1. Background: What is Apache Superset?
Apache Superset is a popular open-source data visualization and data exploration platform. It’s used by data scientists and engineers to connect to data sources, visualize data, and build dashboards. It runs as a web server and supports authentication and fine-grained permissions out-of-the-box.
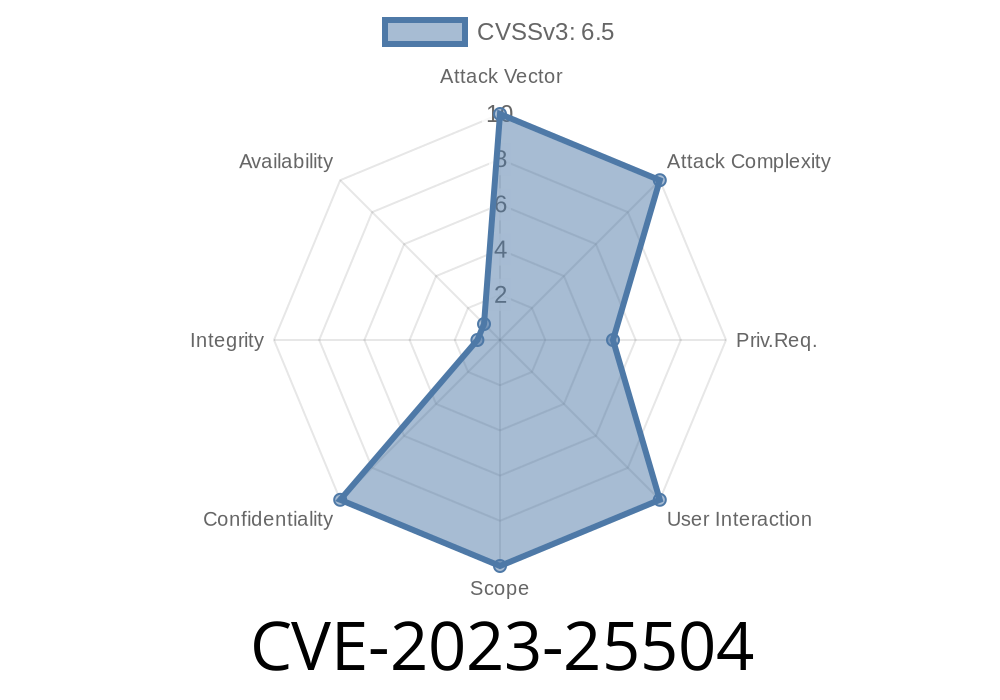
2. What is CVE-2023-25504?
CVE-2023-25504 is a security vulnerability in Apache Superset (versions up to and including 2..1). If an attacker gains valid authentication and at least *import dataset* permissions, they can leverage the *import dataset* feature to perform SSRF (Server-Side Request Forgery). This means they can trick Superset’s server into querying internal resources like internal IP addresses, metadata services, and other endpoints not meant to be exposed, all from the perspective of the server.
*This is especially dangerous if your Superset host has access to sensitive internal services.*
3. Understanding SSRF in the Context of Superset
Server Side Request Forgery (SSRF) is a type of attack where the server is manipulated into making unwanted requests to internal or external resources. In Superset, this could allow an attacker to:
Exfiltrate data from services that only the server can access
SSRF attacks often lead to more serious consequences in cloud environments.
Your Superset server can reach internal network resources or cloud metadata APIs
*Even non-admin authenticated users with dataset import rights could exploit this.*
Attacker prepares a malicious dataset import file that points to an internal or sensitive URL.
3. Attacker uses the "import dataset" feature to upload/import this file.
4. Superset server processes the dataset by fetching metadata (using the URL in the import), thereby making the request on behalf of the attacker.
5. Responses from internal resources—which might be inaccessible directly from the attacker—are now accessible via the Superset server.
6. Code Example: Triggering SSRF
Below is a sample (Python-based) minimal malicious dataset import file that tries to make the Superset server reach out to a sensitive internal service. In Superset, dataset imports are often delivered as JSON/YAML. Suppose you want to import a new database connection pointing to an internal-only service.
malicious_database.yaml
- database_name: "evil_db"
sqlalchemy_uri: "http://169.254.169.254/latest/meta-data/";
expose_in_sqllab: true
allow_run_async: true
sqlalchemy_uri is supposed to specify the database connection string.
- Instead, it targets the AWS EC2 metadata service, which is only reachable from within the internal network.
- When Superset processes the import, it may try to reach this URI, exposing the contents to whoever imported the resource.
Upload the above YAML file.
4. Check the server logs/response—you may see data fetched from the internal 169.254.169.254 address.
Important: Running this against production or without permission is illegal and unethical. This should only be attempted in a test environment you control.
What should you do to fix or mitigate this?
- Upgrade Superset: Upgrade to version 2.1. or later where this vulnerability has been fixed.
- Network Controls: Restrict your Superset server’s outbound network access, especially to internal services or cloud metadata endpoints.
Web Application Firewall: Use a WAF to block SSRF patterns if possible.
8. References & Further Reading
- Official CVE: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-25504
- Apache Superset Security Advisory: https://lists.apache.org/thread/6zwqxfkh11yv9jzx8dgh1stp2cmfqntw
- Superset Changelog: https://github.com/apache/superset/blob/2.1./CHANGELOG.md
- AWS EC2 Metadata: https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/instancedata-data-categories.html
- OWASP SSRF Explained: https://owasp.org/www-community/attacks/Server_Side_Request_Forgery
- Mitigating SSRF Attacks: PortSwigger SSRF prevention
Summary:
*CVE-2023-25504 is a dangerous vulnerability that allows authenticated users to leverage Apache Superset's dataset import to perform SSRF, accessing internal resources by abusing the server's network permissions. If you run or administer Superset, patch immediately and review user permissions—don’t wait for attackers to find your system!*
Timeline
Published on: 04/17/2023 17:15:00 UTC
Last modified on: 04/27/2023 14:08:00 UTC