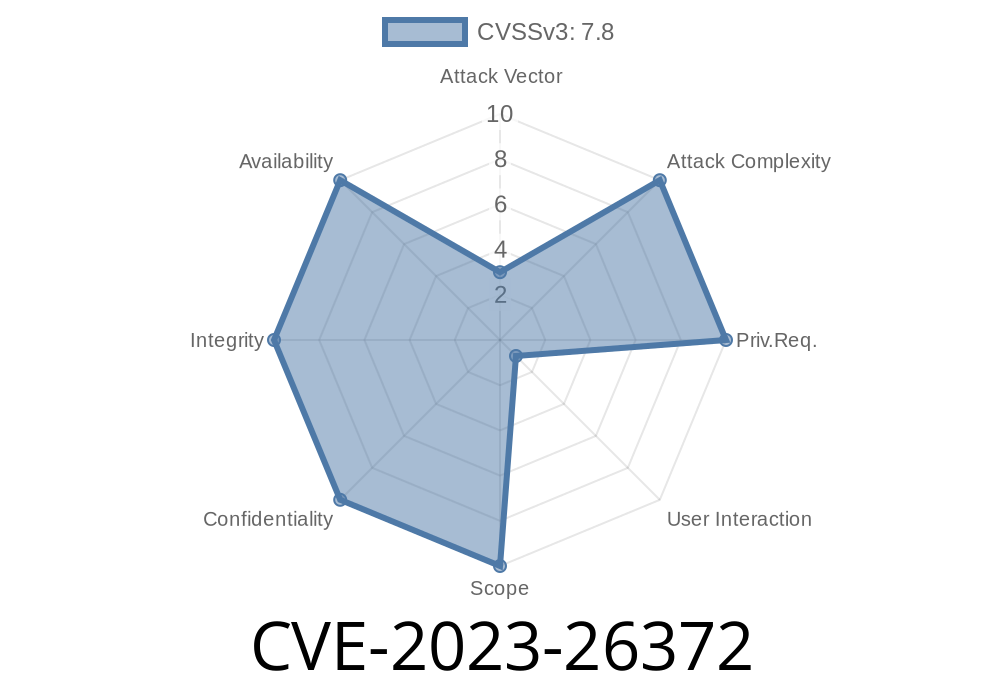
Adobe Dimension is a popular 3D design software used by creative professionals around the world. In early 2023, security researchers uncovered a significant vulnerability—CVE-2023-26372—which affects Adobe Dimension version 3.4.8 and all earlier versions. This post will break down what this vulnerability means, how it can be exploited, and what you should do to keep your system safe. We’ll provide simple code snippets to show how such an attack could be constructed, and link you to authoritative resources to dig deeper.
What is CVE-2023-26372?
CVE-2023-26372 is an out-of-bounds write vulnerability. This type of vulnerability happens when a program writes data outside the bounds of memory it should normally access. In Adobe Dimension, if an attacker crafts a specially designed file and convinces a user to open it, they can force the software to write malicious code into system memory. Ultimately, this can let the attacker execute code of their choice—meaning, they could install malware, steal data, or get control over the victim's computer.
---
Affected Software: Adobe Dimension versions 3.4.8 and earlier
- CVE: CVE-2023-26372
User Interaction: Required (victim must open a malicious file)
---
How Does the Exploit Work?
The hole lies in how Adobe Dimension processes 3D asset files (like .dn or related formats). Attackers can create a malformed file—one that looks like a normal Dimension project but actually includes data that triggers the vulnerability.
Victim opens the file in Adobe Dimension.
4. Dimension processes the file and hits the out-of-bounds write, letting the attacker’s code run on the victim’s system.
Example Exploit Code (Simplified)
Disclaimer: This is for educational purposes. Do not use it for unauthorized access or malicious purposes.
Suppose the vulnerability is in the way Adobe Dimension handles the length of a particular asset entry in the .dn file. An attacker could add extra bytes at the end, making the application overwrite memory.
Here's a highly simplified Python script that demonstrates how an attacker might manipulate a file
# cve2023-26372_exploit.py
# For education only
MALICIOUS_DATA = b'A' * 1024 + b'\x90' * 100 # NOP sled
# Insert shellcode or payload after the NOP sled
MALICIOUS_DATA += b'\xcc' * 10 # Placeholder for payload (int 3 - breakpoint)
# Simulate a malformed .dn file
with open('exploit.dn', 'wb') as f:
f.write(b'HEADER') # Standard header
f.write(b'LENGTH\x00\x00\x10\x00') # Faked length field (overflow trigger)
f.write(MALICIOUS_DATA) # Overflow payload
f.write(b'FOOTER')
When Dimension tries to read and process this file, the oversized "LENGTH" field may end up writing our payload outside the bounds of the intended buffer—which, in a real attack, could let malicious code run.
Technical Details
The vulnerability is classified as an "out-of-bounds write" (CWE-787). That means Dimension does not properly check the size of user-controlled input from the file, which leads to memory corruption.
Usually, software expects the file to contain length fields that control how much data gets written to a buffer. If an attacker puts a huge length value, but not enough real data, the application keeps writing outside its buffer—sometimes into code memory.
Arbitrary code execution: Attacker can execute code with the permissions of the current user
- Possible scenarios: Installing malware, creating backdoors, or exfiltrating sensitive information
Exploitation Requirements
It’s important to know that a user has to open the crafted file—so email phishing and malicious download links are the primary danger.
What Should You Do?
- Update Now: If you use Adobe Dimension, update to the latest version from Adobe’s website.
- Don’t Open Unknown Files: Be careful with Dimension files from untrusted sources, especially unsolicited email attachments.
References and Further Reading
- National Vulnerability Database Entry (NVD) - CVE-2023-26372
- Adobe Security Bulletin: APSB23-17 (Dimension)
- Common Weakness Enumeration (CWE-787): Out-of-bounds Write
Conclusion
CVE-2023-26372 is a dangerous out-of-bounds write bug that can let attackers take control of your PC just by tricking you into opening a malicious file with Adobe Dimension. While the exploit requires user interaction, social engineering makes this a powerful weapon in the hands of hackers. Make sure your software is up-to-date and always be cautious when handling files, especially with your creative tools.
Have questions or concerns?
Drop them in the comments or reach out on security forums—keeping the community informed helps everyone.
Timeline
Published on: 04/12/2023 20:15:00 UTC
Last modified on: 04/14/2023 03:41:00 UTC