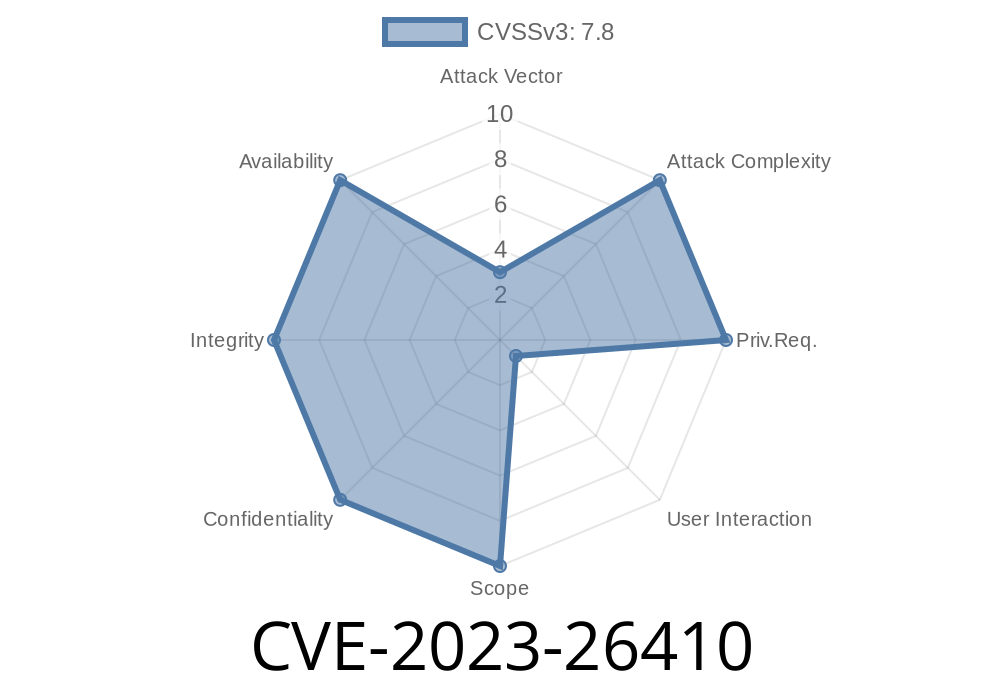
In early 2023, the cybersecurity community identified a severe vulnerability in Adobe Substance 3D Designer—designated as CVE-2023-26410. This bug is a classic "use-after-free" issue that, if exploited, allows attackers to execute any code they want as the current user by tricking them into opening a specially crafted malicious file. This post explains the flaw, walks through an example, and explores how an exploit works in the real world, using easy-to-understand language.
What’s a Use-After-Free Vulnerability?
A "use-after-free" happens when a program tries to use a chunk of memory _after_ it’s been freed (released). If an attacker can control what goes into that freed space, they can sometimes control the program, coaxing it into running their code.
Think of it like this
- You rent a storage unit (memory), fill it with your stuff (data), then cancel your lease (free the memory).
Someone else rents that same unit and puts in their things (attacker’s code).
- But you go back and, without asking, pull out something from the unit—now, it’s their stuff, not yours!
When this situation involves security-sensitive programs (like 3D Designer), it’s a serious problem.
Adobe’s Advisory
> The exploitation requires user interaction in that a victim must open a malicious file.
> — Adobe Security Bulletin APSB23-22
Here, an attacker creates a malicious .sbs file (Substance archive/graph file) that is specially crafted to trigger the bug when opened in Designer. If the attacker gets you to open their file (via phishing, a download, or a fake asset), they get to run malicious code on your system _as you_.
Technical Explanation
Adobe Substance 3D Designer processes complex scene files. If you reference or embed resources in a particular, malformed way, the program winds up freeing an object (for example, a material node) too early. However, later code tries to access that “used-to-exist” object.
If the attacker fills the heap—the area of memory where objects go—with their own data, it’s possible when the program “uses” the freed object, it will run code provided by the attacker.
Below is simplified C++-style pseudo-code to explain what’s going on under the hood
// Simplified vulnerable function:
void processMaterial(Material* mat) {
free(mat); // Oops! Mat is freed.
... // Some unrelated operations
doSomething(mat->id); // Use-after-free! mat is already freed!
}
After free(mat), the pointer mat still exists, but it points to memory that’s now up for grabs. An attacker’s malicious file can arrange things so this pointer now references their injected code.
Triggers the bug: Causes Designer to free a resource, but still references it later.
2. Heap grooming: Uses large, precisely ordered data to fill freed space with attacker-controlled payload.
Imagine the attacker fills the freed space with code that pops the calculator (calc.exe)
# Heavily simplified payload (not production code!)
malicious_data = b"\x90" * 100 # NOP sled
malicious_data += shellcode_to_launch_calc()
Part of the exploit in the malicious file would be binary data designed to become the new “object” pointed to by the dangling pointer.
The bug triggers, executing the attacker’s code.
4. Attacker now has control: they can install spyware, steal art assets, or use the victim's machine for further attacks.
Official References
- Adobe Security Bulletin APSB23-22 (CVE-2023-26410)
- NIST NVD Report for CVE-2023-26410
Be cautious of unknown .sbs files: Don’t open project files from untrusted sources.
- Run as non-admin: If possible, don’t use Designer as an administrator, since this limits what the exploit can do.
Conclusion
Use-after-free bugs like CVE-2023-26410 are dangerous because they are easy to trigger (just open a file) and let attackers fully compromise your computer. If you use Adobe Substance 3D Designer, update immediately and stick to trusted sources for your files.
Read more
- Substance 3D Designer Release Notes
- Basic Guide: Understanding Use-After-Free Vulnerabilities
Timeline
Published on: 04/13/2023 20:15:00 UTC
Last modified on: 04/14/2023 13:06:00 UTC