---
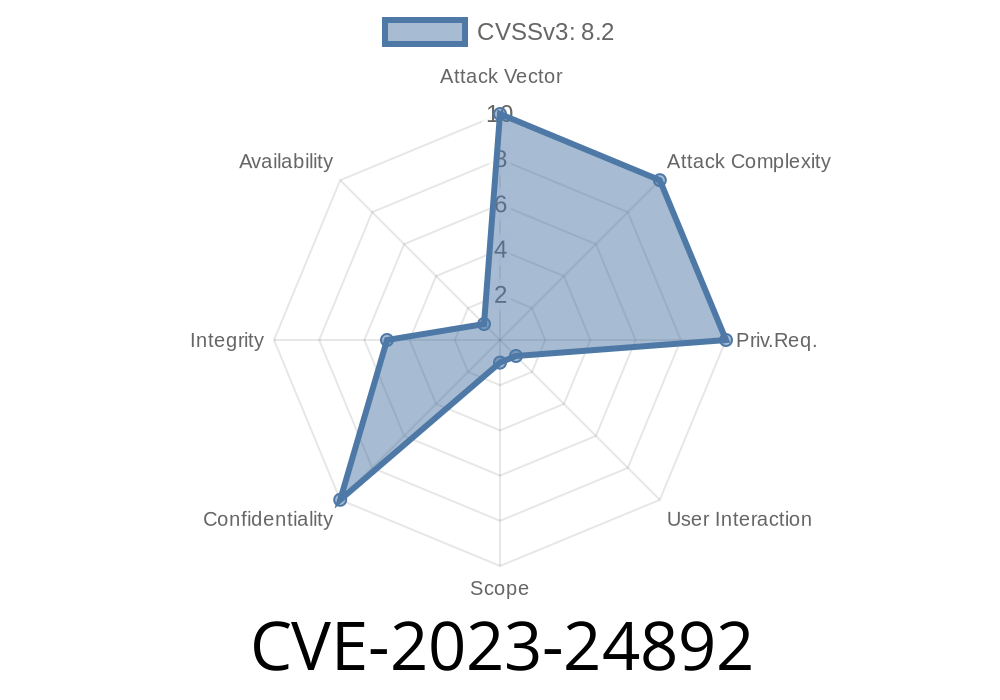
In early 2023, Microsoft patched an important security issue in their Edge WebView2 technology. Known as CVE-2023-24892, this vulnerability lets an attacker spoof web content inside desktop apps that use the Edge Chromium-based WebView2 browser control. That means you could see “fake” websites inside Windows apps—even if you think you're safely inside a trusted app.
In this post, I’ll break down what CVE-2023-24892 means in easy terms, show how the vulnerability works, present code to understand the exploit, and give you direct links to patches and references.
What is Microsoft Edge WebView2?
WebView2 is a framework that lets Windows developers embed a Chromium-based web browser inside their apps. Imagine a banking app with a built-in browser. WebView2 is how that browser exists in your app.
Developers use it because it's modern, powerful, and kept updated with Microsoft's Edge browser codebase.
What is CVE-2023-24892 All About?
The vulnerability allows attackers to spoof content in WebView2. That means with some trickery, an attacker can make your app display a website (like a login form) that looks genuine but is, in fact, malicious. If a user believes they're safe (since they're inside a trusted app), they're more likely to give away sensitive info.
Severity: Moderate
CVE page: CVE-2023-24892
Microsoft advisory: ADV230002
How Does the Spoofing Work?
At the heart of CVE-2023-24892 is a flaw in how WebView2 reports the actual address (URL) shown in the browser control.
Imagine a malicious app or a compromised WebView2 app that runs the following logic
- It tells WebView2 to load a trusted website (like https://accounts.microsoft.com).
- But, using certain navigation and event tricks, it changes the displayed content to a malicious site (like http://evil.example.com/fake-login).
- The URL bar (if you even have one) will still say https://accounts.microsoft.com, but the user is seeing content from http://evil.example.com.
If the app displays the reported URL *somewhere* (like a title bar or an info box), it can be tricked into saying the site is safe, even while delivering nasty payloads.
Example Exploit (PoC): Basic Demonstration
Let’s see how this could happen in code. Below is a simplified C# WinForms WebView2 app with a vulnerability.
Note: This proof-of-concept is for learning only. Don't use it for evil!
using Microsoft.Web.WebView2.WinForms;
using Microsoft.Web.WebView2.Core;
using System.Windows.Forms;
public class VulnerableForm : Form
{
public WebView2 webView;
public Label urlLabel;
public VulnerableForm()
{
webView = new WebView2 { Dock = DockStyle.Fill };
urlLabel = new Label { Dock = DockStyle.Top, Height = 30 };
webView.CoreWebView2InitializationCompleted += (s, e) =>
{
// Update label when navigation occurs
webView.CoreWebView2.NavigationCompleted += (sender, args) =>
{
urlLabel.Text = "You are at: " + webView.Source;
};
webView.CoreWebView2.Navigate("https://accounts.microsoft.com");
};
this.Controls.Add(webView);
this.Controls.Add(urlLabel);
webView.CreateControl();
}
}
// Malicious scenario:
// The attacker injects code or opens a pop-up which, via JavaScript and window manipulation, loads their own content into the main view,
// but the Source property (reported in the URL label) doesn't update correctly, continuing to show Microsoft.com!
Why Is This Bad?
- If the label (or address bar) displays webView.Source, but the real content comes from somewhere else, a user could be tricked into thinking they're safe.
Microsoft Security Response Center:
WebView2 Release Notes:
NIST National Vulnerability Database (NVD):
GitHub discussion about the issue:
Update: Always use the latest WebView2 runtime and SDK in your applications.
- Verify content: Don’t trust the reported Source blindly; leverage HTTPS and *only* allow navigation to whitelisted URLs.
- Double-check navigation events: Use events like CoreWebView2.NavigationStarting and CoreWebView2.SourceChanged to tightly control what is displayed versus what is reported.
Example: Strict Navigation Handling
webView.CoreWebView2.NavigationStarting += (s, e) =>
{
Uri uri = new Uri(e.Uri);
if (uri.Host != "accounts.microsoft.com")
{
e.Cancel = true; // Block navigation to untrusted hosts.
}
};
Summary Table
| Aspect | Details |
|-----------------------|------------------------------------------------|
| CVE | CVE-2023-24892 |
| Affected Software | Chromium-based Edge WebView2 |
| Exploit | Content spoofing (fake websites in trusted app)|
| Severity | Moderate (phishing, data theft risk) |
| Patched? | Yes, update Edge and WebView2 runtime |
| Resource | Microsoft Advisory|
Conclusion
CVE-2023-24892 is a reminder: even desktop apps can have classic “browser” bugs like spoofing. If you’re a developer, update your WebView2 controls, rethink your navigation logic, and never display a URL to your users you haven’t carefully verified.
Stay updated, and keep your users safe!
*For deeper technical analysis, see the official CVE entry and the WebView2 changelog.*
Timeline
Published on: 03/14/2023 17:15:00 UTC
Last modified on: 05/09/2023 18:15:00 UTC