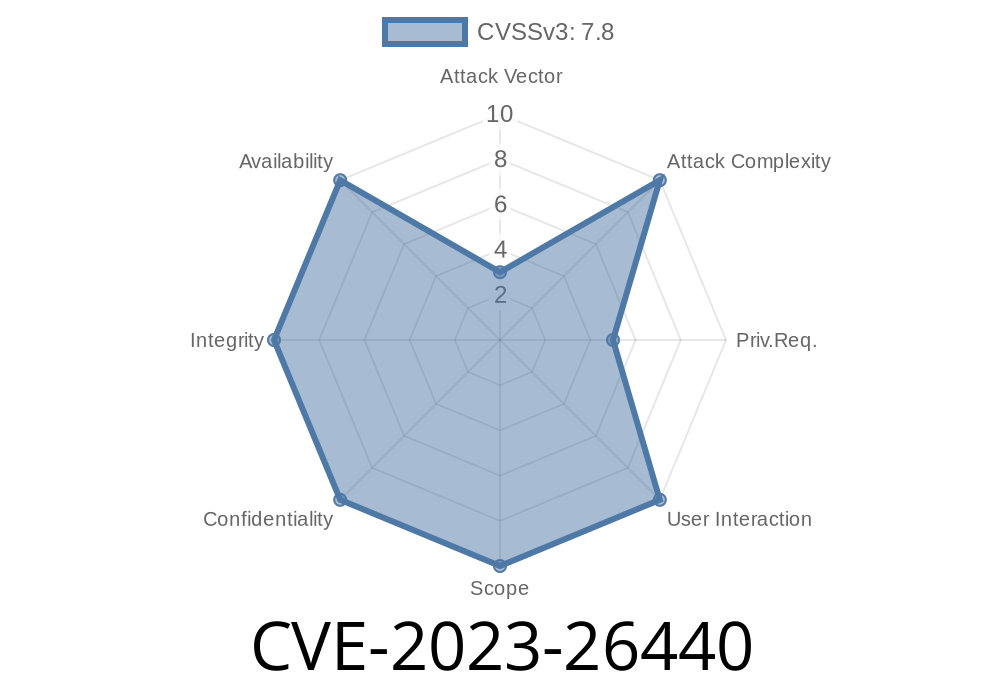
A recent security issue, CVE-2023-26440, was identified in the _cacheservice_ API, revealing how insufficient input checks led to a critical SQL injection vulnerability. This flaw allowed attackers with restricted or local network access to perform unauthorized SQL queries — and while no public exploits are known, the threat surfaced serious concerns for affected organizations.
In this exclusive overview, I’ll clearly break down what happened, show you simplified code snippets that illustrate the problem, provide links to official resources, and explain how the development team fixed the issue.
What Went Wrong? — The Heart of the Vulnerability
At the center of CVE-2023-26440 was a particular API used for cache management (_cacheservice_). This API allowed parameters to pass almost directly into SQL statements when creating cache groups. The input was not cleaned well enough, so someone could sneak in malicious SQL fragments.
What makes this bug tricky is that attackers didn’t have to touch the database directly — they could send legitimate-looking API calls containing SQL keywords or syntax. When these were processed, the server would end up running the injected SQL code.
Who Could Exploit It?
The risk was limited to users with local or restricted network access — such as someone inside your company network, a compromised service, or an attacker who found a way into a protected environment.
Simplified Code Example: How the Injection Worked
Let’s see a stripped-down version of the vulnerable code. Normally, a developer might expect the API to get a group name like new_users from the client, and use it to create a cache group:
# Vulnerable example: handling user input directly in SQL
def create_cache_group(group_name):
cursor.execute("INSERT INTO cache_groups (name) VALUES ('%s')" % group_name)
If group_name is just one word, there’s no issue. But with this bug, an attacker could call the API with:
group_name=anything'); DROP TABLE users; --
The resulting query would become
INSERT INTO cache_groups (name) VALUES ('anything'); DROP TABLE users; --')
With this, the database would try to delete your entire users table! That’s classic SQL injection.
To patch this issue, the development team made two key improvements
1. Improved input validation — All input to the API is now checked for suspicious characters or SQL keywords.
2. Safe query construction — The API now uses parameterized statements to separate data from code.
Here’s how the fixed function should look in Python (using a real SQL library for parameters)
# Patched example: using parameterized queries
def create_cache_group(group_name):
cursor.execute("INSERT INTO cache_groups (name) VALUES (%s)", (group_name,))
With this code, even if someone tries to inject SQL, it will be treated as ordinary text — not as part of the query.
Are you affected?
- If you run a version of cacheservice released before the patch in early 2023, and grant untrusted users access to it, update urgently.
Upgrade to the latest version as soon as possible. The patches are straightforward.
- Audit your API calls and network exposure — make sure sensitive APIs are not open to unnecessary users.
No Public Exploits… Yet
Although no working exploit scripts have been shared online, historical trends show that attackers often test for these issues after disclosure. Don’t wait for something to leak — apply the fix.
References & Further Reading
- Official CVE record: CVE-2023-26440
- National Vulnerability Database entry
- OWASP SQL Injection Cheat Sheet
- Stack Overflow: How to use parameterized queries
Summary
CVE-2023-26440 is a textbook example of how forgetting to sanitize and filter API input can put your applications — and your data — in serious danger. While this specific cache service API bug could only be reached from within restricted networks, the general lesson applies broadly: always treat user input as hostile, and use safe query patterns.
Timeline
Published on: 08/02/2023 13:15:00 UTC
Last modified on: 08/08/2023 18:18:00 UTC