In February 2023, security researchers discovered a significant flaw in the GNU Binutils package that can cause application crashes and enable local denial of service (DoS). The vulnerability, identified as CVE-2023-25588, is rooted in improper initialization of a specific field within the Mach-O file handler code. This post breaks down the bug, its exploitability, and helps you understand what’s going on behind the scenes—even if you aren’t a C developer.
What Is Binutils?
Binutils is a set of binary tools used to handle object files, such as linkers (ld), assemblers (as), and various utilities. These tools are critical for compiling and manipulating programs on Unix-like operating systems.
Affected Function: bfd_mach_o_get_synthetic_symtab
- Bug: The the_bfd field of the asymbol struct is left uninitialized, leading to undefined behavior. If Binutils tries to use this faulty struct, it can crash.
Technical Details
When working with object files, Binutils uses a struct called asymbol. A key member of this struct is the_bfd, a pointer to the Binary File Descriptor (BFD). Normally, this should be set to point to the correct BFD structure; if not, operations using this pointer can go seriously wrong.
Inside the source file
// Inside bfd_mach_o_get_synthetic_symtab (simplified):
asymbol *syms = bfd_malloc (...);
for (i = ; i < n; i++) {
syms[i].name = ...;
// OOPS! syms[i].the_bfd is NOT initialized!
}
The danger comes when later code assumes the_bfd is a valid pointer. Use of an uninitialized value leads to a crash, which a local attacker could trigger by feeding a specially-crafted file to binutils tools like nm, objdump, or readelf.
Proof-of-Concept Exploit
Create a malformed Mach-O binary and run a binutils tool on it. The tool will attempt to process it, hit the buggy function, and crash.
# malformed.o is a crafted Mach-O file
nm -A malformed.o
# Segmentation fault (core dumped)
For those who want to see it in C, here’s a snippet to show unsafe struct use
asymbol *sym = malloc(sizeof(asymbol));
printf("%p\n", sym->the_bfd); // UNDEFINED! May crash.
Attackers could automate the delivery of such files to crash system services relying on Binutils.
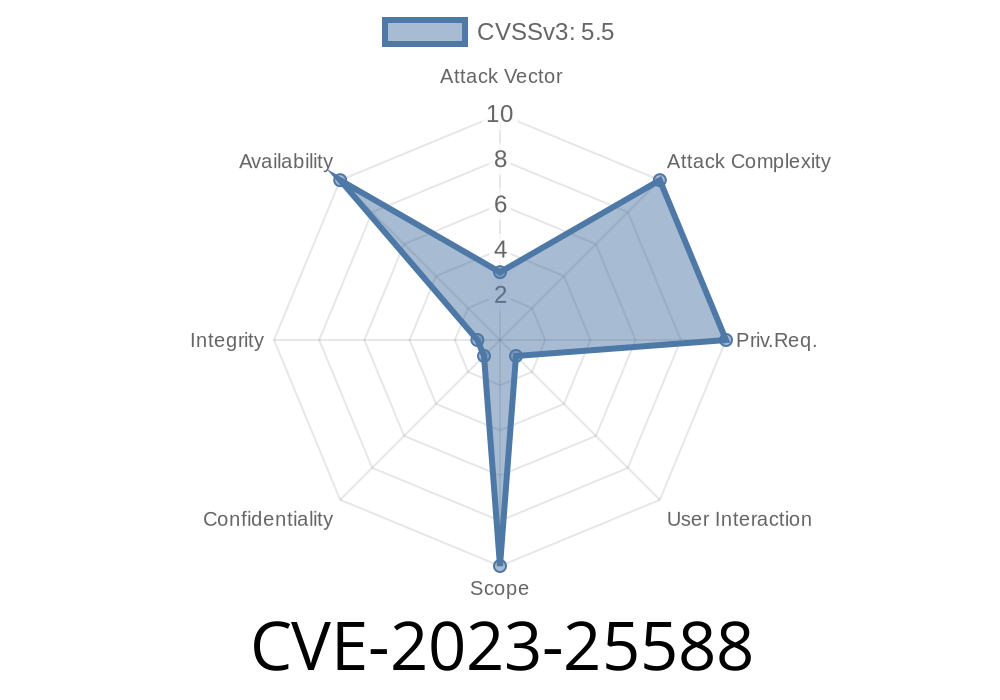
Impact
- Scope: Local, because attackers need to run code or convince you to run a tool (like nm, objdump) on their malicious file.
- Denial of Service: Crashes the tool, possibly affecting automated systems (such as continuous integration servers) that process untrusted binaries.
If you build Binutils from source, ensure you have the latest patches.
Workaround: Avoid running Binutils tools on untrusted Mach-O files.
References
- NVD: CVE-2023-25588 Details
- Binutils Bugzilla Issue
- Upstream Patch Commit
Key Takeaways
- CVE-2023-25588 is a denial-of-service flaw: a single malformed binary may crash Binutils tools.
- Impacts tools that process Mach-O files (used mainly on macOS, but code path can be built on Linux too).
- Fix is simple—initialize all struct fields—but demonstrates why handling binary formats needs care.
If you use Binutils, keep it updated!
*This post is an original simplification for educational purposes. If you handle untrusted binaries regularly, reviewing your toolchain's version and patch status is highly recommended.*
Timeline
Published on: 09/14/2023 21:15:00 UTC
Last modified on: 09/20/2023 17:10:00 UTC