If you use Firefox or Thunderbird, you’ve probably seen the fullscreen warning bar pop up when a website tries to take over your whole screen. That’s one of your browser’s ways of making sure shady sites can’t easily impersonate system dialogs or trick you. But what if a site could throw you into fullscreen mode… and never let you out?
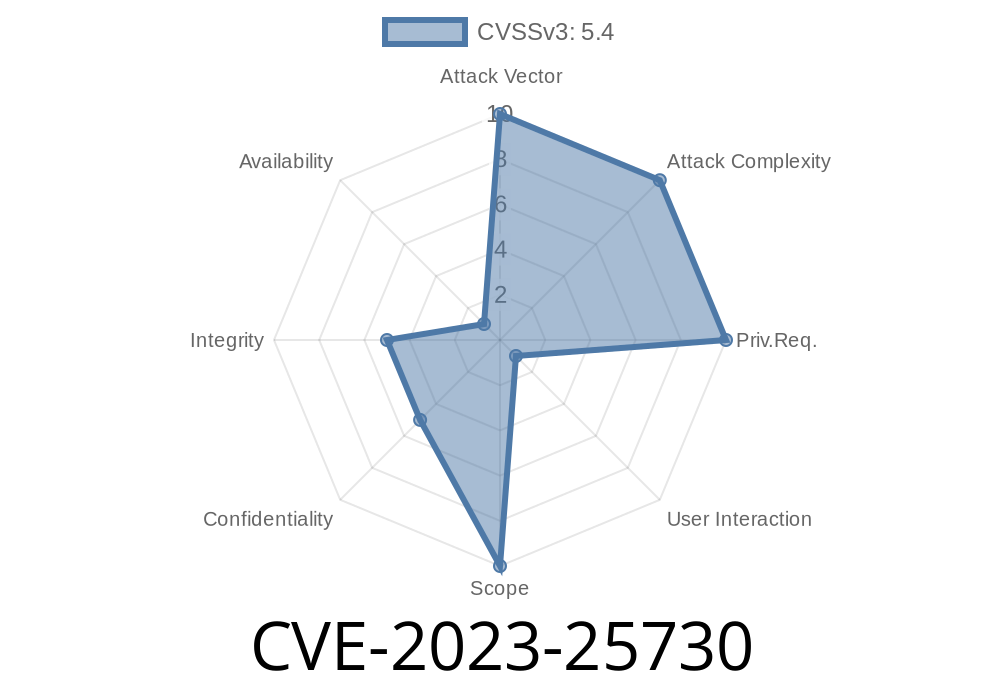
That’s exactly what CVE-2023-25730 makes possible. This vulnerability lets a website lock your browser in fullscreen, potentially leading to user confusion or even clever phishing attacks. Let’s break down how this works, see some code, and go over the risks.
What is CVE-2023-25730?
In short: this is a flaw in older versions of Firefox, Firefox ESR (Extended Support Release), and Thunderbird. A script running in the background can call requestFullscreen(), then completely block the main thread (the part of your browser running the webpage code). Because of this block, the browser cannot quit fullscreen, leaving the user stuck. This could, for example, let a phishing page cover your whole screen with a fake login window, giving the bad guys a shot at stealing your details.
Why is This a Problem?
Browsers are designed to prevent fullscreen abuse. Usually, if something goes fullscreen, a message bar appears along the top, and hitting Esc or other keys quits fullscreen. But if the main thread is completely locked, the browser might not process your requests to exit.
Fool you into entering your password!
Mozilla explains the issue in their advisory (original reference):
> "A background script invoking requestFullscreen and then blocking the main thread could force the browser into fullscreen mode indefinitely, resulting in potential user confusion or spoofing attacks."
The Vulnerable Code: How It Works
Let’s see a simplified proof-of-concept. This script launches a fullscreen request, then runs an infinite loop to block the main thread. Once you go fullscreen, there’s no intuitive way out.
<!DOCTYPE html>
<html>
<body>
<button id="go">Go Fullscreen Trap</button>
<script>
document.getElementById('go').onclick = function() {
// Request fullscreen
document.documentElement.requestFullscreen().then(() => {
// Block the main thread
while (true) { /* Infinite loop blocks forever */ }
});
}
</script>
</body>
</html>
Then, an infinite while (true) loop begins.
- This stalls the main UI. Even pressing Esc or trying to close the tab might not work, since the browser isn’t listening anymore.
> Tip: This affects only browsers mentioned above, and only before versions where the patch was released.
Confuse you enough to force a reboot or even run malware
It’s scary because victims may not realize they’re *still just in the browser*.
Limiting the opportunities for background scripts to block user interaction.
You can read the fix and advisory for technical details.
How to Stay Safe
- Update your browser: Make sure Firefox, Firefox ESR, and Thunderbird are all updated to the latest versions.
References & More Reading
- Mozilla Security Advisory: MFSA2023-05 - CVE-2023-25730
- Bugzilla report and fix discussion
Final Thoughts
This bug is a good reminder that browsers are complex and even small permission gaps can lead to big user risks. As always, keep your software up to date, and be wary of strange behavior when browsing unfamiliar sites. Stay safe!
*This post is written for educational purposes and uses public information with original code for demonstration only.*
Timeline
Published on: 06/02/2023 17:15:00 UTC
Last modified on: 06/08/2023 17:16:00 UTC