for security enthusiasts and sysadmins alike.
What is CVE-2023-24884?
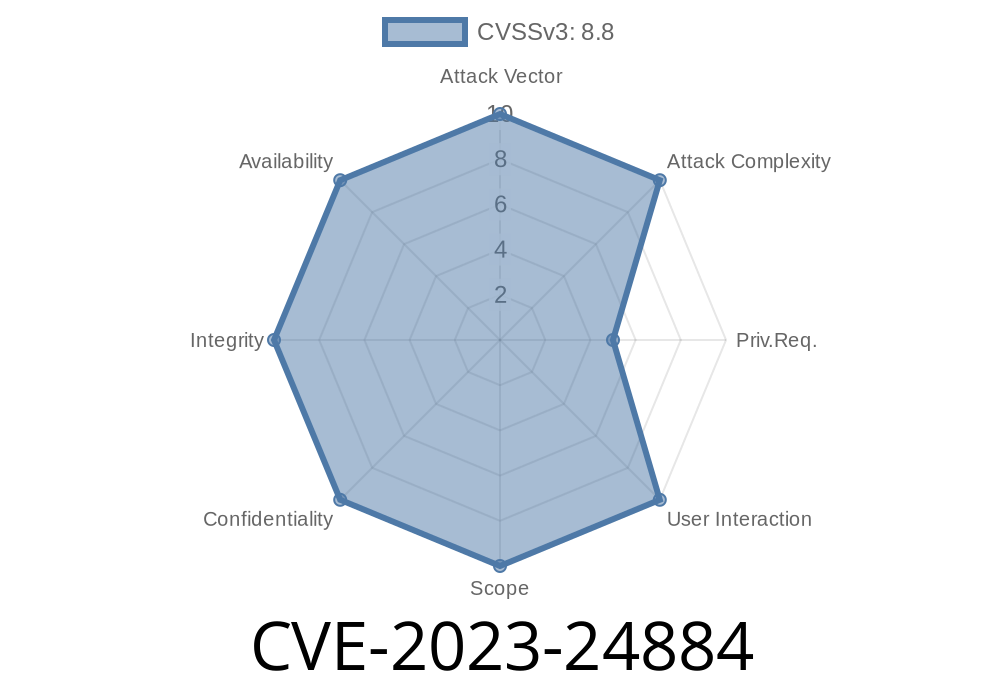
CVE-2023-24884 is a remote code execution vulnerability in the “Microsoft PostScript and PCL6 Class Printer Driver.” Disclosed and patched as part of Microsoft's March 2023 Patch Tuesday, this vulnerability could allow an attacker to run code as the SYSTEM account—one of the most powerful accounts on a Windows machine—by exploiting how Windows processes specially crafted printer jobs.
Official Description
> *A remote code execution vulnerability exists when the Windows Print Spooler service improperly performs privileged file operations. To exploit this vulnerability, an attacker would need to have the ability to submit a crafted print job to a vulnerable system. For more information, see Microsoft's advisory.*
Who is Vulnerable?
The vulnerable components are built into many modern Windows versions, including Windows 10 and 11. If you have *“Microsoft PostScript Class Driver”* or *“Microsoft PCL6 Class Driver”* installed, your system could be at risk. These drivers are default choices for network printers using Microsoft’s universal class driver.
Here’s the exploitation flow, explained simply
1. Attacker gains access—either by being on the same network or by tricking a victim into installing a malicious printer.
2. Crafted print job—the attacker sends a specially designed print job to the Windows Print Spooler service using the vulnerable driver.
3. Trigger the Vulnerability—the driver processes the print job insecurely, allowing code to execute with SYSTEM privileges.
The key is that crafted PostScript or PCL data can cause the printer driver to mishandle files, open handles, or even drop payloads to disk—sometimes in C:\Windows\System32, where only SYSTEM can write.
Microsoft's official write-up:
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-24884
Proof-of-Concept Snippet
A full, functional exploit is not public (and for good reason). But here’s a conceptual breakdown of what an exploit might look like in PowerShell, using the Windows printer APIs:
# PowerShell PoC snippet for crafting a print job
$printerName = "Microsoft PCL6 Class Driver"
$data = [System.Text.Encoding]::ASCII.GetBytes("%!PS\nsystem('calc.exe')\n") # Malicious PostScript-like payload
$hPrinter = Add-PrinterPort -Name $printerName
Start-Process -FilePath "cmd.exe" -ArgumentList "/c echo $data > \\localhost\$printerName"
# This is just a high-level example - real PoCs use raw APIs and may not look like this!
The real world exploit requires in-depth knowledge of the Print Spooler service and raw print job formatting. The key takeaway is that by sending carefully crafted PostScript or PCL commands, an attacker may get the driver to execute code as SYSTEM.
Microsoft Security Advisory:
CVE-2023-24884 - Microsoft Update Guide
Mitre Database Entry:
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-24884
Windows Print Spooler Vulnerabilities Blog:
https://blog.fox-it.com/2021/06/30/printer-nightmare-and-the-windows-print-spooler/ *(for related context)*
Limit Print Spooler Exposure
If you don’t need the Print Spooler service, consider disabling it or limiting its exposure to untrusted users or networks.
Final Thoughts
CVE-2023-24884 is a great reminder that even “basic” Windows features like printer drivers can become serious attack vectors. If you manage Windows environments, update your systems ASAP and monitor print-related activity for unusual patterns.
Timeline
Published on: 04/11/2023 21:15:00 UTC
Last modified on: 04/14/2023 14:26:00 UTC