When you surf the web, you expect things to “just work”—especially when it comes to encryption, which runs under the hood. But sometimes, a small slip can crash your browser. That’s what happened with CVE-2023-25742: a bug that surfaced when Firefox and Thunderbird tried to import a certain type of public key.
In this post, we’ll break down what went wrong, how hackers could exploit it, show a simplified code example, and point you to the best references.
What is CVE-2023-25742?
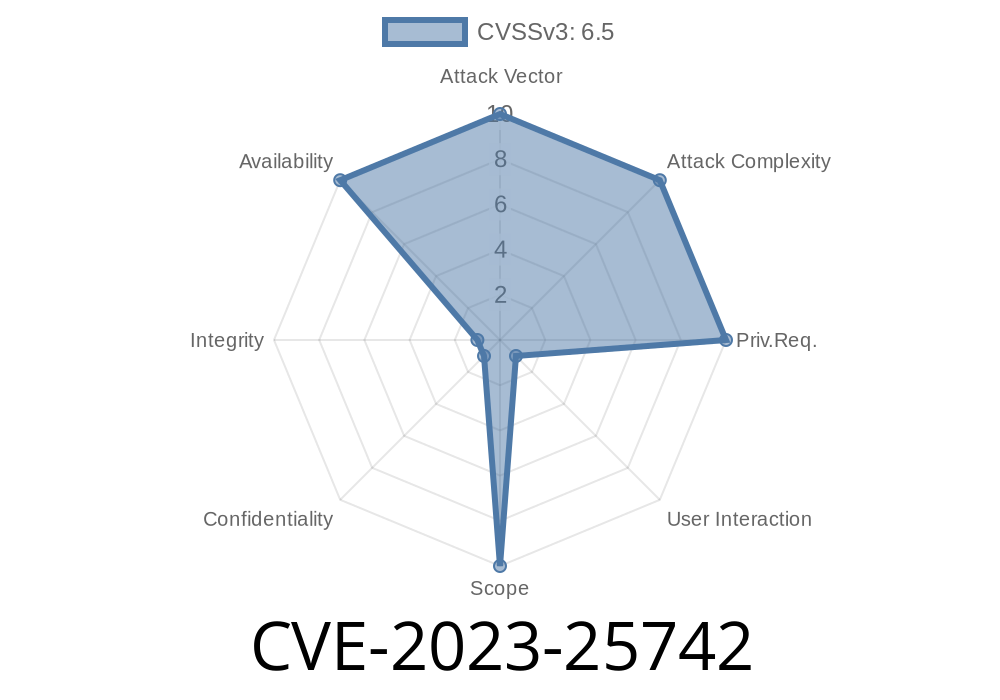
*CVE-2023-25742 is a security issue in Mozilla’s Firefox, Firefox ESR, and Thunderbird. The problem? If a website gives your browser an RSA public key but makes the browser treat it as an ECDSA P-256 key instead, Firefox doesn’t know what to do—and crashes the current tab.*
Firefox ESR before version 102.8
If you’re on these old versions, you’re at risk.
Who Discovered It?
This bug was publicly assigned CVE-2023-25742 and fixed by Mozilla, as documented in their official security advisories:
- Mozilla Foundation Security Advisory 2023-10
- Bugzilla Report
How Did This Vulnerability Work?
Here’s the core issue: when a website or script tried to import a public key using the Web Crypto API, Firefox wouldn’t check carefully whether the key being imported matched the expected algorithm.
A public key in SPKI (Subject Public Key Info) format might actually be an RSA key, but could be *misdeclared* as an ECDSA (P-256) key. The code handling the key would try to load it as ECDSA, but RSA keys are structured very differently. This confusion caused things to go haywire—and crash the tab.
What Does an Attack Look Like?
A hacker could craft a web page which uses JavaScript’s SubtleCrypto.importKey() to import an RSA public key, but tell Firefox it’s an ECDSA key. The browser wouldn’t check carefully—and crash.
Here‘s a simplified example in JavaScript
// Not a working exploit, just for learning!
async function crashFirefoxWithPublicKey() {
// This is actually an SPKI DER-encoded *RSA* public key.
const spkiRSAKey = new Uint8Array([
x30, x82, x01, x22, /* ...snip... */
]);
// Try to import it as ECDSA P-256
try {
const importedKey = await window.crypto.subtle.importKey(
"spki",
spkiRSAKey.buffer,
{
name: "ECDSA",
namedCurve: "P-256"
},
false,
["verify"]
);
// If the bug is present, the browser may crash here.
} catch (e) {
console.log("Error importing key:", e);
}
}
crashFirefoxWithPublicKey();
In a vulnerable browser, running this code would cause the tab to crash. Newer versions just throw an error and move on.
For more details, see the bug tracker entry
Key point
- The browser didn’t validate that the imported SPKI data actually matched the expected key type (RSA vs ECDSA).
Upgrade! If you’re not on the latest version of Firefox or Thunderbird, update now
- Latest Firefox Download
- Thunderbird Download
Mozilla patched the bug to reject keys that don’t match the expected algorithm.
References
- Mozilla Security Advisory 2023-10
- Bugzilla Bug 1816207
- NVD - CVE-2023-25742
Summary
*CVE-2023-25742* showed how a simple mismatch in public key handling could crash a major web browser through the Web Crypto API. While there’s no direct data theft or code execution reported, any bug that lets someone remotely crash your apps deserves attention. If you use Firefox, Thunderbird, or ESR, make sure you’ve updated past the vulnerable version.
If you want to stay safe, always keep your software fresh. For developers: be careful with cryptography APIs—never assume the data type matches what’s expected!
Timeline
Published on: 06/02/2023 17:15:00 UTC
Last modified on: 06/08/2023 16:36:00 UTC